Huawei H12-891_V1.0 - HCIE-Datacom V1.0
In the LDP session establishment process, the initiator sends an Initialization message for parameter negotiation. Which message will be sent by the responder if it does not accept negotiation parameters?
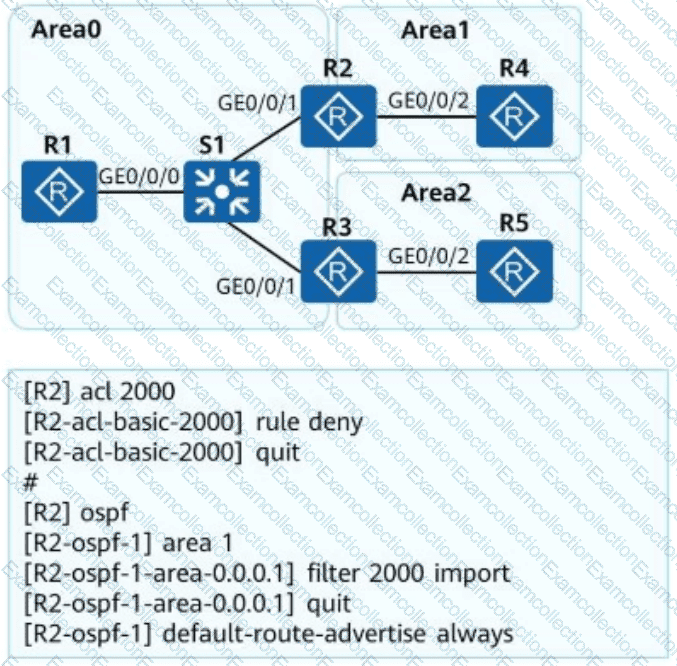
OSPF is deployed on a campus network to implement network interconnection. An engineer configures R2 as shown in the figure. Which of the following statements is incorrect about LSAs on the OSPF network?
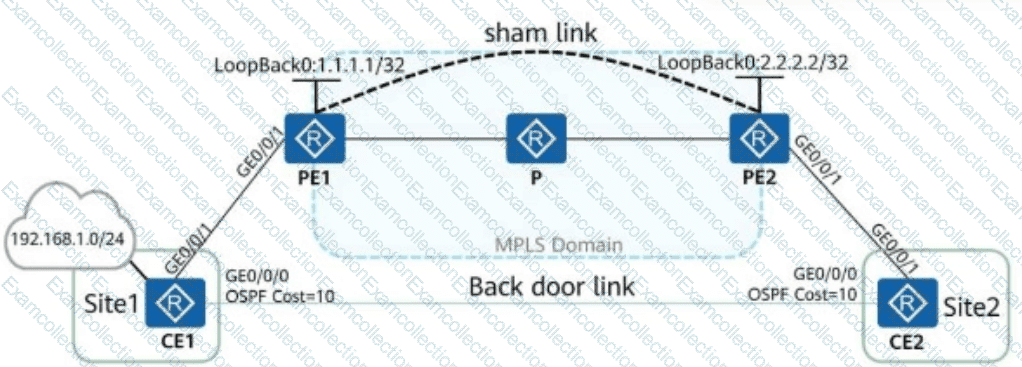
As shown in the figure, a sham link is established between PE1 and PE2 through the loopback interfaces. CE2 can learn the 192.168.1.0/24 route (directed route on CE1) through the sham link and backdoor link. If other parameters use their default settings, the cost of the 192.168.1.0/24 route on CE2 should be ______. (Enter an Arabic numeral without symbols.)
In an MPLS domain, LSRs can be classified into ingress, transit, and egress LSRs based on how they process data. For the same FEC, an LSR can be both an ingress and a transit LSR of the FEC.
NAFTIR policing can only be applied to the inbound direction. Its purpose is to monitor the traffic entering the device and ensure that the upstream device does not unnecessarily consume network resources.
When an SSH client logs in to an SSH server that is configured only with username and password authentication in SSH mode, the key exchange phase is not involved (no key is generated).
In a scenario where SR Policies are dynamically established through the controller, which of the following statements about the SR Policy solution architecture is incorrect?
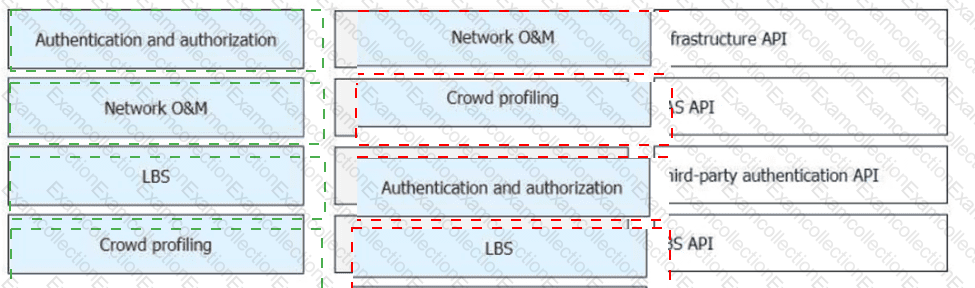
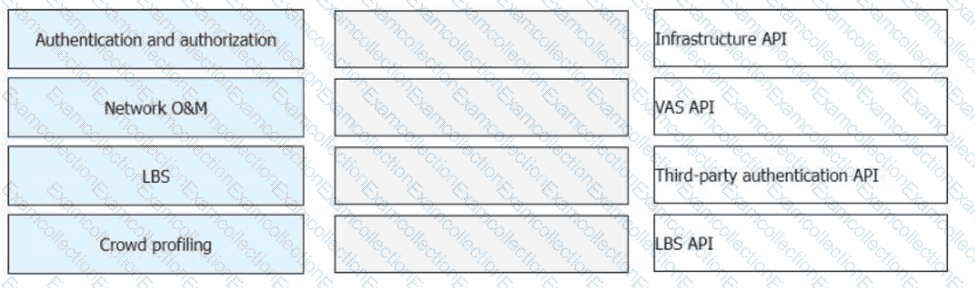
Huawei CloudCampus Solution has multiple application scenarios, and iMaster NCE-Campus provides different APIs for each application scenario. Match the following application scenarios with the open APIs provided by iMaster NCE-Campus.
Telemetry is a technology that remotely collects data from physical or virtual devices at high speed, and has a layered protocol stack. Which of the following layers is not included in the telemetry protocol stack?
What can be determined from the following IS-IS peer output?
Peer information for ISIS(1):
Peer System ID: ee8c.a0c2.baf3
Interface: GE0/0/0
State: Up
HoldTime: 7s
Type: L1
PRI: 64
MT IDs supported: 0(UP), 2(UP)
Local MT IDs: 0, 2
Area Address(es): 49.0022
Peer IP Address(es): 10.1.34.1
Peer IPv6 Address(es): FE80::2E0:FCFF:FE98:2576