Cisco 200-201 - Understanding Cisco Cybersecurity Operations Fundamentals (CBROPS)
Which type of data collection requires the largest amount of storage space?
Refer to the exhibit.

Which component is identifiable in this exhibit?
A security engineer deploys an enterprise-wide host/endpoint technology for all of the company's corporate PCs. Management requests the engineer to block a selected set of applications on all PCs.
Which technology should be used to accomplish this task?
A security engineer must protect the company from known issues that trigger adware. Recently new incident has been raised that could harm the system. Which security concepts are present in this scenario?
Refer to the exhibit.
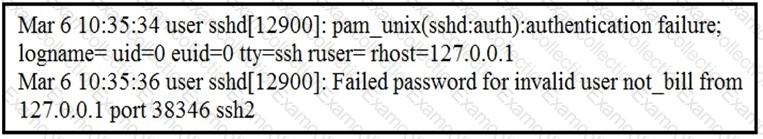
In which Linux log file is this output found?
How does an attacker observe network traffic exchanged between two users?
Refer to the exhibit.
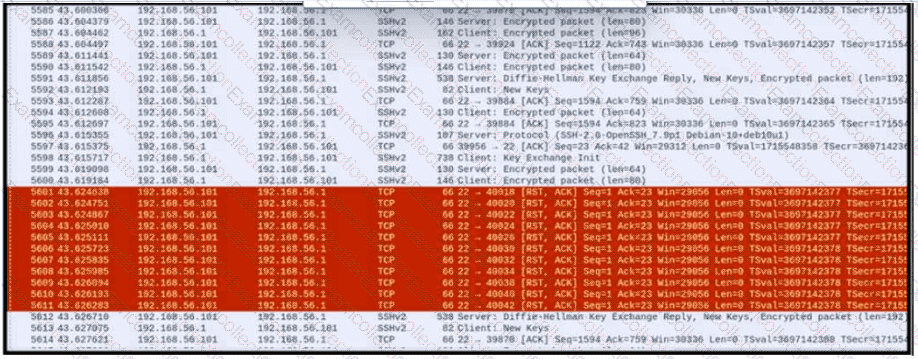
An engineer is analyzing a PCAP file after a recent breach An engineer identified that the attacker used an aggressive ARP scan to scan the hosts and found web and SSH servers. Further analysis showed several SSH Server Banner and Key Exchange Initiations. The engineer cannot see the exact data being transmitted over an encrypted channel and cannot identify how the attacker gained access How did the attacker gain access?
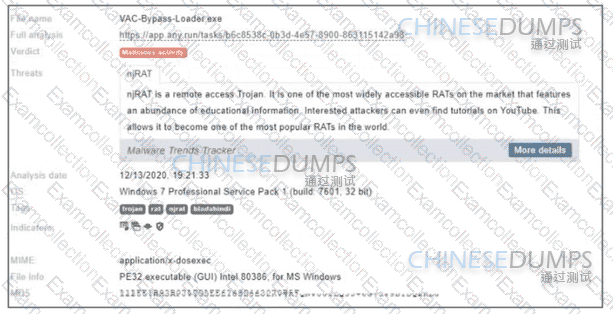
Refer to the exhibit. Where is the executable file?
What is the communication channel established from a compromised machine back to the attacker?
Which evasion method is being used when TLS is observed between two endpoints?



