Microsoft AZ-801 - Configuring Windows Server Hybrid Advanced Services
You have an Azure virtual machine named VM1 that runs Windows Server.
You plan to deploy a new line-of-business (LOB) application to VM1.
You need to ensure that the application can create child processes.
What should you configure on VM1?
You have a server that runs Windows Server and hosts an app named Appl.
You need to prevent App1 from accessing external SMTP servers. The solution must meet the following requirements:
• Minimize the impact on AppVs access to external HTTP servers.
• Minimize the impact on other apps on (he server.
• Minimize administrative effort
What should you implement in Windows Defender Firewall?
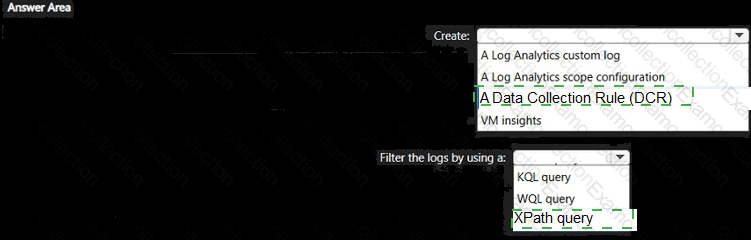
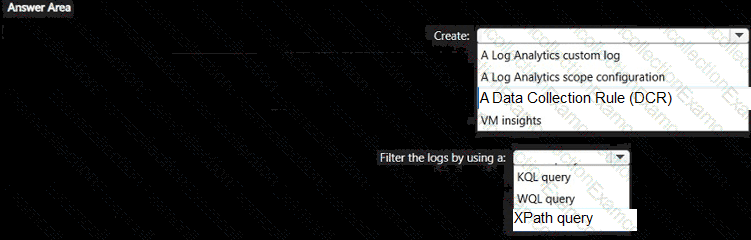
You have 100 Azure virtual machines that run Windows Server.
You plan to use Azure Monitor agents to track occurrences of event 10 1035 in the Application log of each virtual machine.
You need to ensure that the events will be available tor analysis in Log Analytics. The solution must minimize the total volume of events stored in Azure.
What should you do? To answer, select the appropriate options in the answer area.
NOTE: Each correct selection is worth one point.
Your company uses Storage Spaces Direct.
You need to view the available storage in a Storage Space Direct storage pool.
What should you use?
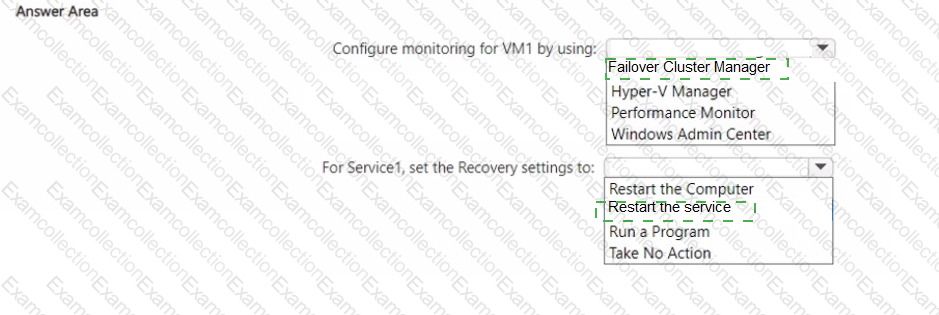
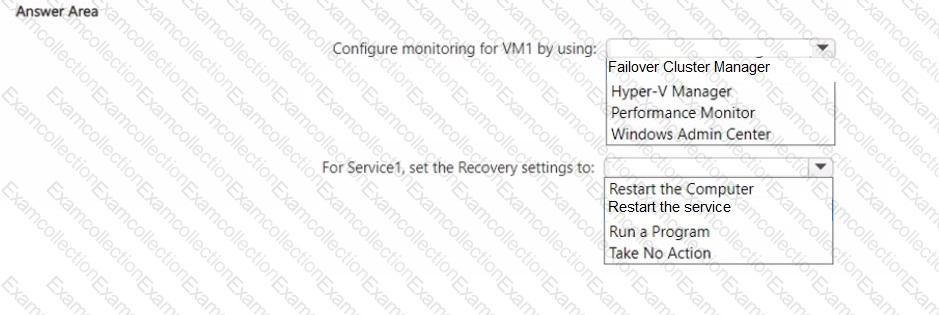
You have a Hyper-V failover cluster named Ousted. Cluster1 contains a virtual machine named VM1 that runs Windows Server. VM1 contains a Windows service named Service1.
You need to ensure that Cluster1 performs a recovery action if Service1 fails.
What should you do? To answer, select the appropriate options in the answer area.
NOTE: Each correct selection is worth one point.
You have a server named Served that runs Windows Server. You install a custom app named App1 that is accessed by using TCP port 52310. Users report that they cannot access App1. You confirm that App1 is running on Server1.
You need to ensure that the users can access App1. The solution must only provide access to App1 on Server1. What should you do in Windows Defender Firewall with Advanced Security?
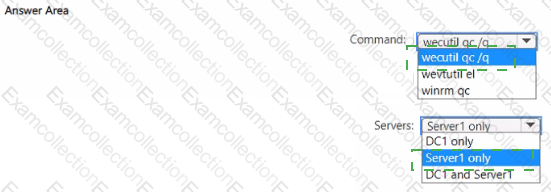
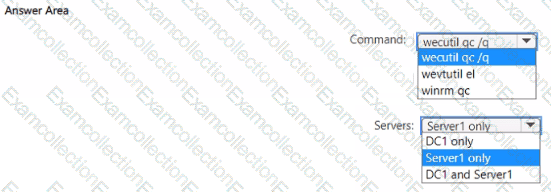
Your network contains an Active Directory domain. The domain contains a domain controller named DC1 and a server named Server1 that runs Windows Server.
You need to enable event log subscriptions to forward events from DC1 to Server1.
Which command should you run to enable the Windows Event Collector service, and on which servers should you run the command? To answer, select the appropriate options in the answer area.
NOTE: Each correct selection is worth one point.
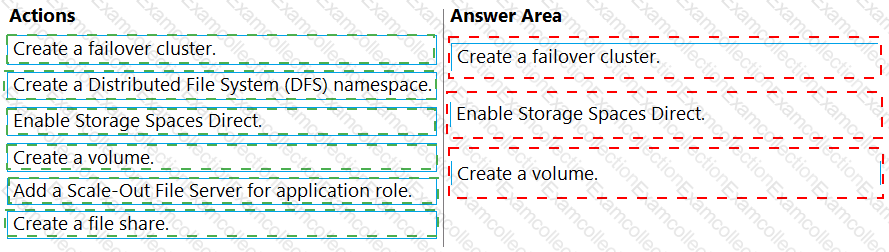
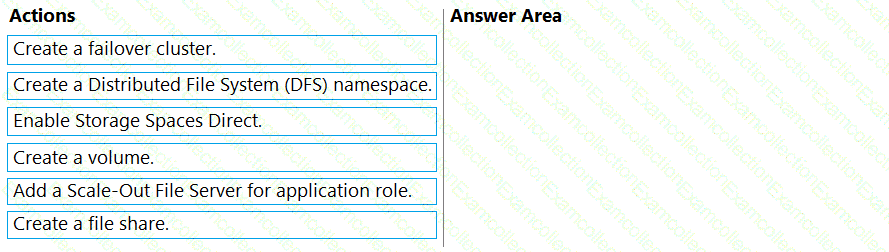
You have three servers named Server1, Server2, Server3 that run Windows Server and have the Hyper-V server role installed.
You plan to create a hyper-converged cluster to host Hyper-V virtual machines.
You need to ensure that you can store virtual machines in Storage Spaces Direct.
Which three actions should you perform in sequence? To answer, move the appropriate actions from the list of actions to the answer area and arrange them in the correct order.
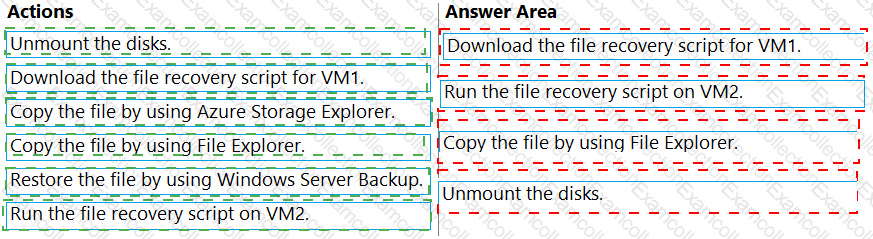
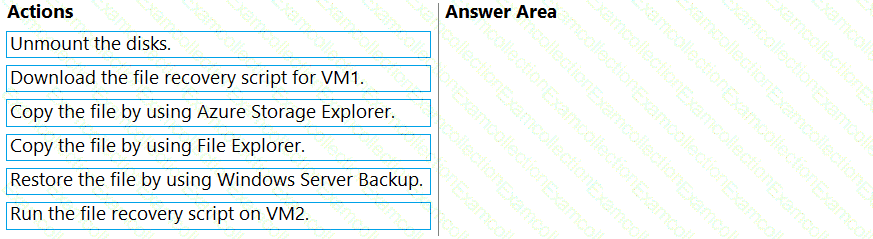
You have two Azure virtual machines named VM1 and VM2. VM1 is backed up to an Azure Recovery Services vault daily and retains backups for 30Â days.
You need to restore an individual file named C:\Data\Important.docx from VM1 to VM2. The solution must minimize administrative effort.
Which four actions should you perform in sequence? To answer, move the appropriate actions from the list of actions to the answer area and arrange them in the correct order.
You are planning the deployment of Microsoft Sentinel.
Which type of Microsoft Sentinel data connector should you use to meet the security requirements?