CyberArk CPC-CDE-RECERT - CyberArk CDE-CPC Recertification
You are configuring firewall rules between the Privilege Cloud components and the Privilege Cloud. Which firewall rules should be set up to allow connections?
In large-scale environments, it is important to enable the CPM to focus its search operations on specific Safes instead of scanning all Safes it sees in the Vault. How is this accomplished?
What is the default username for the PSM for SSH maintenance user?
When using Connector Management, how do you configure a DR CPM in Privilege Cloud shared services? (Choose two.)
An end user (external user account) has been removed from the Users tab in CyberArk Identity Administration and tries to log in to the CyberArk Privilege Cloud portal using the correct credentials. What will happen?
Which actions must be performed when manually hardening a SUSE server with PSM for SSH? (Choose two.)
'What is a default authentication profile to access CyberArk Identity?
Which file must you edit to ensure the PSM for SSH server is not hardened automatically after installation?
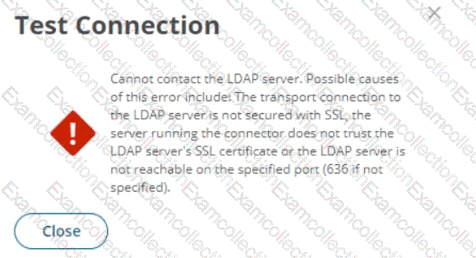
Refer to the exhibit.
You set up your LDAP Directory in CyberArk Identity, but encountered an error during the connection test.
Which scenarios could represent a valid misconfiguration? (Choose 2.)
Which group has only View Audit and View Safe permissions?



