Cisco 350-701 - Implementing and Operating Cisco Security Core Technologies (SCOR 350-701)
Which feature must be configured before implementing NetFlow on a router?
Which statement about IOS zone-based firewalls is true?
What is the purpose of the Decrypt for Application Detection feature within the WSA Decryption options?
An organization wants to provide visibility and to identify active threats in its network using a VM. The
organization wants to extract metadata from network packet flow while ensuring that payloads are not retained
or transferred outside the network. Which solution meets these requirements?
Which encryption algorithm provides highly secure VPN communications?
What is a capability of Cisco ASA Netflow?
An organization recently installed a Cisco WSA and would like to take advantage of the AVC engine to allow the organization to create a policy to control application specific activity. After enabling the AVC engine, what must be done to implement this?
Refer to the exhibit.
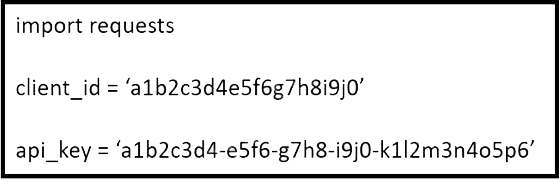
What does the API key do while working with https://api.amp.cisco.com/v1/computers?
What are two facts about WSA HTTP proxy configuration with a PAC file? (Choose two.)
Which technology provides the benefit of Layer 3 through Layer 7 innovative deep packet inspection,
enabling the platform to identify and output various applications within the network traffic flows?
Which feature is used in a push model to allow for session identification, host reauthentication, and session termination?
What is a benefit of using Cisco Tetration?
When network telemetry is implemented, what is important to be enabled across all network infrastructure devices to correlate different sources?
On which part of the IT environment does DevSecOps focus?
Which two types of connectors are used to generate telemetry data from IPFIX records in a Cisco Secure Workload implementation? (Choose two.)



