Cisco 200-201 - Understanding Cisco Cybersecurity Operations Fundamentals (CBROPS)
Which type of data is used to detect anomalies in the network?
Which event is a vishing attack?
Which data type is necessary to get information about source/destination ports?
A software development company develops high-end technology for the customer that will go through the HIPAA audit program. The technology will be hosted in the cloud, and the healthcare, employee names, and contact information will be stored on two separate logically isolated private cloud services. The patents and inventions will be hosted on a separate encrypted database. A compliance team is asked to analyze the cloud infrastructure and architecture to identify the protected data. Which two types of protected data should be identified? (Choose two.)
What is the dataflow set in the NetFlow flow-record format?
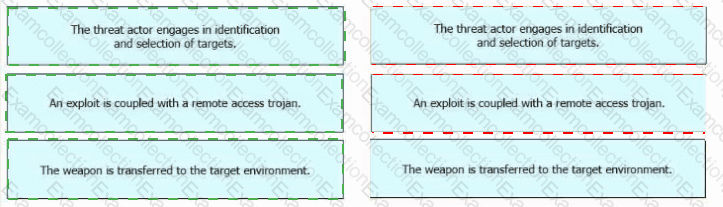
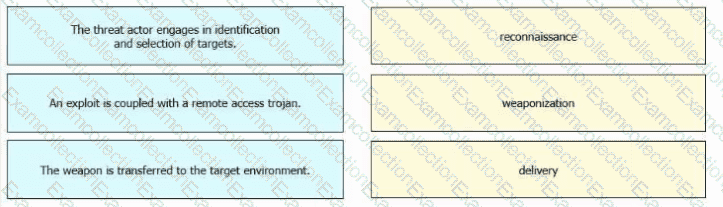
Drag and drop the definitions from the left onto the phases on the right to classify intrusion events according to the Cyber Kill Chain model.
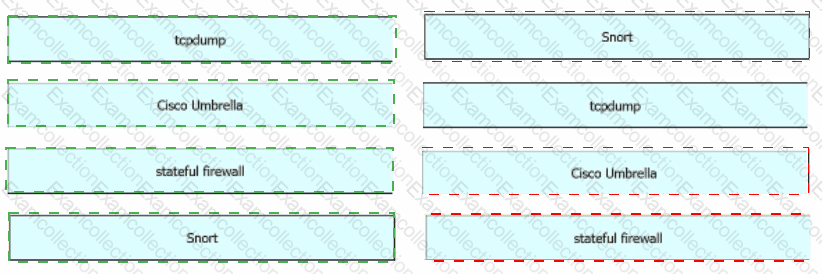
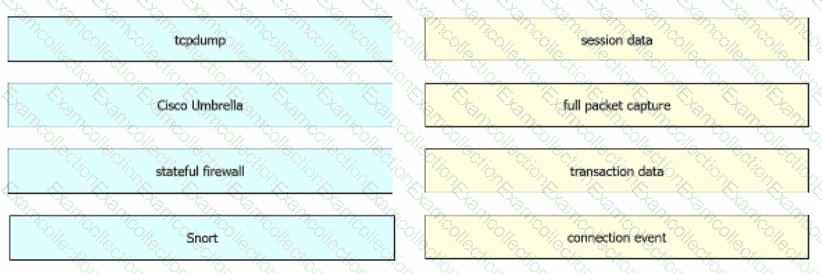
Drag and drop the technologies from the left onto the data types the technologies provide on the right.
A security consultant must change the identity access management model fof their organization The new approach will put responsibility on the owner, who will decide whichusers will have access to which resources Which low-cost model must be used for this purpose?
An analyst is exploring the functionality of different operating systems.
What is a feature of Windows Management Instrumentation that must be considered when deciding on an operating system?
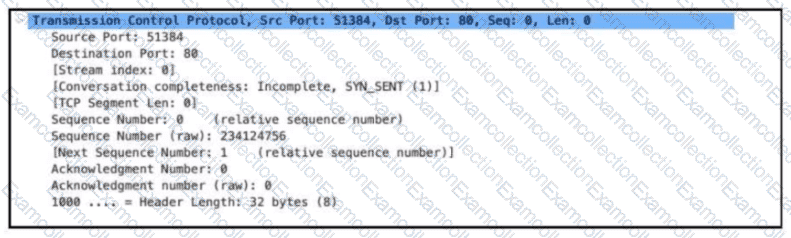
Refer to the exhibit. Which alert is identified from this packet?