CompTIA PT0-002 - CompTIA PenTest+ Certification Exam
A penetration tester opened a reverse shell on a Linux web server and successfully escalated privileges to root. During the engagement, the tester noticed that another user logged in frequently as root to perform work tasks. To avoid disrupting this user’s work, which of the following is the BEST option for the penetration tester to maintain root-level persistence on this server during the test?
A security analyst needs to perform an on-path attack on BLE smart devices. Which of the following tools would be BEST suited to accomplish this task?
Penetration tester who was exclusively authorized to conduct a physical assessment noticed there were no cameras pointed at the dumpster for company. The penetration tester returned at night and collected garbage that contained receipts for recently purchased networking :. The models of equipment purchased are vulnerable to attack. Which of the following is the most likely next step for the penetration?
Which of the following BEST explains why a penetration tester cannot scan a server that was previously scanned successfully?
The following output is from reconnaissance on a public-facing banking website:
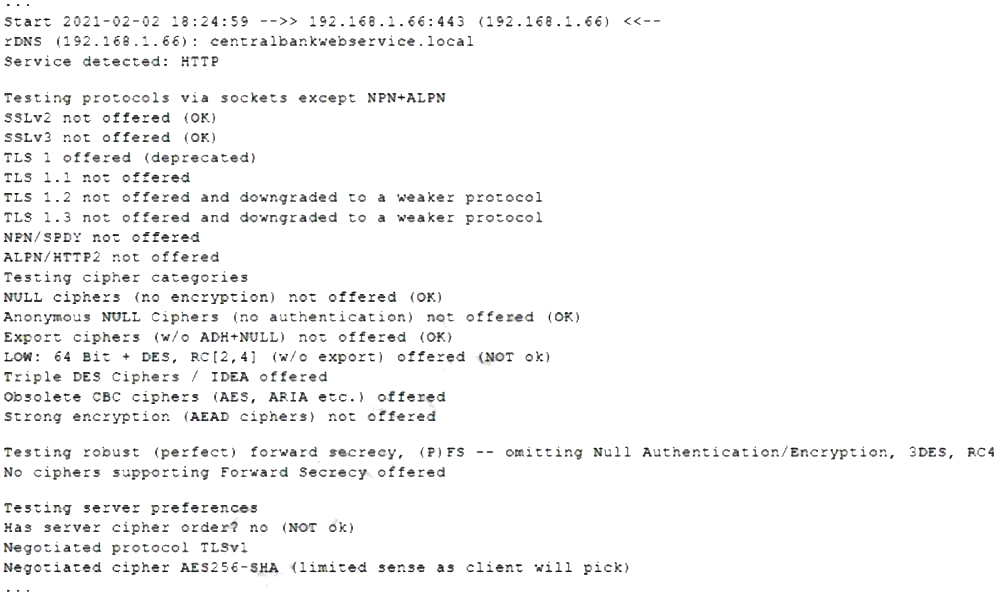
Based on these results, which of the following attacks is MOST likely to succeed?
Which of the following situations would require a penetration tester to notify the emergency contact for the engagement?
Which of the following concepts defines the specific set of steps and approaches that are conducted during a penetration test?
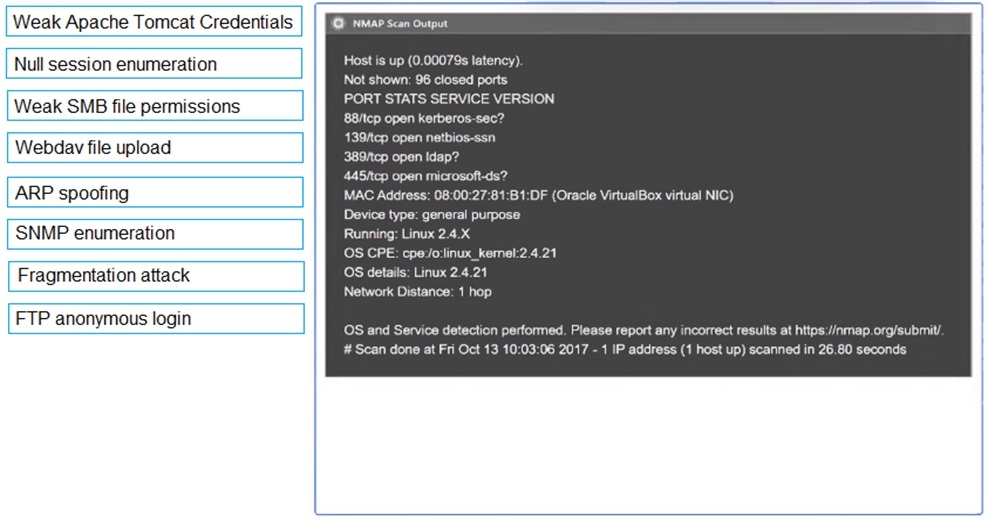
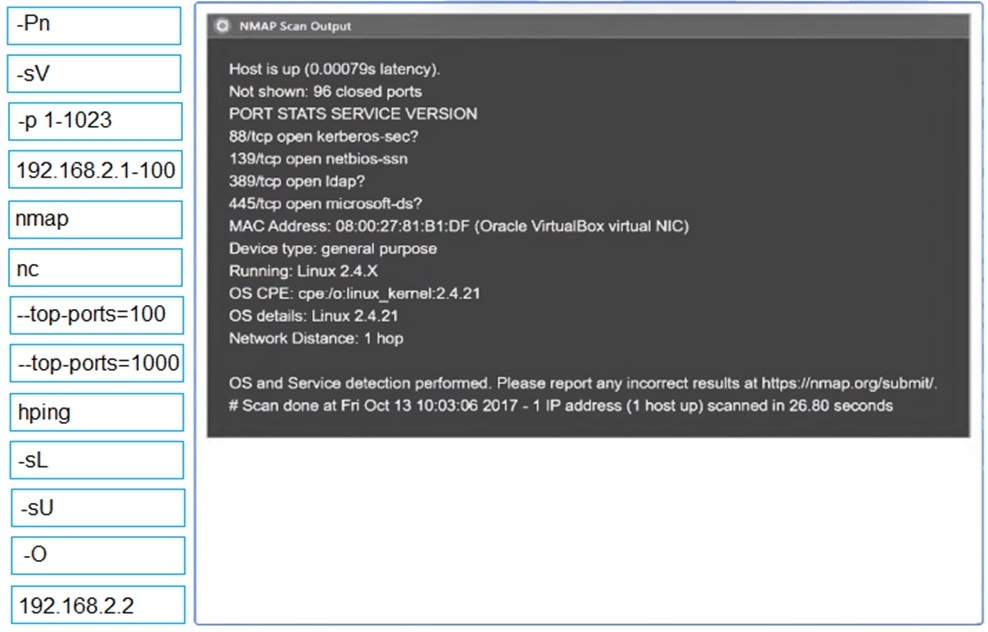
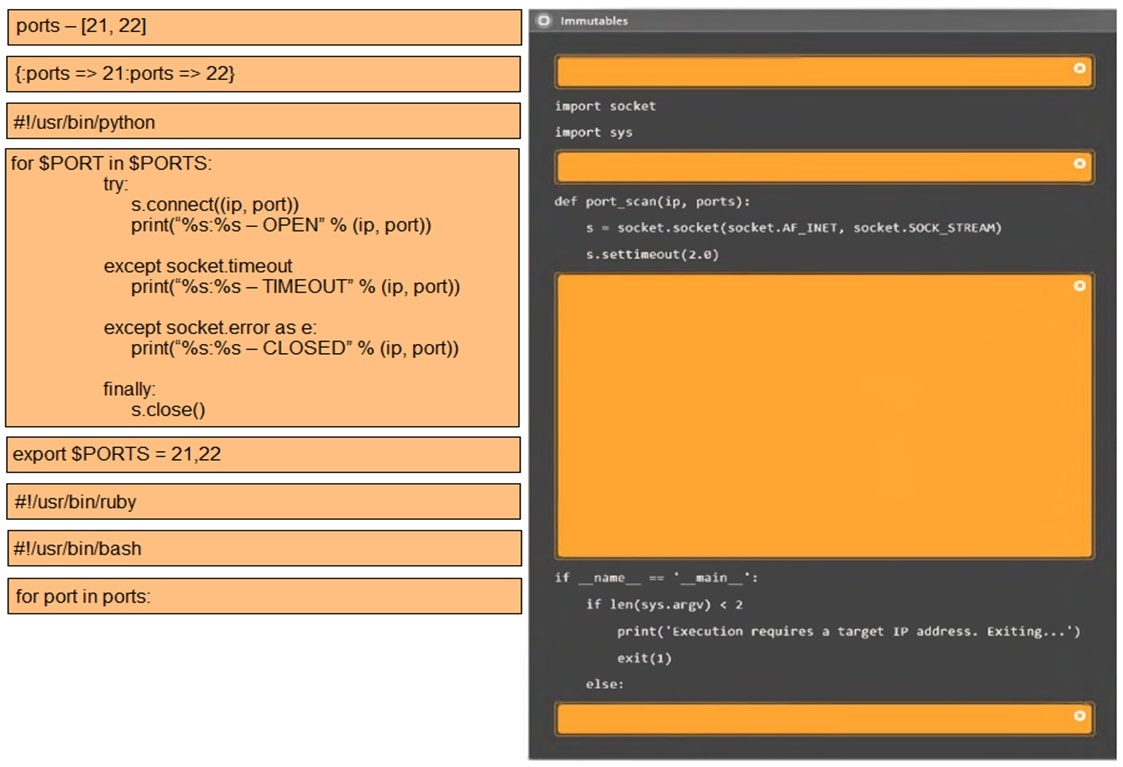
SIMULATION
Using the output, identify potential attack vectors that should be further investigated.
A penetration tester gains access to a system and is able to migrate to a user process:
Given the output above, which of the following actions is the penetration tester performing? (Choose two.)
A penetration tester is conducting an engagement against an internet-facing web application and planning a phishing campaign. Which of the following is the BEST passive method of obtaining the technical contacts for the website?



