CompTIA DS0-001 - CompTIA DataSys+ Certification Exam
(Which of the following statements is TRUNCATE an example of?)
Which of the following constraints is used to enforce referential integrity?
A DBA is reviewing the following logs to determine the current data backup plan for a primary data server:
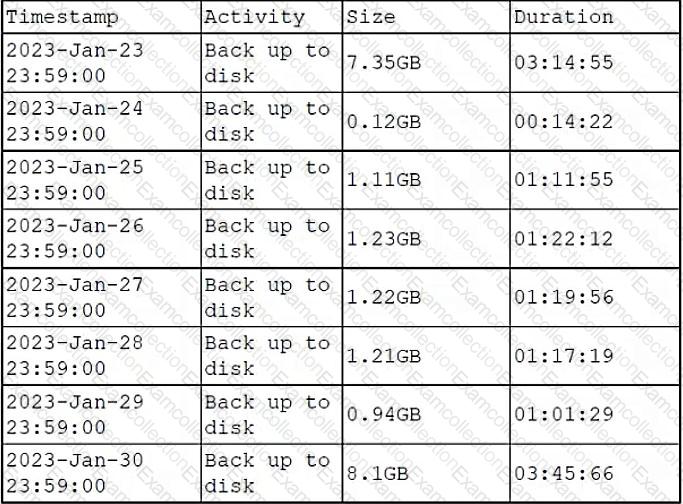
Which of the following best describes this backup plan?
(A developer needs to integrate a trigger to execute an action in a database. Which of the following SQL snippets is a correct use of a trigger?)
Which of the following sets the age requirement for data that should be recovered after a major disaster?
A company wants to deploy a new application that will distribute the workload to five different database instances. The database administrator needs to ensure that, for each copy of the database, users are able to read and write data that will be synchronized across all of the instances.
Which of the following should the administrator use to achieve this objective?
(An IT manager needs to create a workflow for a new application. Which of the following tools should the manager use to facilitate the creation of a workflow?)
A database administrator needs to ensure that a newly installed corporate business intelligence application can access the company’s transactional data. Which of the following tasks should the administrator perform first?
(New users at a company are reporting that the system is not accepting new credentials when the users are asked to change the credentials for the first time. Which of the following is the reason the credentials are being rejected?)
A database administrator needs to provide access to data from two different tables to multiple group users in order to facilitate ongoing reporting. However, some columns in each table are restricted, and users should not be able to see the values in these columns.
Which of the following is the best action for the administrator to take?



