CyberArk CPC-CDE-RECERT - CyberArk CDE-CPC Recertification
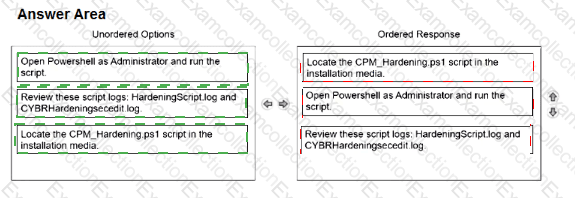
Arrange the steps to complete CPM Hardening for out-of-Domain deployment in the correct sequence.
Which statements are correct regarding enabling end users from multiple domains in the same forest to authenticate to CyberArk Privilege Cloud? (Choose two.)
Before you can delete a Safe, you must first delete all of its content (accounts and files) permanently. What else must also be achieved before the Safe can be successfully deleted?
You are implementing LDAPS Integration for a standard Privilege Cloud environment.
Which information must be provided to the CyberArk Privilege Cloud support team through a Service Request? (Choose 2.)
Which statement is correct about using the AllowedSafes platform parameter?
According to best practice, when considering the location of PSM Connector servers in Privilege Cloud environments, where should the PSM be placed?
When installing the PSM and CPM components on the same Privilege Cloud Connector, what should you consider when hardening?
Which statements accurately describe the process of LDAP integration with CyberArk Privilege Cloud Standard? (Choose two.)
A support team has asked you to provide the previous password for an account that had its password recently changed by the CPM. In which tab within the account's overview page can you retrieve this information?
You are deploying a CyberArk Identity Connector to integrate Privilege Cloud Shared Services with an Active Directory environment. Which requirement must be met?