GIAC GSSP-.NET - GIAC GIAC Secure Software Programmer - C#.NET
You work as a Software Developer for Webtech Inc. You plan to migrate the existing Active Server Pages (ASP) pages to ASP.NET Web pages in order to implement rich functionalities of a Web browser in your Web pages. Therefore, you want to add controls to Web pages of your existing application named WebApp1. Which of the following controls will be most suitable to implement?
Which of the following is the best encryption algorithm to encrypt and decrypt messages?
You work as an Application Developer for ABC Inc. You are assigned with developing a Web site that will handle information related to monthly sales of the company. You wish to secure the Web site so that only employees of the Accounts department can view the Web pages. You need to create roles for the employees of this department. The user account information will be stored in a SQL Server database named Database. You decide to do all this by using the Web Site Administration Tool. Which of the following types of security will you use to accomplish the task?
You work as a Web Application Developer for SunInfo Inc. The company uses Visual Studio 2008 as its application development platform. You create a Web application using .NET Framework 3.5. You want to ensure that when an unhandled exception occurs on the site, a custom error page errorpage.aspx is displayed. Also, you want to ensure that when the HTTP 500 error occurs, the servererror.aspx page is displayed. Which of the following settings will you add inside the system.web section of the Web.config file to accomplish the task?
You work as a Software Developer for ABC Inc. The company uses Visual Studio .NET 2008 as its application development platform. You create an ASP.NET Web application using .NET Framework 3.5. You create a Web form in the application that permits users to provide personal information. You add a DropDownList control to the Web form to retrieve the residential status of users. The default item that the DropDownList control displays is the "Select Country" option. You have to ensure that users select a country other than the default option. Which of the following validation controls should you use to accomplish this task?
Which of the following data structures is used for storing reference data types?
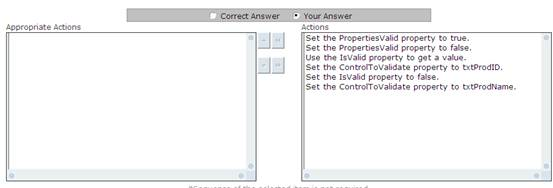
Peter works as a Software Developer for NessCom Inc. He creates a Web application named WebApp using Visual Studio .NET. WebApp contains an .aspx page named DataValidatePage.aspx, which has several Web server controls. Two TextBox controls, txtProdID and txtProdName, are used. The txtProdID control is used to enter the identification number of the products used by the company. The txtProdName control is used to enter valid product names. Peter wants to ensure that only valid data is entered in these two TextBox controls. Therefore, he implements a RequiredFieldValidator class in the DataValidatePage.aspx page. Choose the appropriate actions Peter will perform to accomplish the task.
You work as an Application Developer for ABC Inc. You are assigned with developing a Web site that will handle information related to monthly sales of the company. You wish to secure the Web site so that only employees of the Accounts department can view the Web pages. You need to create roles for the employees of this department. The user account information will be stored in a SQL Server database named Database. You decide to do all this by using the Web Site Administration Tool. Which of the following types of security will you use to accomplish the task?
You work as a Software Developer for Mansoft Inc. You create an application and use it to create code access security policies. Which of the following tools will you use to examine and modify code access security policies from a batch file?
You work as a Software Developer for ABC Inc. The company uses Visual Studio.NET 2005 as its application development platform. You create a Web service using .NET Framework 2.0. You want the Web service to utilize a two step process to map XML generated by Web methods to .NET objects. What will you do to accomplish the task?
Each correct answer represents a part of the solution. Choose two.



