GIAC GSNA - GIAC Systems and Network Auditor
What does a firewall check to prevent certain ports and applications from getting the packets into an Enterprise?
Which of the following methods is used to get a cookie from a client? Note: Here, request is a reference of type HttpServletRequest, and response is a reference of type HttpServletResponse.
You have been assigned a project to develop a Web site for a construction company. You have to develop a Web site and want to get more control over the appearance and presentation of your Web pages. You also want to increase the ability to precisely specify the location and appearance of the elements on a page and create special effects. You plan to use Cascading style sheets (CSS). You want to apply the same style consistently throughout your Web site. Which type of style sheet will you use?
Which of the following methods will free up bandwidth in a Wireless LAN (WLAN)?
In which of the following social engineering attacks does an attacker first damage any part of the target's equipment and then advertise himself as an authorized person who can help fix the problem.
You work as a Security Administrator in Tech Perfect Inc. The company has a TCP/IP based network. The network has a vast majority of Cisco Systems routers and Cisco network switches. You have mplemented four VPN connections in the network. You use the Cisco IOS on the network. Which feature will you enable to maintain a separate routing and forwarding table for each VPN?
You work as a Network Administrator for XYZ CORP. The company's Windows 2000 network is configured with Internet Security and Acceleration (ISA) Server 2000. ISA Server is configured as follows: The server uses the default site and content rule and default IP packet filters. Packet filtering is enabled. The server has two protocol rules:
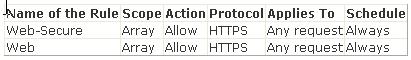
Users in the network complain that they are unable to access secure Web sites. However, they are able to connect to Web sites in which secure transmission is not required. What is the most likely cause?
You work as the Network Administrator for XYZ CORP. The company has a Unix-based network. You want to impose some special access restrictions on users. Which of the following Unix configuration files can you use to accomplish the task?
You configure a wireless router at your home. To secure your home Wireless LAN (WLAN), you implement WEP. Now you want to connect your client computer to the WLAN. Which of the following is the required information that you will need to configure the client computer? (Choose two)
You work as a Database Administrator for Dolliver Inc. The company uses Oracle 11g as its database. You have used the LogMiner feature for auditing purposes. Which of the following files store a copy of the data dictionary? (Choose two)



