Microsoft MS-900 - Microsoft 365 Fundamentals
A company is evaluating Microsoft 365.
You need to determine me deployment methods for Microsoft 365 Apps Which two tools can you use? Each correct answer presents a complete solution NOTE: Each correct selection is worth one point.
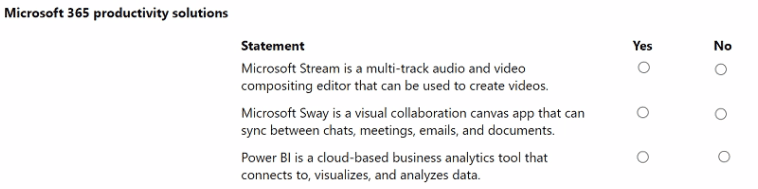
A company plans to implement Microsoft 365 productivity apps.
For each of the following statements, select Yes if the statement is true. Otherwise, select No.
NOTE: Each correctselection is worth one point.
A company is evaluating Microsoft Entra capabilities.
You need to identify a type of service principal in Microsoft Entra.
Which type can you use?
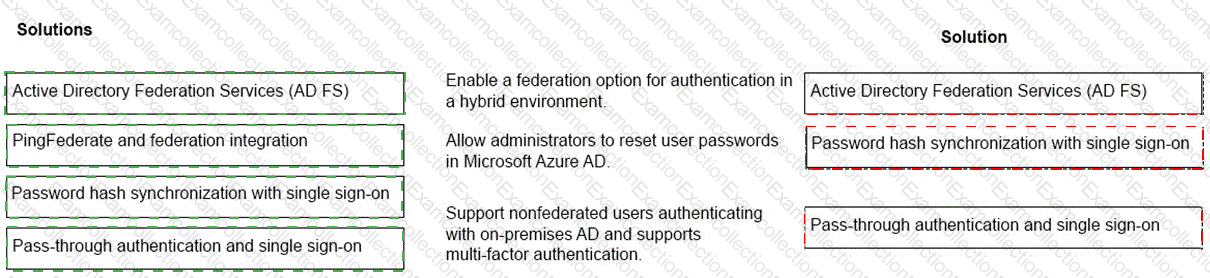
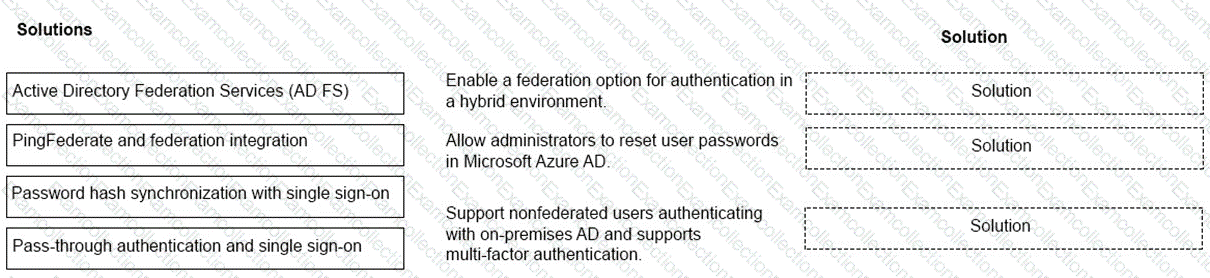
An organization plans to deploy Microsoft 365 in a hybrid scenario.
You need to provide a recommendation based on some common identity and access management scenarios. The solution must minimize costs.
Match each solution to its appropriate scenario. To answer, drag the appropriate solutions from the column on the left to the scenarios on the right. Each solution may be used once, more than once, or not at all. Each correct match is worth one point.
NOTE: Each correct selection is worth one point.
You are the Microsoft 365 administrator for an organization.
A group of employees and users outside the company must be ableto collaborate on a project in real time by using a whiteboard.
In the Microsoft 365 admin portal, which Office 365 product should you configure?
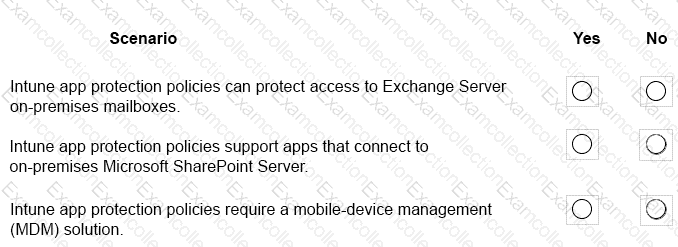
Acompany plans to deploy Microsoft Intune.
Which scenarios can you implement by using Intune? To answer, select the appropriate answer for the given scenarios.
NOTE:Each correct selection is worth one point.
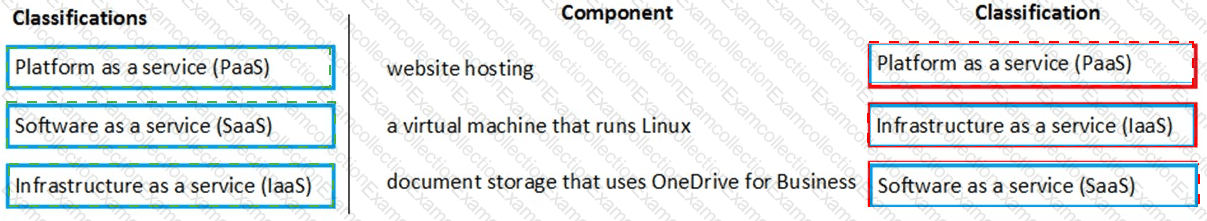
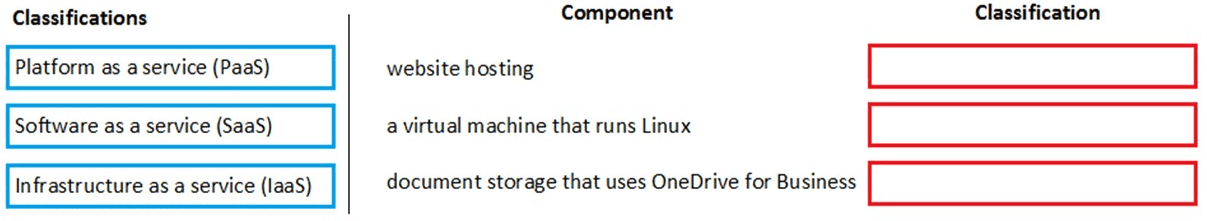
An organization is moving toMicrosoft Azure and Microsoft 365.
You need to classify the following components:
website hosting
a virtual machine that runs Linux
document storage that uses OneDrive for Business
Match each component to its classification. To answer, drag the appropriate components from the column on the left to its classifications on the right. Each component may be used once, more than once, or not at all.
NOTE:Each correct selection is worth one point.
An organization plans to deploy Microsoft Office 2019 of Office 365 ProPlus.
What are two advantages of Office 365 ProPlus? Each correct answer presents a complete solution.
NOTE: Each correct selection is worth one point
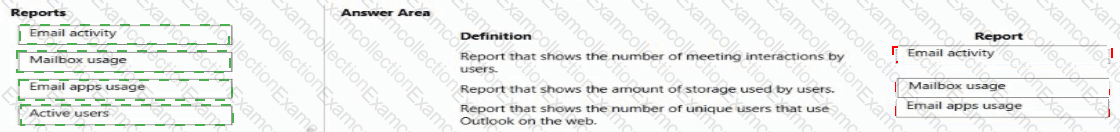
A company is using Microsoft cloud services.
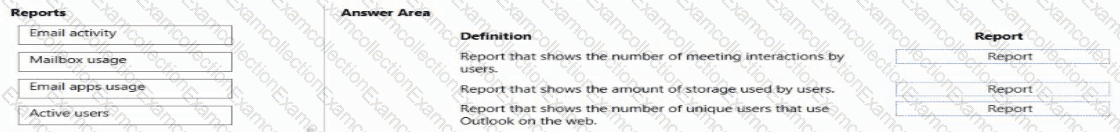
You need to select the correct reports in the Microsoft 365 admin center.
Match each report to its definition. Each report may be used once, more than once, or not at all.
NOTE: Each correct match is worth one point.
A company uses Microsoft 365 to track progress 3nd issues for construction projects.
Project tasks must be tracked within aMicrosoft-maintained unified interface that can be shared and updated across multiple users.
You need to recommend a solution for the company.
What should you recommend?