CompTIA CS0-003 - CompTIA CyberSecurity Analyst CySA+ Certification Exam
A security administrator has found indications of dictionary attacks against the company ' s external-facing portal. Which of the following should be implemented to best mitigate the password attacks?
An older CVE with a vulnerability score of 7.1 was elevated to a score of 9.8 due to a widely available exploit being used to deliver ransomware. Which of the following factors would an analyst most likely communicate as the reason for this escalation?
Which of the following are process improvements that can be realized by implementing a SOAR solution? (Select two).
A security analyst receives an alert for suspicious activity on a company laptop An excerpt of the log is shown below:
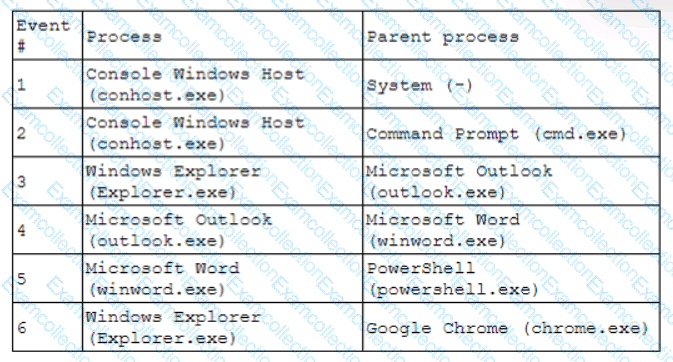
Which of the following has most likely occurred?
Which of the following best explains the importance of network microsegmentation as part of a Zero Trust architecture?
Which of the following best explains the importance of the implementation of a secure software development life cycle in a company with an internal development team?
A cybersecurity analyst has recovered a recently compromised server to its previous state. Which of the following should the analyst perform next?
A security analyst needs to prioritize vulnerabilities for patching. Given the following vulnerability and system information:
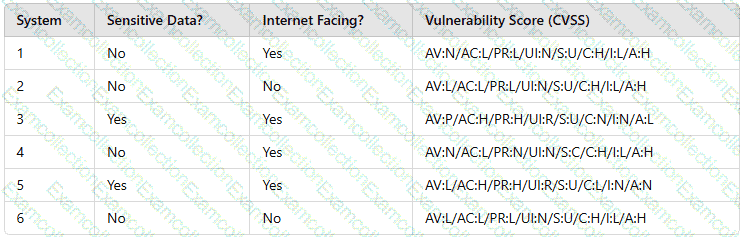
Which of the following systems should the analyst patch first?
Which of the following is the most important factor to ensure accurate incident response reporting?
Results of a SOC customer service evaluation indicate high levels of dissatisfaction with the inconsistent services provided after regular work hours. To address this, the SOC lead drafts a document establishing customer expectations regarding the SOC ' s performance and quality of services. Which of the following documents most likely fits this description?



