ECCouncil 312-39 - Certified SOC Analyst (CSA v2)
A large financial services company has experienced increasing sophisticated threats targeting critical assets. The SOC primarily focuses on log collection and basic monitoring, but incidents revealed gaps in detecting and responding to advanced threats proactively. Management decides to adopt the SOC Capability Maturity Model (CMM). The initial assessment indicates the SOC is at Level 1, and the organization aims to reach Level 3 by enhancing incident response procedures, improving threat intelligence integration, establishing KPIs, automating triage, implementing behavior-based analytics, and creating continuous training. Based on the SOC CMM, what should be the first priority in transitioning from Level 1 to Level 3?
If the SIEM generates the following four alerts at the same time:
I.Firewall blocking traffic fromgetting into the network alerts
II.SQL injection attempt alerts
III.Data deletion attempt alerts
IV.Brute-force attempt alerts
Which alert should be given least priority as per effective alert triaging?
John as a SOC analyst is worried about the amount of Tor traffic hitting the network. He wants to prepare adashboard in the SIEM to get a graph to identify the locations from where the TOR traffic is coming.
Which of the following data source will he use to prepare the dashboard?
Bob is a SOC analyst in a multinational corporation that relies on a centralized file-sharing system for storing confidential project documents. One morning, he notices that a few critical financial records stored on the shared server appear to have been altered without authorization. Version history confirms unexpected changes made outside business hours. Bob must investigate by inspecting logs. Which log should he check to determine who accessed the files and when the modifications occurred?
In which log collection mechanism, the system or application sends log records either on the local disk or over the network.
ABC is a multinational company with multiple offices across the globe, and you are working as an L2 SOC analyst. You are implementing a centralized logging solution to enhance security monitoring. You must ensure that log messages from routers, firewalls, and servers across multiple remote offices are efficiently collected and forwarded to a central syslog server. To streamline this process, an intermediate component is deployed to receive log messages from different devices and forward them to the main syslog server. Which component in the syslog infrastructure performs this function?
Which attack works like a dictionary attack, but adds some numbers and symbols to the words from the dictionary and tries to crack the password?
The SOC analyst at a national cybersecurity agency detected unusual system behavior on critical infrastructure servers. Initial scans flagged potential malware activity. Due to the sophisticated nature of the suspected attack, including registry modifications, process injection, and unauthorized tasks, the case was escalated to the forensic team. The forensic team suspects the malware is designed for stealthy data exfiltration. To assess the compromise, they captured system snapshots before and after suspected infection to identify unauthorized changes and anomalies. Which process are they following by capturing and comparing system snapshots to detect unauthorized changes?
An organization is implementing and deploying the SIEM with following capabilities.
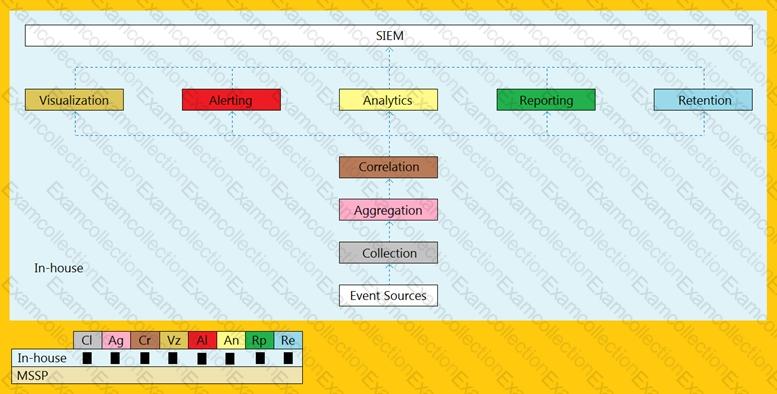
What kind of SIEM deployment architecture the organization is planning to implement?
A security analyst in a multinational corporation’s Threat Intelligence team is tasked with enhancing detection of stealthy malware infections. During an investigation, the analyst observes an unusually high volume of DNS requests directed toward domains that follow patterns commonly associated with Domain Generation Algorithms (DGAs). Recognizing that these automated domain queries could indicate malware attempting to establish communication with command-and-control (C2) infrastructure, the analyst realizes existing detection may be insufficient. The security team needs to define intelligence requirements, including identifying critical data sources, refining detection criteria, and improving monitoring strategies. Which stage of the Cyber Threat Intelligence (CTI) process does this align with?



