Cisco 300-715 - Implementing and Configuring Cisco Identity Services Engine (SISE) v4.0 (300-715 SISE)
TION NO: 69
Refer to the exhibit.
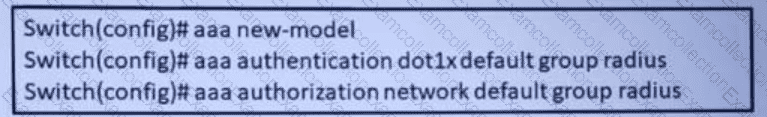
A network engineers configuring the switch to accept downloadable ACLs from a Cisco ISC server Which two commands should be run to complete the configuration? (Choose two)
What is an advantage of TACACS+ versus RADIUS authentication when reviewing reports in Cisco ISE?
A network administrator notices that after a company-wide shut down, many users cannot connect their laptops to the corporate SSID. What must be done to permit access in a timely manner?
A network security administrator needs a web authentication configuration when a guest user connects to the network with a wireless connection using these steps:
. An initial MAB request is sent to the Cisco ISE node.
. Cisco ISE responds with a URL redirection authorization profile if the user's MAC address is unknown in the endpoint identity store.
. The URL redirection presents the user with an AUP acceptance page when the user attempts to go to any URL.
Which authentication must the administrator configure on Cisco ISE?
NO: 188
During a 802 1X deployment, an engineer must identify failed authentications without causing problems for the connected endpoint. Which command will successfully achieve this''
Which three default endpoint identity groups does cisco ISE create? (Choose three)
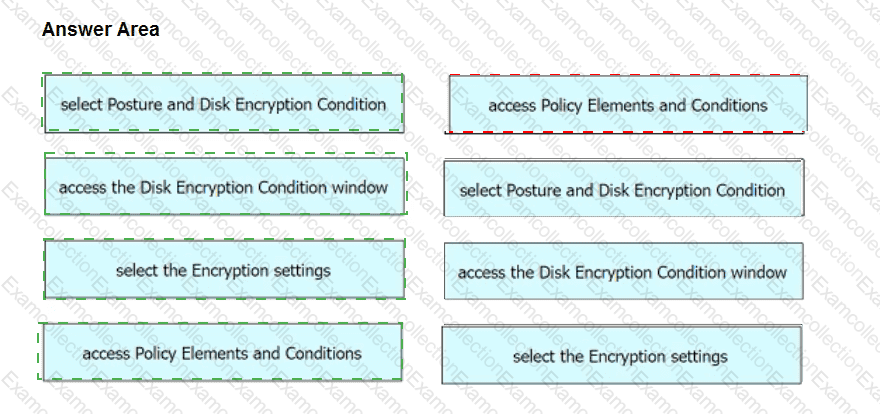
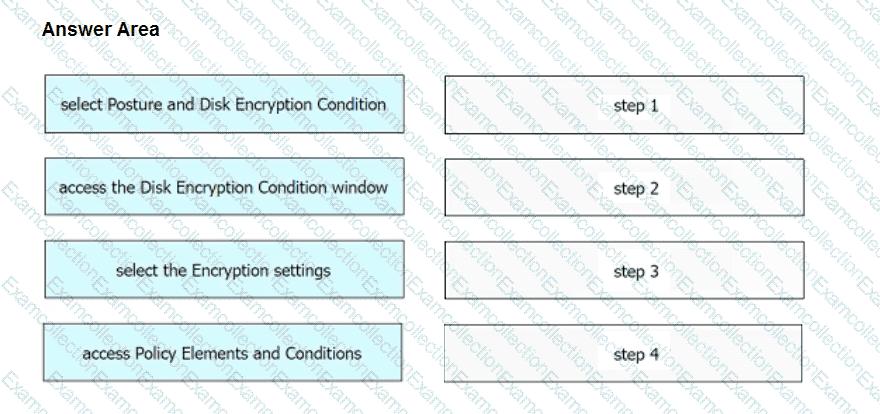
An engineer needs to configure a compliance policy on Cisco ISE to ensure that the latest encryption software is running on the C drive of all endpoints. Drag and drop the configuration steps from the left into the sequence on the right to accomplish this task.
An engineer is testing Cisco ISE policies in a lab environment with no support for a deployment server. In order to push supplicant profiles to the workstations for testing, firewall ports will need to be opened. From which Cisco ISE persona should this traffic be originating?
What gives Cisco ISE an option to scan endpoints for vulnerabilities?
An engineer is creating a new authorization policy to give the endpoints access to VLAN 310 upon successful authentication The administrator tests the 802.1X authentication for the endpoint and sees that it is authenticating successfully What must be done to ensure that the endpoint is placed into the correct VLAN?