Microsoft AZ-500 - Microsoft Azure Security Technologies
You need to ensure that users can access VM0. The solution must meet the platform protection requirements.
What should you do?
You plan to implement JIT VM access. Which virtual machines will be supported?
You plan to configure Azure Disk Encryption for VM4. Which key vault can you use to store the encryption key?
From Azure Security Center, you need to deploy SecPol1.
What should you do first?
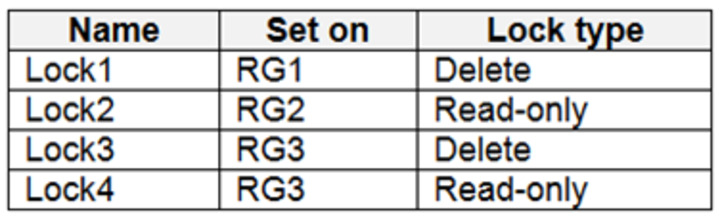
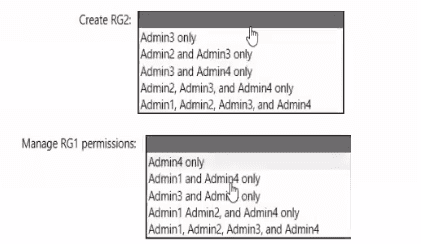
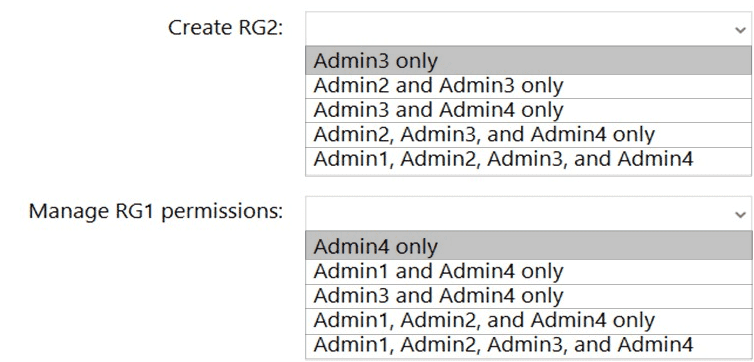
You need to delegate the creation of RG2 and the management of permissions for RG1. Which users can perform each task? To answer select the appropriate options in the answer area. NOTE: Each correct selection is worth one point
You need to configure support for Azure Sentinel notebooks to meet the technical requirements.
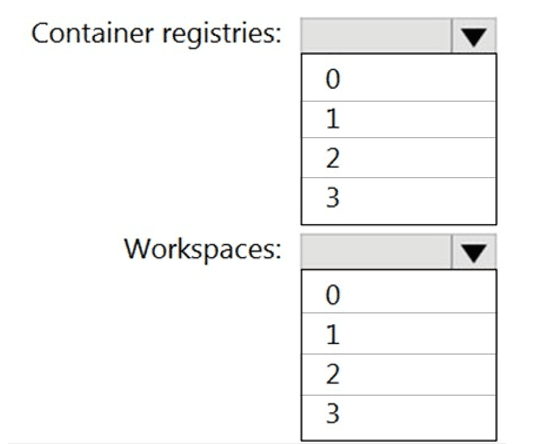
What is the minimum number of Azure container registries and Azure Machine Learning workspaces required?
You need to meet the technical requirements for VNetwork1.
What should you do first?
: 2 HOTSPOT
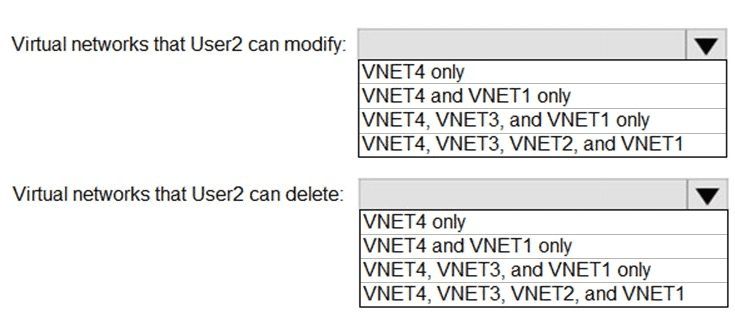
Which virtual networks in Sub1 can User2 modify and delete in their current state? To answer, select the appropriate options in the answer area.
NOTE: Each correct selection is worth one point.
You assign User8 the Owner role for RG4, RG5, and RG6.
In which resource groups can User8 create virtual networks and NSGs? To answer, select the appropriate options in the answer area.
NOTE: Each correct selection is worth one point.

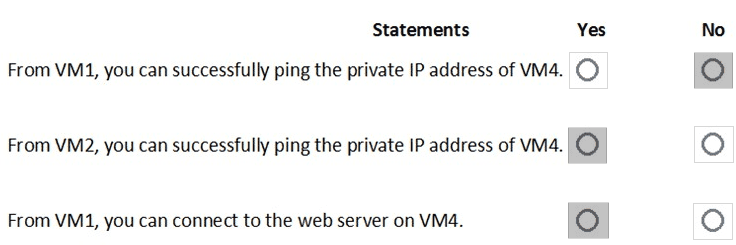
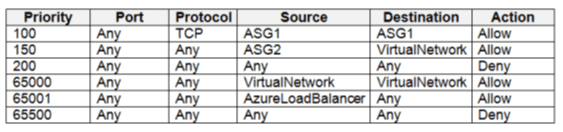
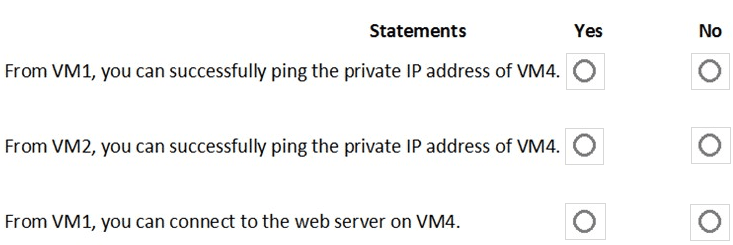
You are evaluating the effect of the application security groups on the network communication between the virtual machines in Sub2.
For each of the following statements, select Yes if the statement is true. Otherwise, select No.
NOTE: Each correct selection is worth one point.




 Graphical user interface, text, application, chat or text message Description automatically generated
Graphical user interface, text, application, chat or text message Description automatically generated
 Table Description automatically generated with medium confidence
Table Description automatically generated with medium confidence