Nutanix NCP-NS-7.5 - Nutanix Certified Professional - Network and Security (NCP-NS) 7.5
Users have recently reported intermittent connectivity issues and slower-than-usual application performance for a Nutanix cluster to an administrator. The administrator needs to identify the root cause of these issues by analyzing the health of the infrastructure components. What action should the administrator take first to diagnose the root cause of the problem?
When cloning a Flow Network Security policy, what should be verified before enabling Enforce mode?
In a Nutanix deployment, when is the Network Controller automatically enabled?
What happens when a monitored policy is enforced?
A junior network operator is assigned two predefined roles in Prism Central... Role A: Prism Viewer Role B: VPC Admin The operator reports being able to successfully create, update, and delete Virtual Private Clouds (VPCs). However, the operator is unable to create a VM into the VPC. How does Prism Central determine the operator's effective permissions?
Which policy mode blocks all traffic that is not explicitly allowed by the policy?
An administrator wants to configure the subnet 10.1.1.0/24 to stretch across two VPCs over a Network Gateway in VXLAN mode. The VMs on this subnet need to communicate with a traffic pattern of size 2000 Bytes. What is the minimum MTU required in the underlay network to ensure communication happens without fragmentation or traffic drops?
An administrator is designing a Transit VPC to provide shared corporate services (e.g., DNS) for two tenant VPCs: VPC-A requires WAN access using NAT. VPC-B requires WAN access without NAT. Both VPCs connect to the Transit VPC for shared services hosted on the corporate network. Shared services residing in the Transit VPC use routed IP addressing for WAN connectivity. Which two configuration elements should the administrator implement on the Transit VPC? (Choose two.)
An administrator observes a Network Controller Unreachable alert in Prism Central for a specific AHV cluster. All other management tasks for the cluster from Prism Central are succeeding and the cluster itself reports a healthy status. Which step is the most appropriate to investigate the cause of this specific alert?
Exhibit:
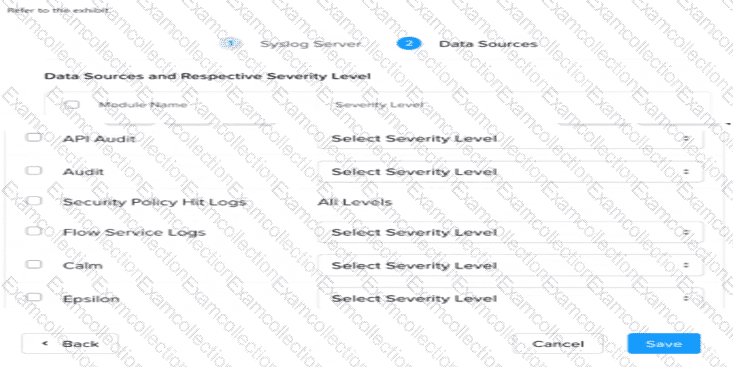
An administrator needs to setup a Syslog server to capture the Flow Network Security Hit logs. Which module name should be selected?



