CompTIA CAS-005 - CompTIA SecurityX Certification Exam
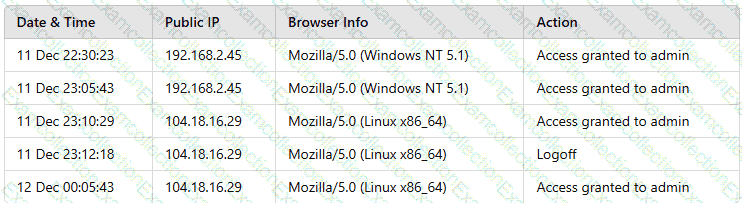
A building camera is remotely accessed and disabled from the remote console application during off-hours. A security analyst reviews the following logs:
Which of the following actions should the analyst take to best mitigate the threat?
A systems administrator wants to introduce a newly released feature for an internal application. The administrate docs not want to test the feature in the production environment. Which of the following locations is the best place to test the new feature?
A security analyst is developing a threat model that focuses on attacks associated with the organization's storage products. The products:
• Are used in commercial and government user environments
• Are required to comply with crypto-export requirements
• Include both hardware and software components that are developed by external vendors in Europe and Asia
Which of the following are the most important for the analyst to consider when developing the model? (Select two).
An organization purchased a new manufacturing facility and the security administrator needs to:
• Implement security monitoring.
• Protect any non-traditional device(s)/network(s).
• Ensure no downtime for critical systems.
Which of the following strategies best meets these requirements?
An organization wants to implement a secure cloud architecture across all instances. Given the following requirements:
· Establish a standard network template.
· Deployments must be consistent.
· Security policies must be able to be changed at scale.
Which of the following technologies meets these requirements?
A security analyst is reviewing the following vulnerability assessment report:
192.168.1.5, Host = Server1, CVSS 7.5, Web Server, Remotely Executable = Yes, Exploit = Yes
205.1.3.5, Host = Server2, CVSS 6.5, Bind Server, Remotely Executable = Yes, Exploit = POC
207.1.5.7, Host = Server3, CVSS 5.5, Email Server, Remotely Executable = Yes, Exploit = Yes
192.168.1.6, Host = Server4, CVSS 9.8, Domain Controller, Remotely Executable = Yes, Exploit = Yes
Which of the following should be patched first to minimize attacks against internet-facing hosts?
A security officer received several complaints from usersabout excessive MPA push notifications at night The security team investigates and suspects malicious activities regarding user account authentication Which of the following is the best way for the security officer to restrict MI~A notifications''
A company detects suspicious activity associated with inbound connections. Security detection tools are unable to categorize this activity. Which of the following is the best solution to help the company overcome this challenge?
An organization hires a security consultant to establish a SOC that includes athreat-modeling function. During initial activities, the consultant works with system engineers to identify antipatterns within the environment. Which of the following is most critical for the engineers to disclose to the consultant during this phase?
An organization has been using self-managed encryption keys rather than the free keys managed by the cloud provider. The Chief Information Security Officer (CISO) reviews the monthly bill and realizes the self-managed keys are more costly than anticipated. Which of the following should the CISO recommend to reduce costs while maintaining a strong security posture?



