Cisco 200-201 - Understanding Cisco Cybersecurity Operations Fundamentals (CBROPS)
What is a Heartbleed vulnerability?
In a SOC environment, what is a vulnerability management metric?
What is the difference between an attack vector and an attack surface?
What is a benefit of agent-based protection when compared to agentless protection?
What is obtained using NetFlow?
Refer to the exhibit.
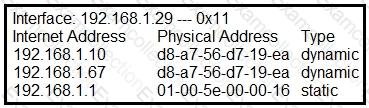
What is occurring in this network?
What is the purpose of command and control for network-aware malware?
Refer to the exhibit.
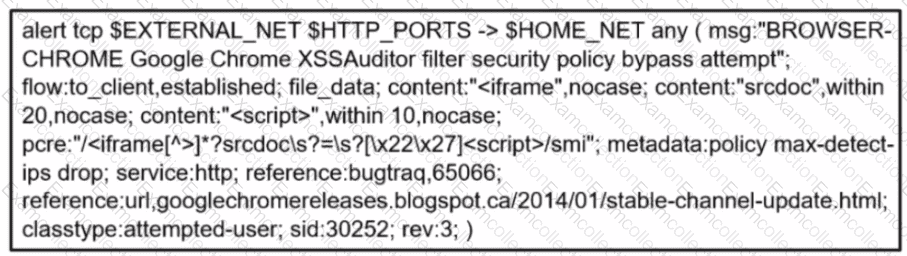
A company's user HTTP connection to a malicious site was blocked according to configured policy What is the source technology used for this measure'?
Refer to the exhibit.
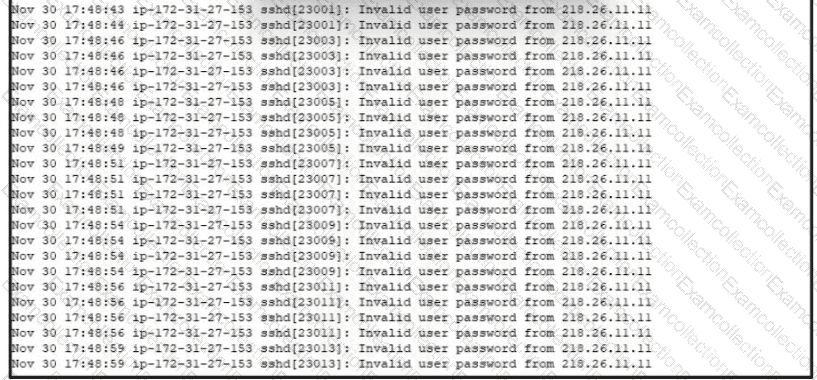
A security analyst is investigating unusual activity from an unknown IP address Which type of evidence is this file1?
Refer to the exhibit.
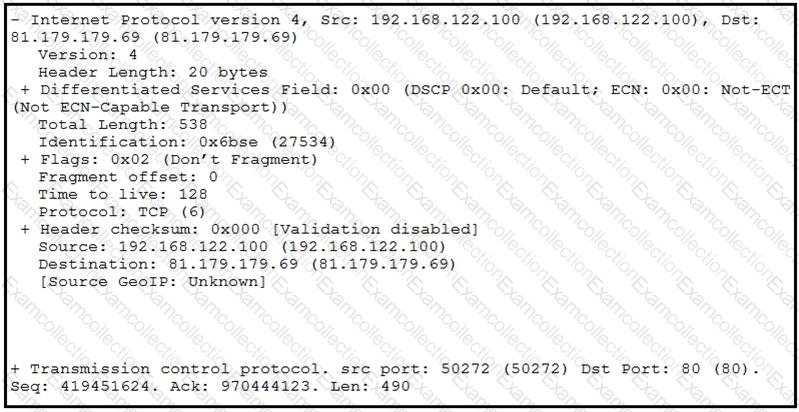
What should be interpreted from this packet capture?



