GIAC G2700 - GIAC Certified ISO-2700 Specialist Practice Test
Mark is hired as an Information Security Officer for BlueWell Inc. He wants to draw the attention of the management towards the significance of integrating information security in the business processes.
Which of the following tasks should he perform first to accomplish the task?
Which of the following types of social engineering attacks is a term that refers to going through someone's trash to find out useful or confidential information?
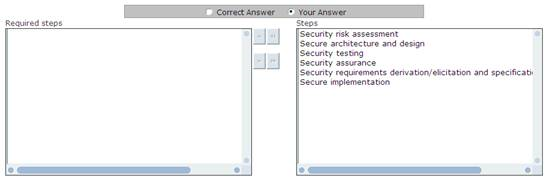
Cigital Risk Management Method was developed by Gary McGraw of Cigital and John Viega of Stonewall Software, and it defines software security risk management process. Choose and re-order the risk management steps that are included in this method.
Which of the following is expressly set up to attract and trap people who attempt to penetrate other people's computer systems?
Which of the following are the perspectives considered to ensure the confidentiality, integrity, and availability of an organization's assets, information, data, and IT services?
Each correct answer represents a complete solution. Choose all that apply.
You work as an Information Security Manager for uCertify Inc. You are working on asset management. You need to differentiate various assets of your organization. Which of the following are information assets?
Each correct answer represents a complete solution. Choose all that apply.
Which of the following are the two methods that are commonly used for applying mandatory access control?
Each correct answer represents a complete solution. Choose all that apply.
You work as an Information Security Manager for uCertify Inc. You are working on the documentation of control A.10.1.1. What is the purpose of control A.10.1.1?
Which of the following statements is correct about the Annual Loss Expectancy?
Which of the following information security standards deals with the protection of the computer facilities?



