ISC CC - CC - Certified in Cybersecurity
A company’s servers are down due to malware. What is the FIRST step the DR team should take?
Representation of data at OSI Layer 3 is called a:
After an earthquake disrupts business operations, which document contains the reactive procedures required to return business to normal operations?
Which fire suppression system is more friendly to electronics?
A measure of the degree to which an organization depends on information or systems to achieve its mission is called:
How does IPSec protect against replay attacks?
What is the primary goal of an incident management team?
Firewalls operate at which OSI layers?
Exhibit.
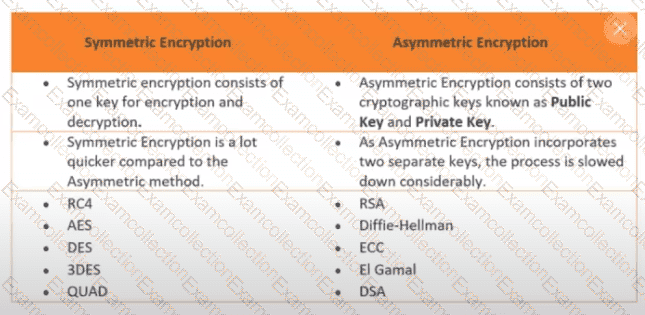
How many keys would be required to support 50 users in an asymmetric cryptography system?
Ensuring a process cannot be completed by a single person is known as:



