ECCouncil EC0-350 - Ethical Hacking and Countermeasures V8
What is the primary drawback to using advanced encryption standard (AES) algorithm with a 256 bit key to share sensitive data?
If an e-commerce site was put into a live environment and the programmers failed to remove the secret entry point that was used during the application development, what is this secret entry point known as?
Which of the following techniques does a vulnerability scanner use in order to detect a vulnerability on a target service?
An ethical hacker for a large security research firm performs penetration tests, vulnerability tests, and risk assessments. A friend recently started a company and asks the hacker to perform a penetration test and vulnerability assessment of the new company as a favor. What should the hacker's next step be before starting work on this job?
Which of the following is a symmetric cryptographic standard?Â
What technique is used to perform a Connection Stream Parameter Pollution (CSPP) attack?
Which of the following descriptions is true about a static NAT?
Which of the following business challenges could be solved by using a vulnerability scanner?
Which protocol and port number might be needed in order to send log messages to a log analysis tool that resides behind a firewall?
Which of the following network attacks relies on sending an abnormally large packet size that exceeds TCP/IP specifications?
Firewalk has just completed the second phase (the scanning phase) and a technician receives the output shown below. What conclusions can be drawn based on these scan results? TCP port 21 – no response TCP port 22 – no response TCP port 23 – Time-to-live exceeded
Which of the following techniques can be used to mitigate the risk of an on-site attacker from connecting to an unused network port and gaining full access to the network? (Choose three.)
In the software security development life cyle process, threat modeling occurs in which phase?
Which of the following can take an arbitrary length of input and produce a message digest output of 160 bit?
An attacker sniffs encrypted traffic from the network and is subsequently able to decrypt it. The attacker can now use which cryptanalytic technique to attempt to discover the encryption key?
Some passwords are stored using specialized encryption algorithms known as hashes. Why is this an appropriate method?
Keystroke logging is the action of tracking (or logging) the keys struck on a keyboard, typically in a covert manner so that the person using the keyboard is unaware that their actions are being monitored.
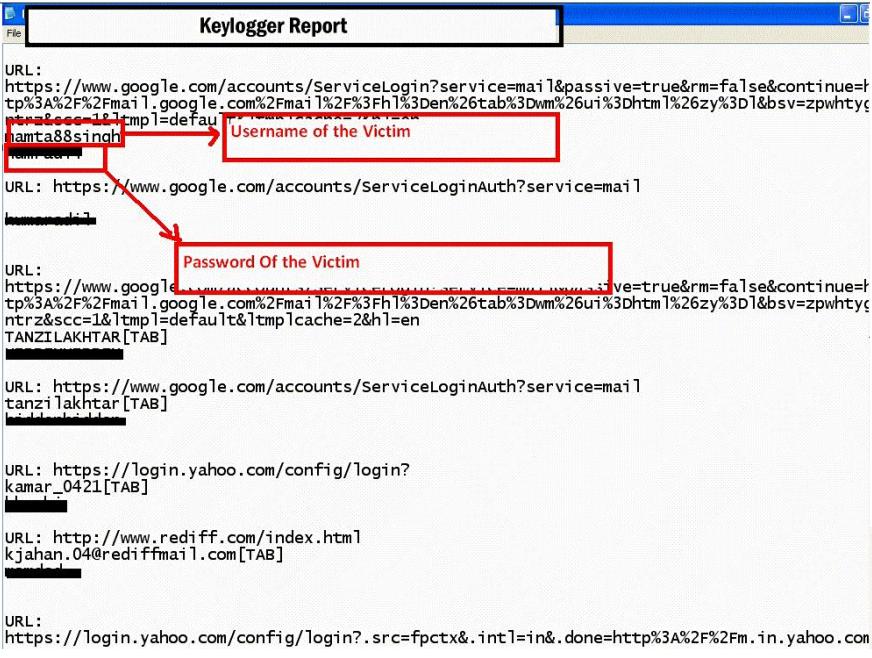
How will you defend against hardware keyloggers when using public computers and Internet Kiosks? (Select 4 answers)
When utilizing technical assessment methods to assess the security posture of a network, which of the following techniques would be most effective in determining whether end-user security training would be beneficial?
NTP allows you to set the clocks on your systems very accurately, to within 100ms and sometimes-even 10ms. Knowing the exact time is extremely important for enterprise security. Various security protocols depend on an accurate source of time information in order to prevent "playback" attacks. These protocols tag their communications with the current time, to prevent attackers from replaying the same communications, e.g., a login/password interaction or even an entire communication, at a later date. One can circumvent this tagging, if the clock can be set back to the time the communication was recorded. An attacker attempts to try corrupting the clocks on devices on your network. You run Wireshark to detect the NTP traffic to see if there are any irregularities on the network. What port number you should enable in Wireshark display filter to view NTP packets?
A company has made the decision to host their own email and basic web services. The administrator needs to set up the external firewall to limit what protocols should be allowed to get to the public part of the company's network. Which ports should the administrator open? (Choose three.)



