Cisco 300-715 - Implementing and Configuring Cisco Identity Services Engine (SISE) v4.0 (300-715 SISE)
An engineer deploys Cisco ISE and must configure Active Directory to then use information from Active Directory in an authorization policy. Which two components must be configured, in addition to Active Directory groups, to achieve this goat? (Choose two )
What must be configured on the WLC to configure Central Web Authentication using Cisco ISE and a WLC?
Which two features should be used on Cisco ISE to enable the TACACS+ feature? (Choose two )
TION NO: 33
Which portal is used to customize the settings for a user to log in and download the compliance module?
An engineer is configuring 802.1X and wants it to be transparent from the users' point of view. The implementation should provide open authentication on the switch ports while providing strong levels of security for non-authenticated devices. Which deployment mode should be used to achieve this?
How is policy services node redundancy achieved in a deployment?
NO: 37
In which two ways can users and endpoints be classified for TrustSec?
(Choose Two.)
An administrator is configuring a Cisco ISE posture agent in the client provisioning policy and needs to ensure that the posture policies that interact with clients are monitored, and end users are required to comply with network usage rules Which two resources must be added in Cisco ISE to accomplish this goal? (Choose two)
Which use case validates a change of authorization?
Refer to the exhibit:
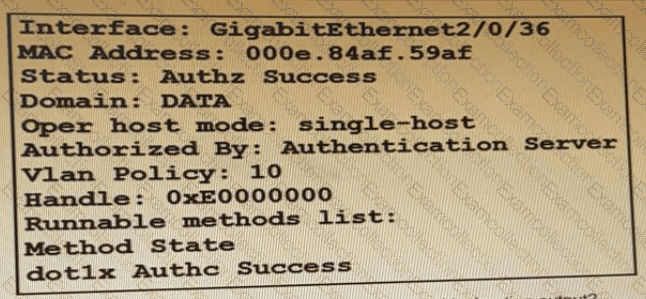
Which command is typed within the CU of a switch to view the troubleshooting output?



