Fortinet FCSS_EFW_AD-7.6 - Fortinet NSE 7 - Enterprise Firewall 7.6 Administrator
How do you allow IPS inspection of inbound HTTPS traffic?
An administrator configured the FortiGate devices in an enterprise network to join the Fortinet Security Fabric. The administrator has a list of IP addresses that must be blocked by the data center firewall. This list is updated daily.
How can the administrator automate a firewall policy with the daily updated list?
Refer to the exhibit.
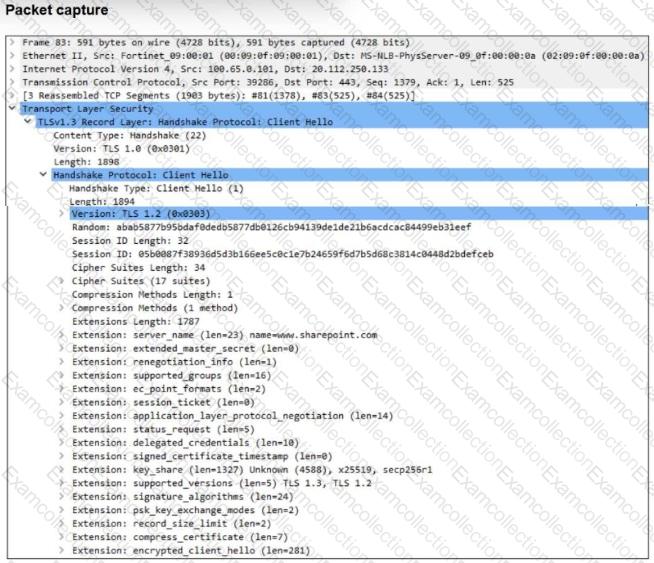
The packet capture output of a client hello message is shown.
You are updating a firewall policy that includes SSL certificate inspection. You are capturing packets from the traffic passing through this firewall policy.
Which two statements about the packet capture are correct? (Choose two.)
A vulnerability scan report has revealed that a user has generated traffic to the website example.com (10.10.10.10) using a weak SSL/TLS version supported by the HTTPS web server.
What can the firewall administrator do to block all outdated SSL/TLS versions on any HTTPS web server to prevent possible attacks on user traffic?
What can be inferred from the OSPF status output shown?
Refer to the exhibit, which shows a revision history window in the FortiManager device layer.
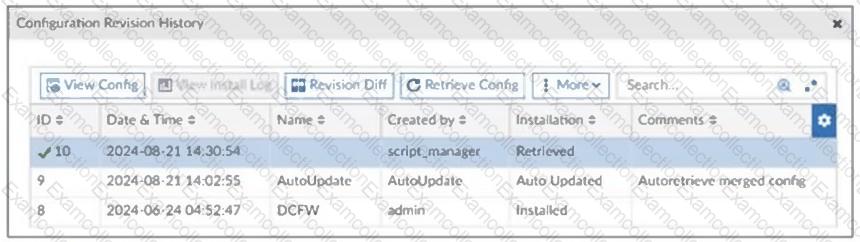
The IT team is trying to identify the administrator responsible for the most recent update in the FortiGate device database.
Which conclusion can you draw about this scenario?
Which action should you take after applying a block-all IPS profile that caused applications to stop working?
You applied a block-all intrusion prevention system (IPS) profile for client and server targets to secure the server but the database team reported that applications stopped working immediately after.
How can you apply IPS in a way that ensures it does not disrupt existing applications in the network?
To secure your enterprise network traffic, which step does FortiGate perform first, when handling the first packets of a session? (Choose one answer)
How can you automate updates to firewall policies using a daily updated IP block list?



