Cisco 350-601 - Implementing Cisco Data Center Core Technologies (350-601 DCCOR)
Which Cisco Nexus Dashboard feature analyzes flow telemetry data that is streamed from a Cisco Nexus 9000 Series Switch?
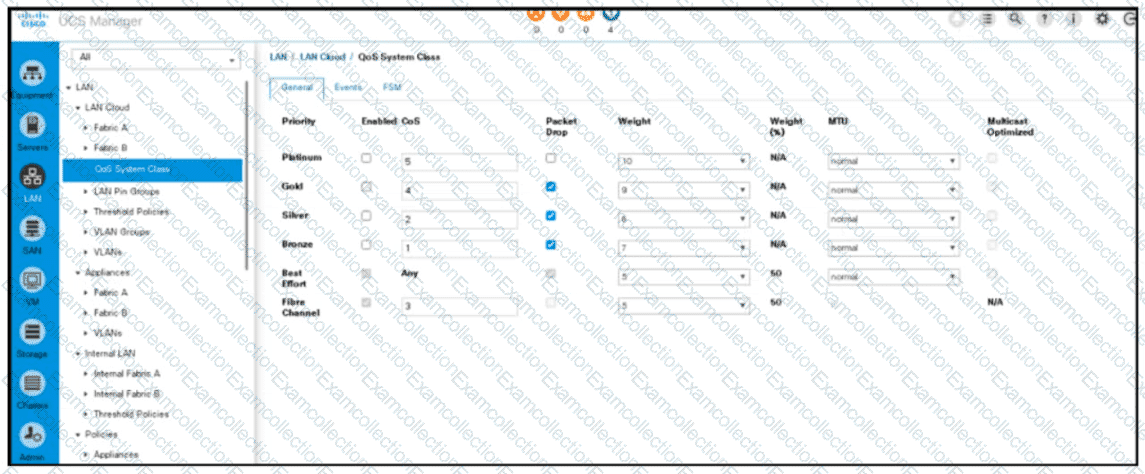
Refer to the exhibit. An engineer must configure a QoS policy that controls only vHBA traffic. Which policy must be used to meet this requirement?
What are two capabilities of the Cisco Network Assurance
Engine? (Choose two.)
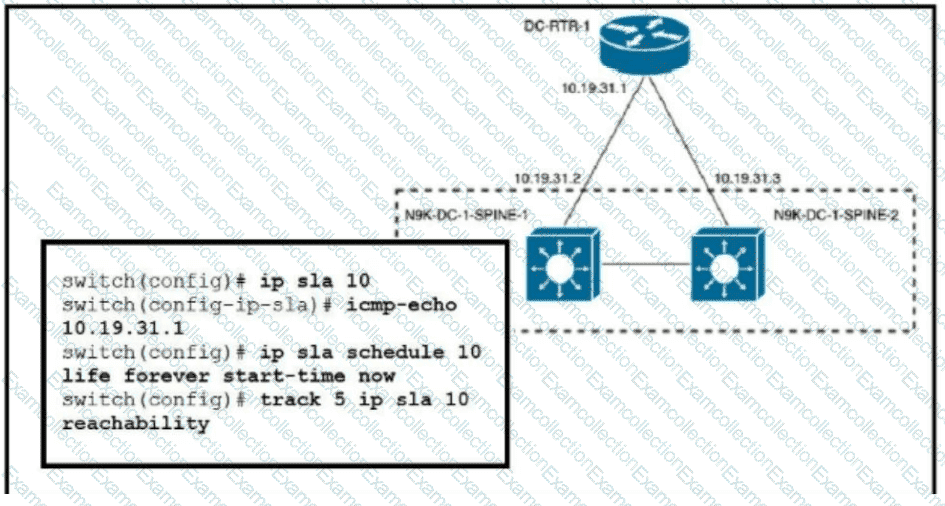
Refer to the exhibit. An engineer must invoke a Python script that alerts the operations team when the router DC-RTR-1 becomes unreachable. Which configuration set accomplishes this task?
A cisco mds 9000 series switch must automatically learn about devices and
switches connected to a fibre channel interface. However
a conflicting entry exists in the configuration database.
Which set of actions activates the configuration database?
An engineer must allow communication between the APIC controller and an OpenStack OpFlex agent. The agent Is running on a compute node directly plugged to a Cisco ACI leaf switch The engineer must enable and extend Intra VLAN on the port facing the compute and extend the Infra VLAN to the host. Which action must be taken to meet these requirements?
What is the impact of an electronic programmable logic device upgrade on a Cisco MDS 9000 Series Director Switch with dual supervisors?
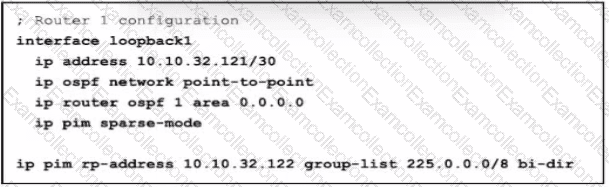
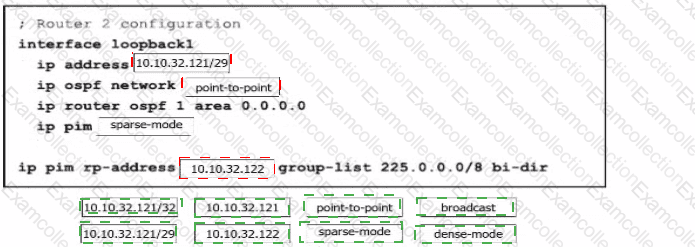
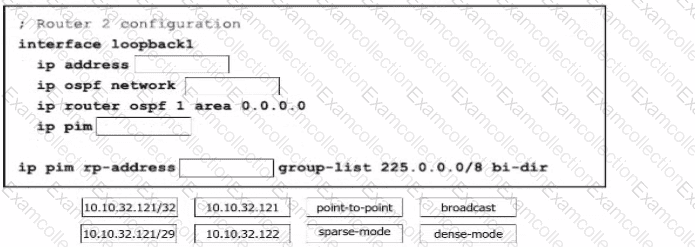
Refer to the exhibit. In a bidirectional PIM network using Phantom RP as an RP redundancy mechanism, two Cisco NX-OS routers have these requirements:
•R1 must be the active RP.
•R2 must be the backup RP that is used only if R1 is not reachable
Drag and drop the configuration steps to complete the configuration for Router 2 Not all configuration steps are used.
In a data center based on Cisco Nexus 9000 Series Switches, all endpoints support explicit congestion notifications How does the Nexus switch respond when the ECN-enabled queue reaches the maximum WRED threshold?
An engineer must back up the Cisco UCS Manager configuration to a remote server. The backup job must meet these requirements:
The backup must use the TCP protocol and be secure.
Client identification does not need to be verified before data is transmitted
The backup must contain the system configuration, including usernames, roles, and locales.
The operations team requires that the backup file is in a human-readable format.
Which set of configurations should the engineer use?