GIAC G2700 - GIAC Certified ISO-2700 Specialist Practice Test
Which of the following is used to shift the impact of a threat to a third party, together with the ownership of the response?
You work as an Information Security Manager for uCertify Inc. You need to create the documentation on information security management system (ISMS). Which of the following elements are included in ISMS?
Each correct answer represents a complete solution. Choose all that apply.
Sam works as the Network Administrator for uCertify Inc. The information of a sensitive nature is processed. The highest-level security measures are to be implemented by management. What is this kind of risk strategy called?
What is the order of the steps in the incident cycle?
You work as a Security Administrator for uCertify Inc. You are responsible for securing the network of the organization. While checking your network log files, you find that someone is sending too many data packets over a long period of time. These data packets are difficult to be detected by IDS. Which of the following types of attacks is this?
As per a password policy, which of the following rules should be followed by a user while creating a password?
Each correct answer represents a complete solution. Choose all that apply.
Which of the following is a technique for a threat, which creates changes to the project management plan?
Mark is the project manager of the HAR Project. The project is scheduled to last for eighteen months and six months already passed. Management asks Mark that how often the project team is participating in the risk reassessment of this project. What should Mark tell management if he is following the best practices for risk management?
What are the basic steps involved in Continuity Management?
1. Prioritizing the businesses to be recovered by conducting a Business Impact Analysis (BIA).
2. Performing a Risk Assessment (aka Risk Analysis) for each of the IT Services to identify the assets, threats, vulnerabilities, and countermeasures for each service.
3. Evaluating the options for recovery.
4. Producing the Contingency Plan.
5. Testing, reviewing, and revising the plan on a regular basis.
Each correct answer represents a complete solution. Choose two.
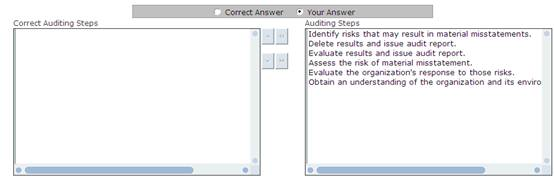
You work as a Network Auditor for Net Perfect Inc. The company has a Windows-based network. You need to audit the network of the company. You need to plan the audit process to minimize the audit risk.
What steps will you take to minimize the possibility of audit risk?