RedHat EX407 - Red Hat Certified Specialist in Ansible Automation exam
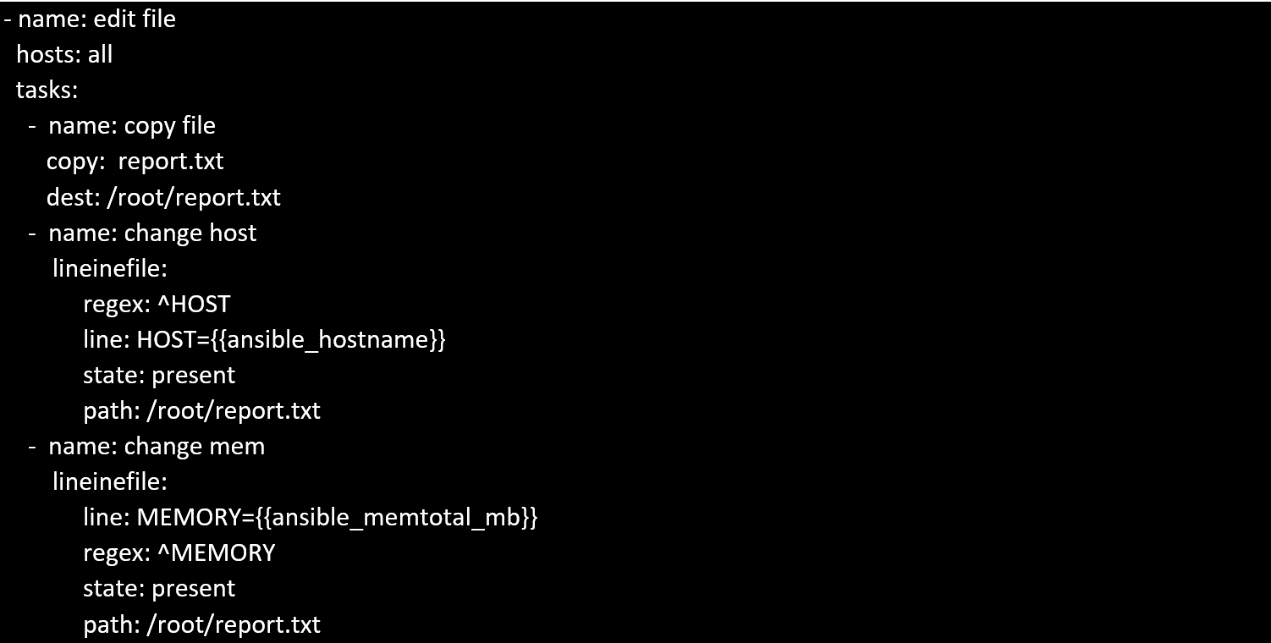
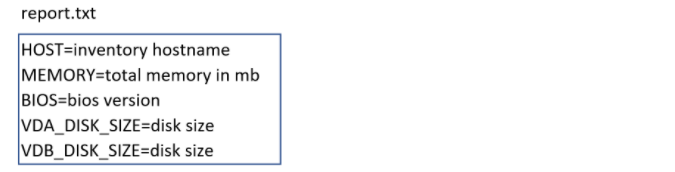
Create a file in /home/sandy/ansible/ called report.yml. Using this playbook, get a file called report.txt (make it look exactly as below). Copy this file over to all remote hosts at /root/report.txt. Then edit the lines in the file to provide the real information of the hosts. If a disk does not exist then write NONE.
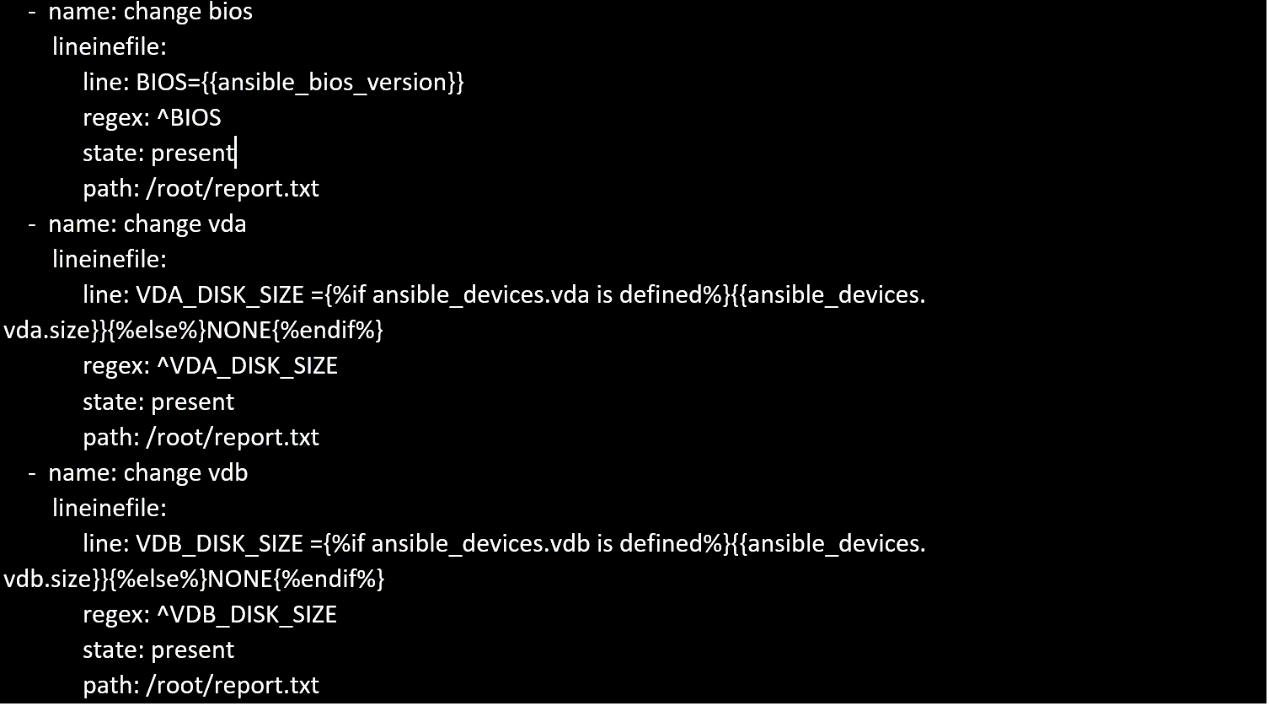
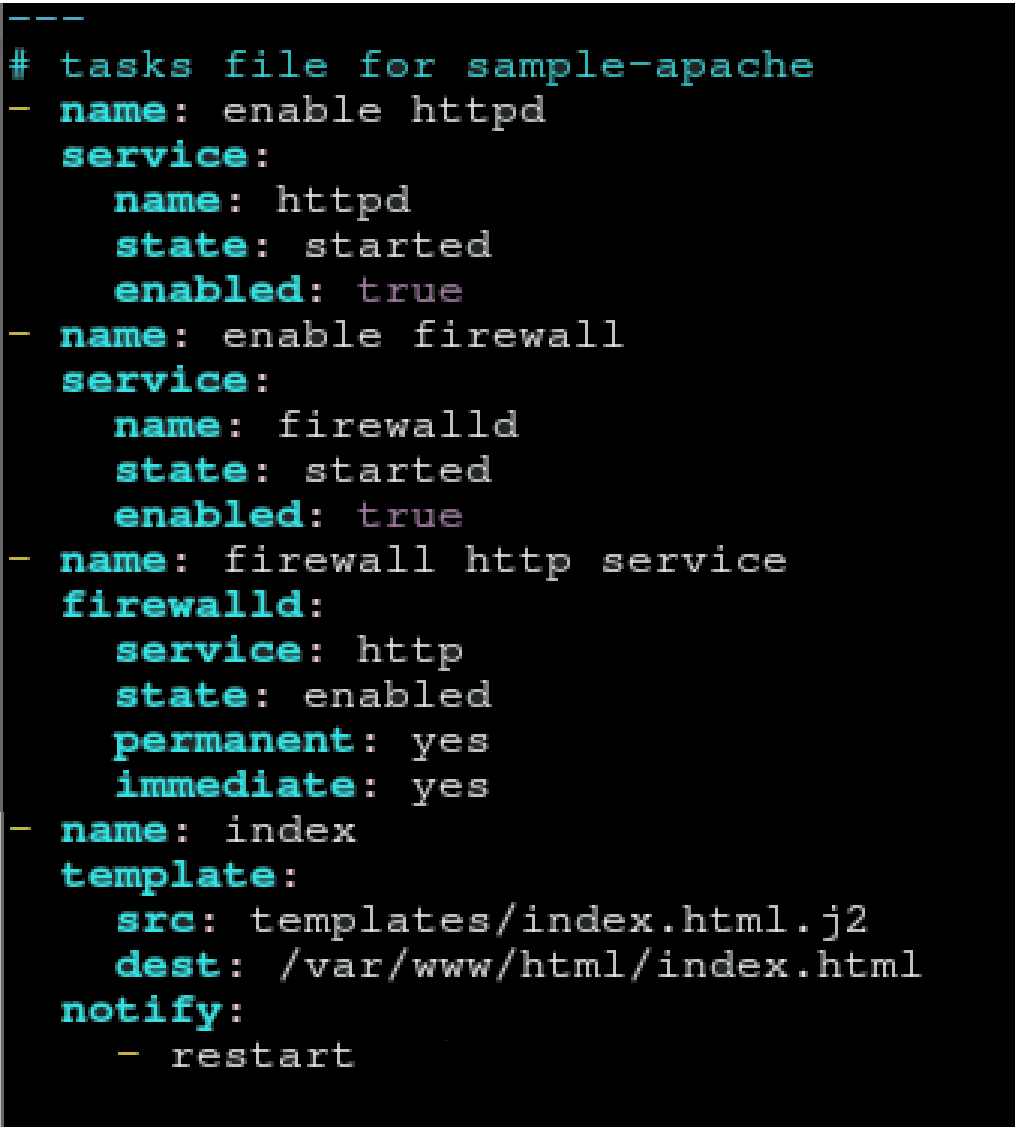
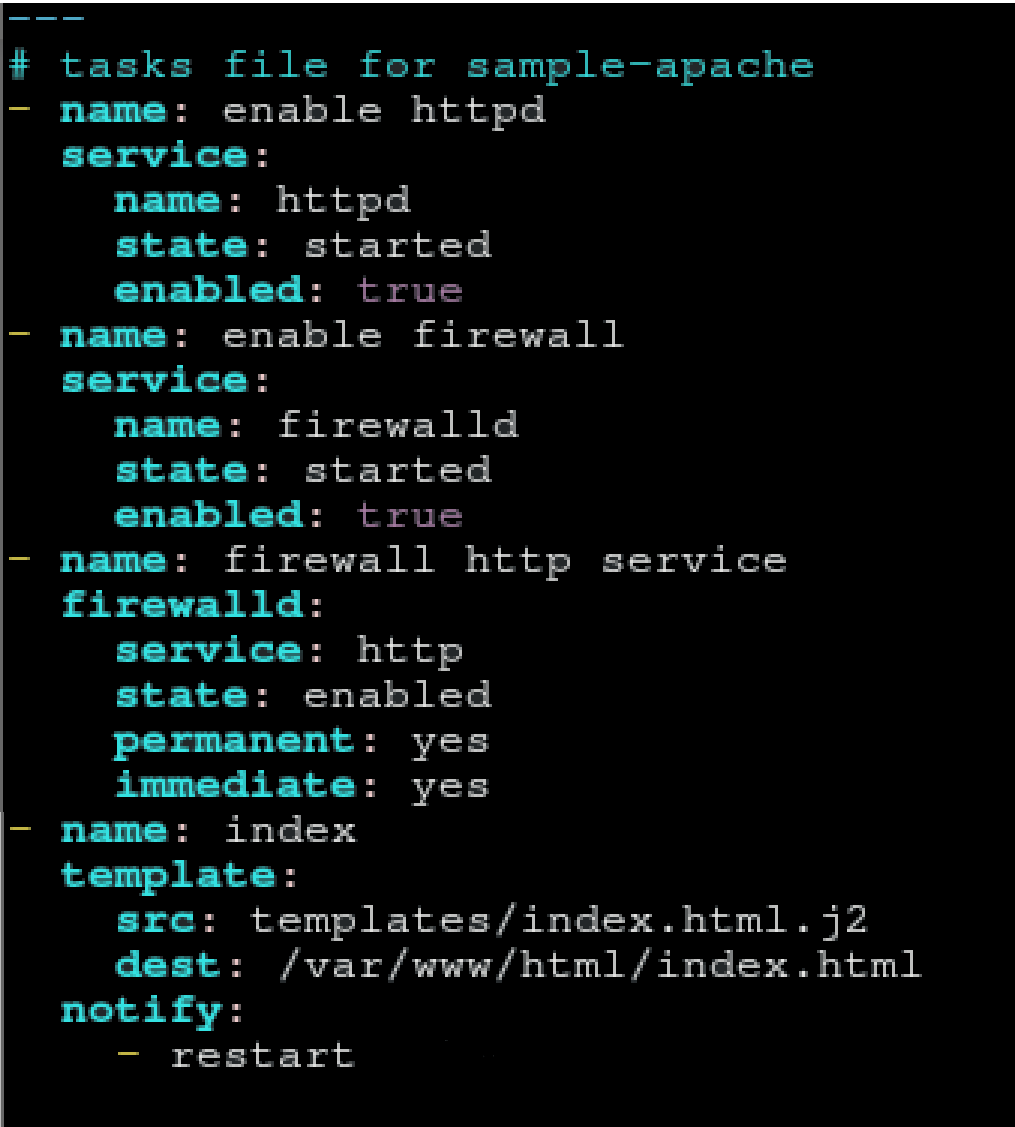
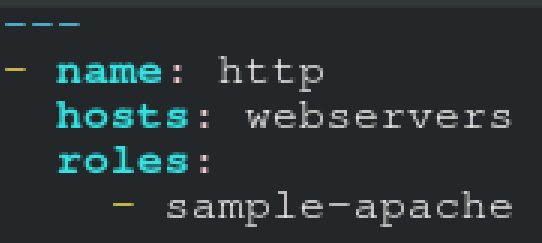
Create a role called sample-apache and store it in /home/bob/ansible/roles. The role should
satisfy the following requirements:
*In the role, install and enable httpd. Also enable the firewall to allow http. Also run the template
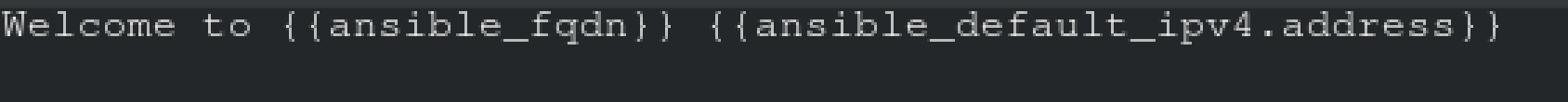
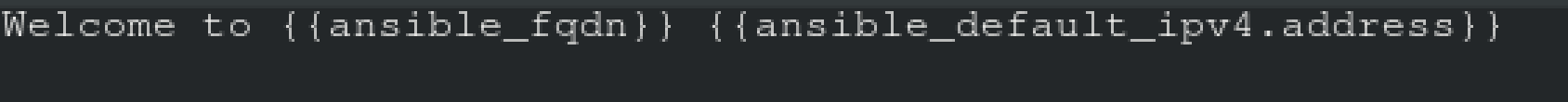
*index.html.j2 and make sure this runs Create a template index.html.j2 that displays "Welcome to the server HOSTNAME"
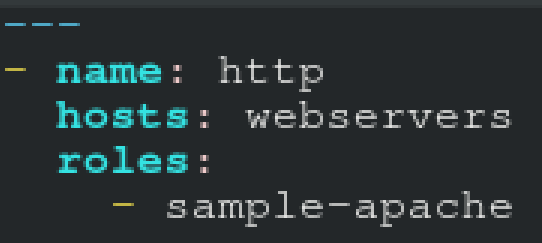
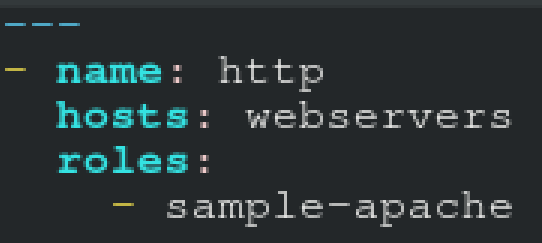
In a play called apache.yml in /home/bob/ansible/ run the sample-apache role.
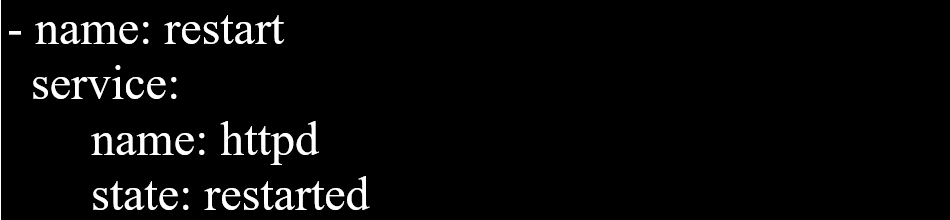
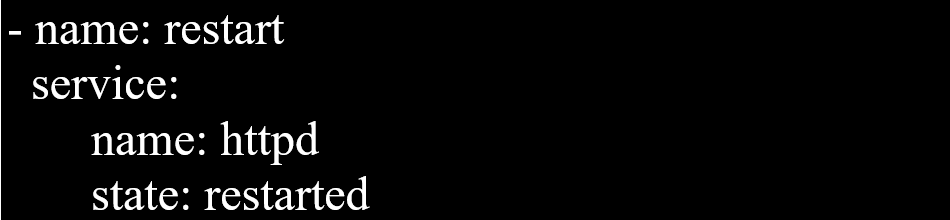
Create a role called sample-apache in /home/sandy/ansible/roles that enables and starts httpd, enables and starts the firewall and allows the webserver service. Create a template called index.html.j2 which creates and serves a message from /var/www/html/index.html Whenever the content of the file changes, restart the webserver service.
Welcome to [FQDN] on [IP]
Replace the FQDN with the fully qualified domain name and IP with the ip address of the node using ansible facts. Lastly, create a playbook in /home/sandy/ansible/ called apache.yml and use the role to serve the index file on webserver hosts.
Using the Simulation Program, perform the following tasks:
Ad-Hoc Ansible Commands (Number Two) Task:
1. Use the ad-hoc command to make sure php is installed.
2. Use the ad-hoc command to make sure that php is installed and is the latest version.
3. Use the ad-hoc command to make sure that httpd is installed.
4. Use the ad-hoc command to remove httpd from the servers.
Create a playbook /home/bob /ansible/motd.yml that runs on all inventory hosts and docs the following: The playbook should replaee any existing content of/etc/motd in the following text. Use ansible facts to display the FQDN of each host
On hosts in the dev host group the line should be "Welcome to Dev Server FQDN".
On hosts in the webserver host group the line should be "Welcome to Apache Server FQDN".
On hosts in the database host group the line should be "Welcome to MySQL Server FQDN".
Create an empty encrypted file called myvault.yml in /home/sandy/ansible and set the password to notsafepw. Rekey the password to iwejfj2221.
===================================================================================
control.realmX.example.com _ workstation.lab.example.com
node1.realmX.example.com _ servera.lab.example.com
node2.realmX.example.com _ serverb.lab.example.com
node3.realmX.example.com _ serverc.lab.example.com
node4.realmX.example.com _ serverd.lab.example.com
node5.realmX.example.com
- username:root, password:redhat
- username:admin, password:redhat
note1. don’t change ‘root’ or ‘admin’ password.
note2. no need to create ssh-keygen for access, its pre-defined
note3. SELinux is in enforcing mode and firewalld is disabled/stop on whole managed hosts.
===================================================================================
Use Ansible Galaxy with a requirements file called /home/admin/ansible/roles/
install.yml to download and install roles to /home/admin/ansible/roles from the
following URLs:
http:// classroom.example.com /role1.tar.gz The name of this role should be balancer
http:// classroom.example.com /role2.tar.gz The name of this role should be phphello
===================================================================================
control.realmX.example.com _ workstation.lab.example.com
node1.realmX.example.com _ servera.lab.example.com
node2.realmX.example.com _ serverb.lab.example.com
node3.realmX.example.com _ serverc.lab.example.com
node4.realmX.example.com _ serverd.lab.example.com
node5.realmX.example.com
- username:root, password:redhat
- username:admin, password:redhat
note1. don’t change ‘root’ or ‘admin’ password.
note2. no need to create ssh-keygen for access, its pre-defined
note3. SELinux is in enforcing mode and firewalld is disabled/stop on whole managed hosts.
===================================================================================
Create and run an Ansible ad-hoc command.
--> As a system administrator, you will need to install software on the managed
nodes.
--> Create a shell script called yum-pack.sh that runs an Ansible ad-hoc command to
create yum-repository on each of the managed nodes as follows:
--> repository1
-----------
1. The name of the repository is EX407
2. The description is "Ex407 Description"
3. The base URL is http://content.example.com/rhel8.0/x86_64/dvd/BaseOS/
4. GPG signature checking is enabled
5. The GPG key URL is http://content.example.com/rhel8.0/x86_64/dvd/RPM-GPG-KEYredhat-
release
6. The repository is enabled
--> repository2
-----------
1. The name of the repository is EXX407
2. The description is "Exx407 Description"
3. The base URL is http://content.example.com/rhel8.0/x86_64/dvd/AppStream/
4. GPG signature checking is enabled
5. The GPG key URL is http://content.example.com/rhel8.0/x86_64/dvd/ RPM-GPG-KEYredhat-
release
6. The repository is enabled
===================================================================================
control.realmX.example.com _ workstation.lab.example.com
node1.realmX.example.com _ servera.lab.example.com
node2.realmX.example.com _ serverb.lab.example.com
node3.realmX.example.com _ serverc.lab.example.com
node4.realmX.example.com _ serverd.lab.example.com
node5.realmX.example.com
- username:root, password:redhat
- username:admin, password:redhat
note1. don’t change ‘root’ or ‘admin’ password.
note2. no need to create ssh-keygen for access, its pre-defined
note3. SELinux is in enforcing mode and firewalld is disabled/stop on whole managed hosts.
===================================================================================
Create a playbook called web.yml as follows:
* The playbook runs on managed nodes in the "dev" host group
* Create the directory /webdev with the following requirements:
--> membership in the apache group
--> regular permissions: owner=r+w+execute, group=r+w+execute, other=r+execute
s.p=set group-id
* Symbolically link /var/www/html/webdev to /webdev
* Create the file /webdev/index.html with a single line of text that reads:
“Developmentâ€
--> it should be available on http://servera.lab.example.com/webdev/index.html
Create a file called mysecret.yml on the control host using ansible vault in home/bob/ansible. Set the password to 'notasafepass' and inside the file create a variable called dev_pass with the value of devops. Save the file. Then go back in the file and change dev_pass value to devops123. Then change the vault password of mysecret.yml to verysafepass