Symantec 250-587 - Symantec Data Loss Prevention 16.x Administration Technical Specialist
Which tool must a DLP administrator run to certify the database prior to upgrading DLP?
Which two (2) detection servers are available as virtual appliances? (Choose two.)
A company needs to implement Data Owner Exception so that incidents when employees send or receive their own personal information.
What detection method should the company use?
Why is it important for an administrator to utilize the grid scan feature?
What is Application Detection Configuration?
Which two detection technology options run on the DLP agent? (Choose two.)
A DLP administrator determines that the \SymantecDLP\Protect\Incidents folder on the Enforce server contains. BAD files dated today, while other. IDC files are flowing in and out of the \Incidents directory. Only .IDC files larger than 1MB are turning to .BAD files.
What could be causing only incident data smaller than 1MB to persist while incidents larger than 1MB change to .BAD files?
Which two detection technology options ONLY run on a detection server? (Choose two.)
A DLP administrator needs to stop the PacketCapture process on a detection server. Upon inspection of the Server Detail page, the administrator discovers that all processes are missing from the display.
What are the processes missing from the Server Detail page display?
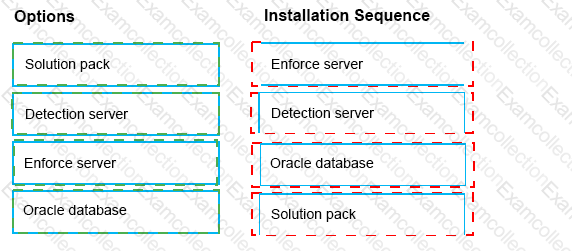
What is the correct installation sequence for the components shown here, according to the Symantec Installation Guide?
Place the options in the correct installation sequence.