Cisco 200-201 - Understanding Cisco Cybersecurity Operations Fundamentals (CBROPS)
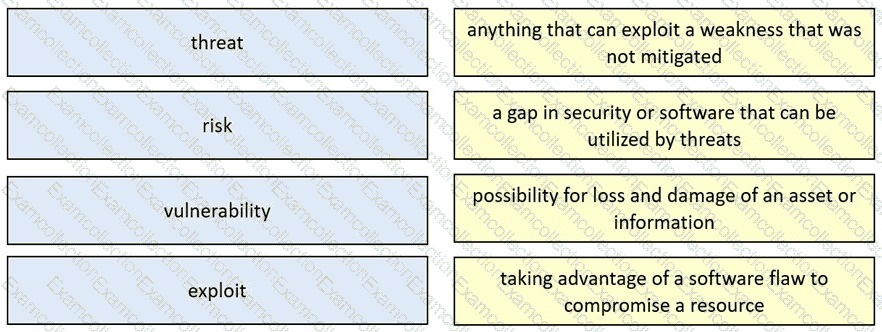
Drag and drop the security concept from the left onto the example of that concept on the right.
Refer to the exhibit.
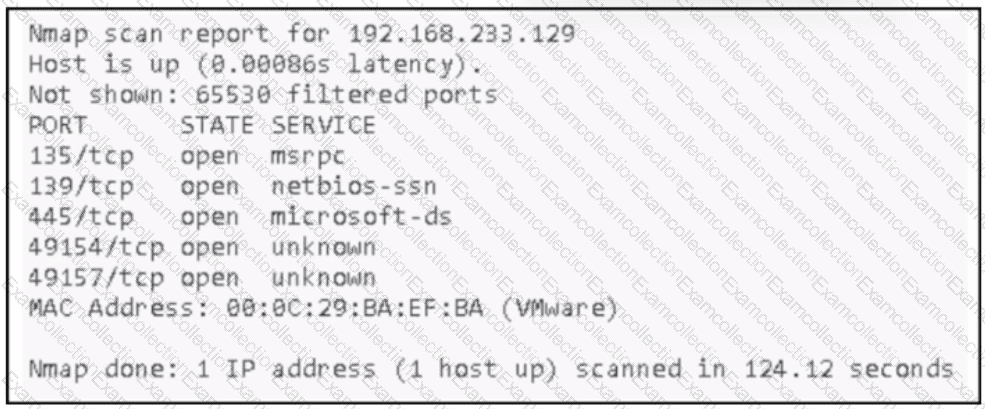
An attacker Infiltrated an organization's network and ran a scan to advance with the lateral movement technique. Which two elements from the scan assist the attacker? (Choose two.)
What is a characteristic of a temporal score in CVSS?
Which piece of information is part of the chain of custody during investigation?
Which CVSS metric group identifies other components that are affected by a successful security attack?
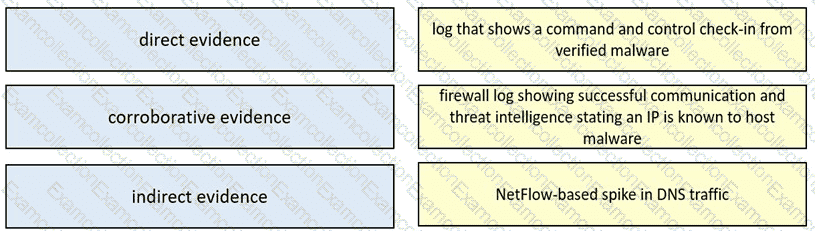
Drag and drop the type of evidence from the left onto the description of that evidence on the right.
An offline audit log contains the source IP address of a session suspected to have exploited a vulnerability resulting in system compromise.
Which kind of evidence is this IP address?
How does certificate authority impact a security system?
An organization is cooperating with several third-party companies. Data exchange is on an unsecured channel using port 80 Internal employees use the FTP service to upload and download sensitive data An engineer must ensure confidentiality while preserving the integrity of the communication. Which technology must the engineer implement in this scenario'?
Which tool provides a full packet capture from network traffic?



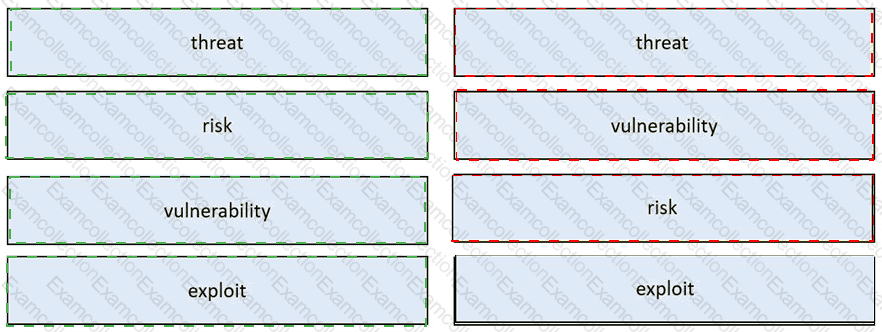
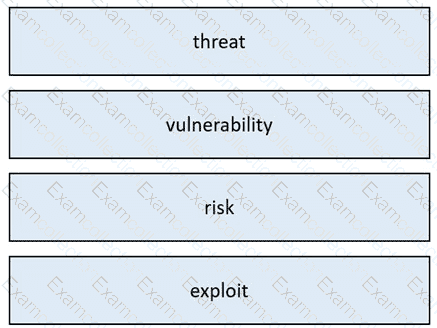 Table Description automatically generated
Table Description automatically generated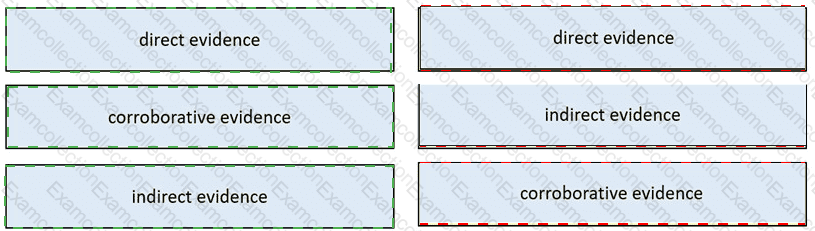
 Graphical user interface, application Description automatically generated
Graphical user interface, application Description automatically generated