Cisco 200-201 - Understanding Cisco Cybersecurity Operations Fundamentals (CBROPS)
An engineer needs to discover alive hosts within the 192.168.1.0/24 range without triggering intrusive portscan alerts on the IDS device using Nmap. Which command will accomplish this goal?
Refer to the exhibit.
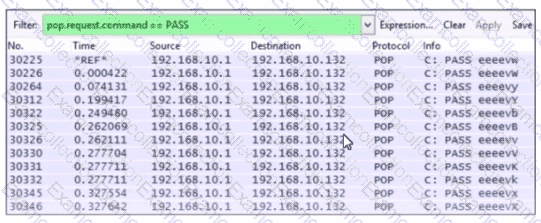
Which alert is identified from this packet capture?
What is the key difference between mandatory access control (MAC) and discretionary access control (DAC)?
Refer to exhibit.
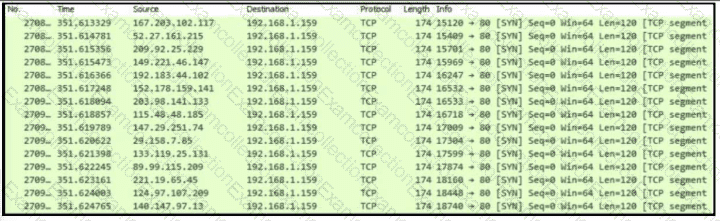
An engineer is Investigating an Intrusion and Is analyzing the pcap file. Which two key elements must an engineer consider? (Choose two.)
What is the difference between the ACK flag and the RST flag?
According to CVSS, which condition is required for attack complexity metrics?
What is the difference between deep packet inspection and stateful inspection?
An engineer is analyzing a recent breach where confidential documents were altered and stolen by the receptionist. Further analysis shows that the threat actor connected an externa USB device to bypass security restrictions and steal data. The engineer could not find an external USB device Which piece of information must an engineer use for attribution in an investigation?
Which HTTP header field is used in forensics to identify the type of browser used?
Refer to the exhibit.
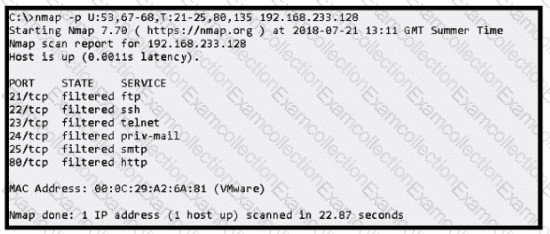
An attacker scanned the server using Nmap.
What did the attacker obtain from this scan?



