CompTIA N10-009 - CompTIA Network+ Certification Exam
A network administrator needs to divide a Class B network into four equal subnets, each with a host range of 1,000 hosts. Which of the following subnet masks should the administrator use?
After extremely high temperatures cause a power outage, the servers automatically shut down, even though the UPSs for the servers still have hours of battery life. Which of the following should a technician recommend?
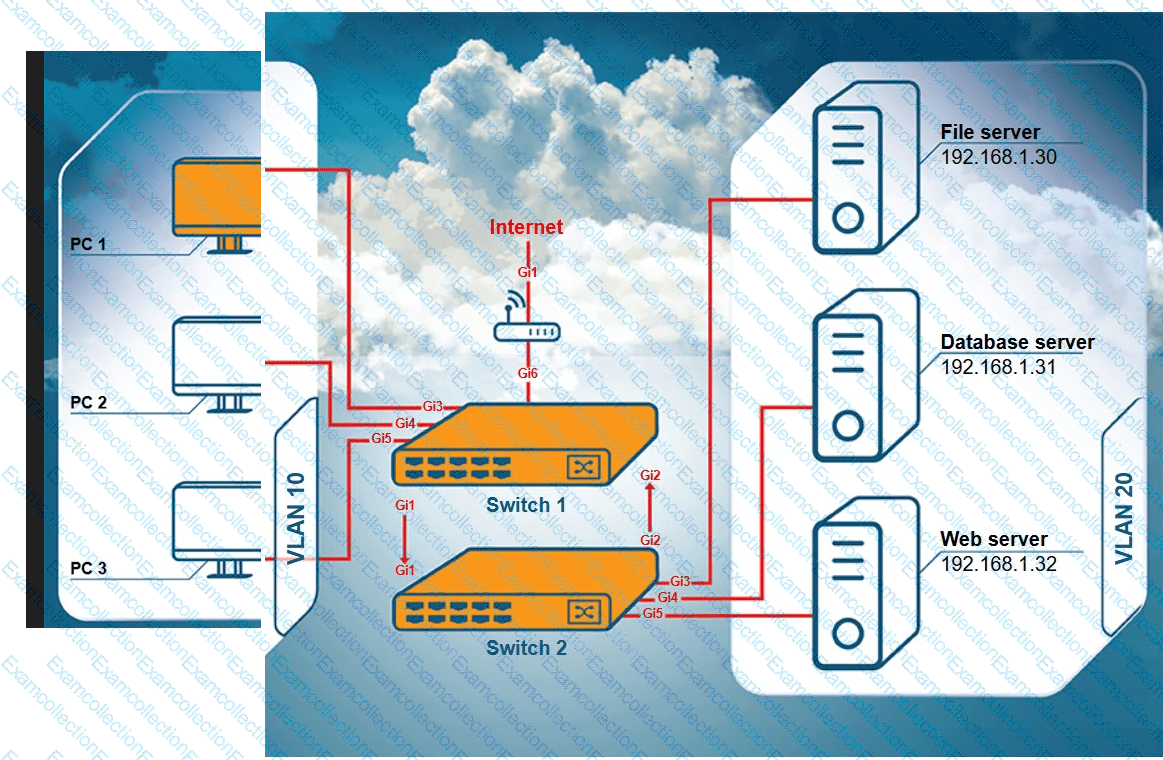
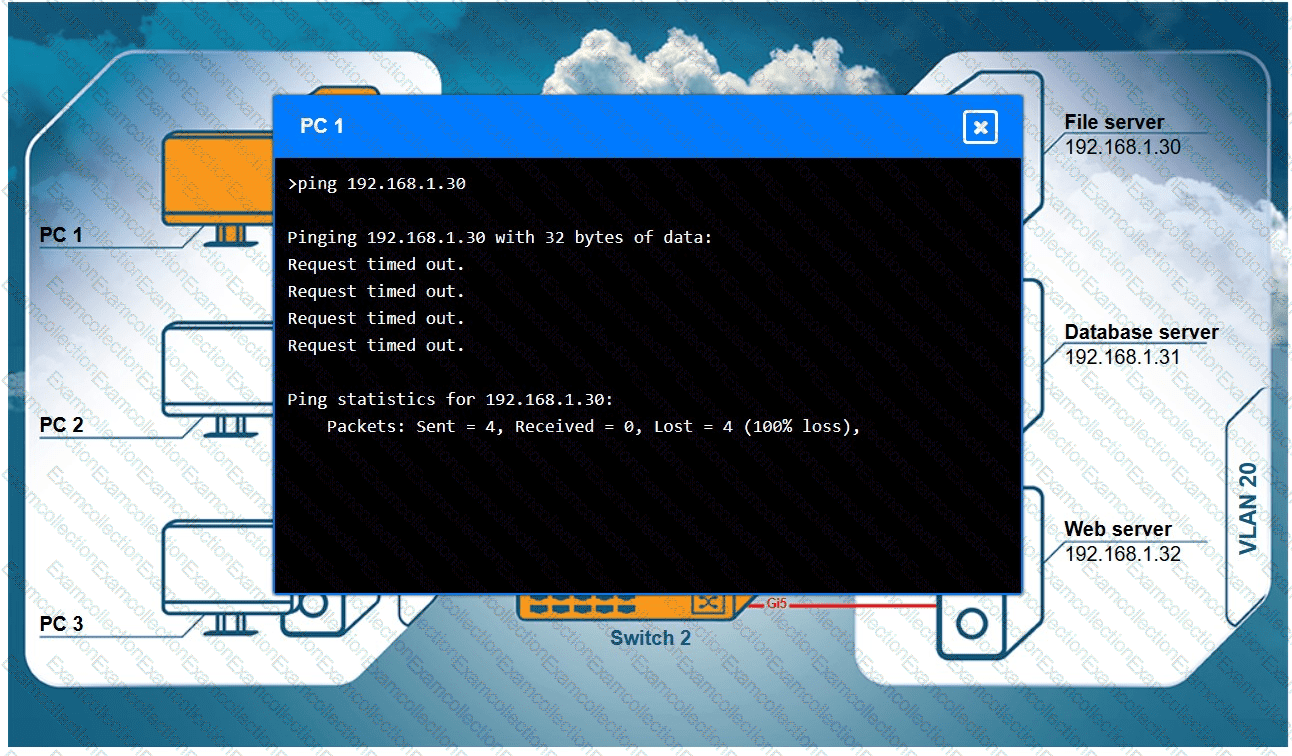
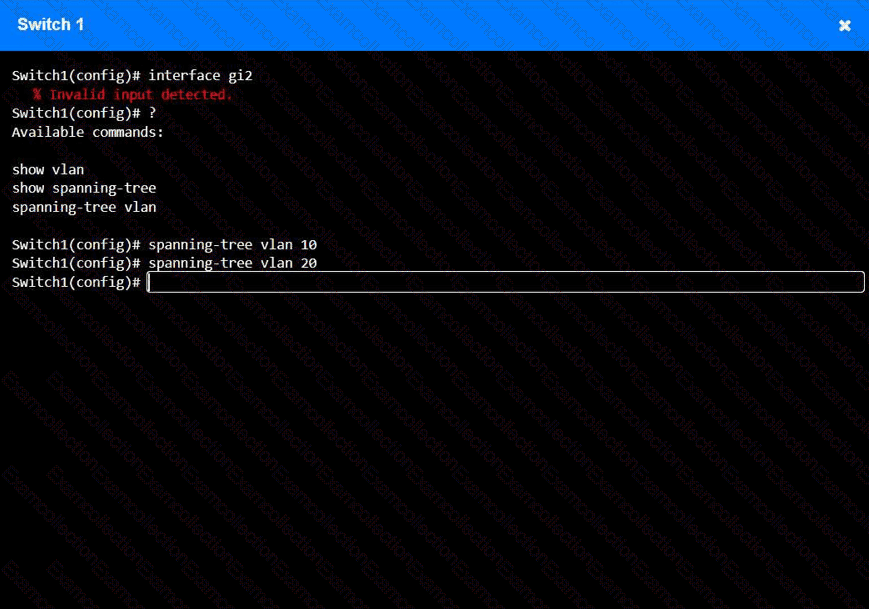
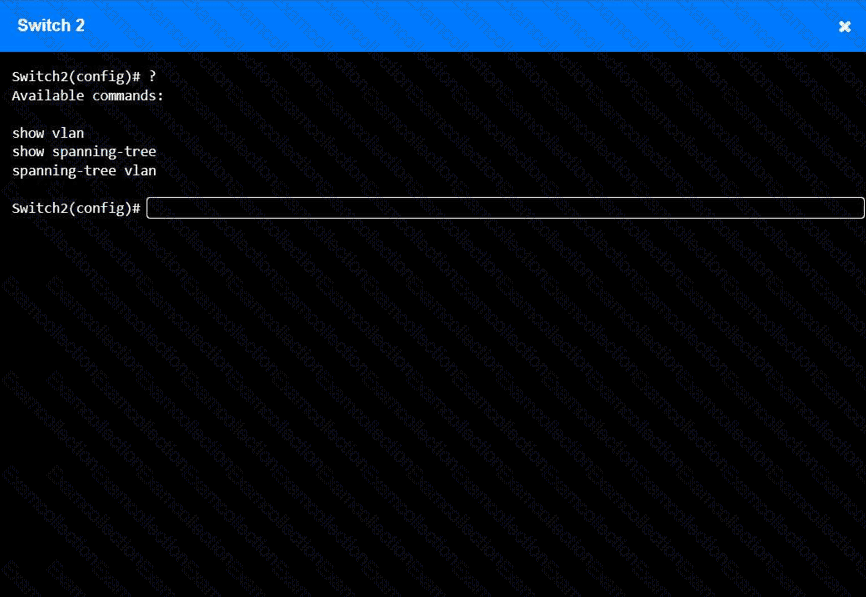
A network technician receives a ticket from an employee who is working on PC 1 but is unable to connect to the database server. The technician pings the database server from PC 1, but the request times out. After reviewing the utilization of Switch 1 and Switch 2, the technician finds high CPU utilization and sees that the MAC table is continuously changing.
INSTRUCTIONS
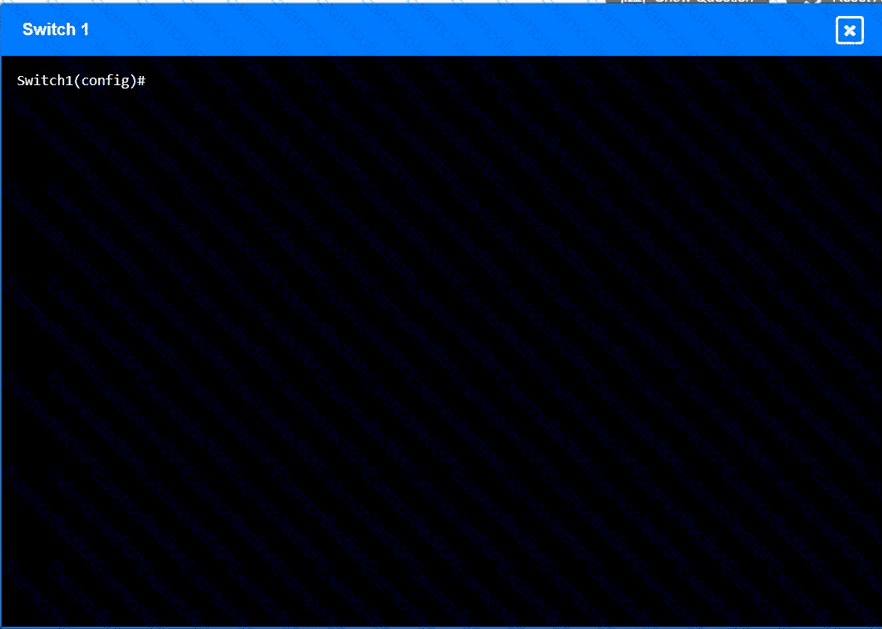
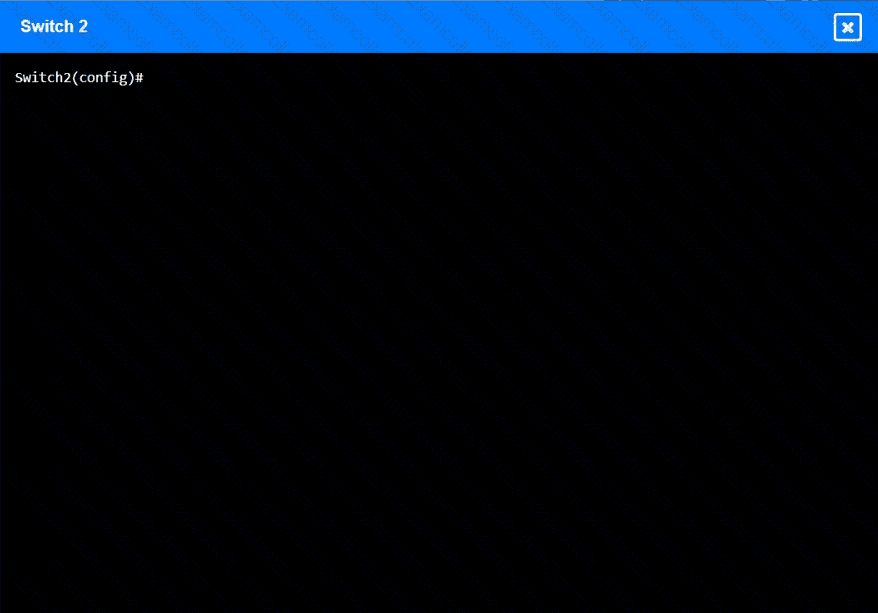
Configure Switch 1 and Switch 2 to remediate the employee ' s issue. Then, validate connectivity between PC 1 and the database server.
Switch 1 and Switch 2 are already in configuration mode. Type help to view a list of available commands.
Which of the following best describes the amount of time between a disruptive event and the point that affected resources need to be back to fully functional status?
An organization has four departments that each need access to different resources that do not overlap. Which of the following should a technician configure in order to implement and assign an ACL?
An administrator is troubleshooting a Layer 3 communication issue between the web server and the database server. The administrator finds the following information:
Device
IP
Subnet
Gateway
Firewall
192.168.1.1
255.255.255.0
1.2.3.4
Web server
192.168.1.50
255.255.255.0
192.168.1.1
Database server
192.168.1.201
255.255.255.128
192.168.1.1
Which of the following corrects the communication issue?
A network administrator configures a new network discovery tool and is concerned that it might disrupt business operations. Which of the following scan types should the administrator configure?
Which of the following ports is a secure protocol?
A network technician is examining the configuration on an access port and notices more than one VLAN has been set. Which of the following best describes how the port is configured?
A technician needs to set up a wireless connection that utilizes MIMO on non-overlapping channels. Which of the following would be the best choice?
A technician is planning an equipment installation into a rack in a data center that practices hot aisle/cold aisle ventilation. Which of the following directions should the equipment exhaust face when installed in the rack?
A network administrator needs a solution to isolate and potentially identify any threat actors that are attempting to breach the network. Which of the following should the administrator implement to determine the type of attack used?
Which of the following types of routes takes precedence when building a routing table for a given subnet?
An organization has a security requirement that all network connections can be traced back to a user. A network administrator needs to identify a solution to implement on the wireless network. Which of the following is the best solution?
A network engineer discovers network traffic that is sending confidential information to an unauthorized and unknown destination. Which of the following best describes the cause of this network traffic?



