Fortinet FCSS_NST_SE-7.6 - Fortinet NSE 6 - Network Security 7.6 Support Engineer
Refer to the exhibit, which shows the omitted output of a session table entry.
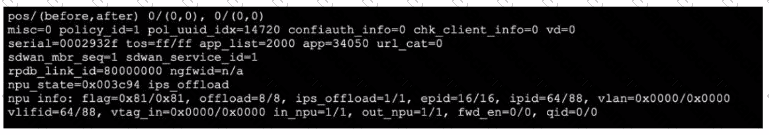
Which two statements are true? (Choose two.)
Refer to the exhibit.
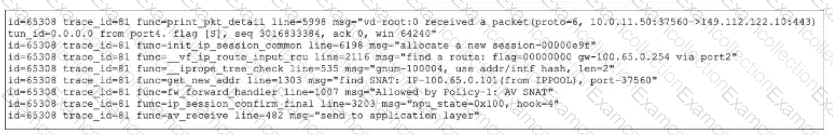
Which two observations can you make about the web filter traffic captured using the flow tool? (Choose two.)
In the SAML negotiation process, which section does the Identity Provider (IdP) provide the SAML attributes utilized in the authentication process to the Service Provider (SP)?
Refer to the exhibits.
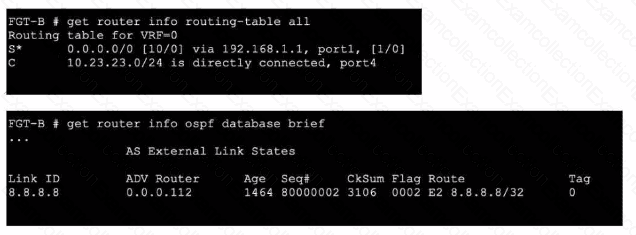
An administrator Is expecting to receive advertised route 8.8.8.8/32 from FGT-A. On FGT-B, they confirm that the route is being advertised and received, however, the route is not being injected into the routing table. What is the most likely cause of this issue?
Refer to the exhibits, which contain the partial configurations of two VPNs on FortiGate.
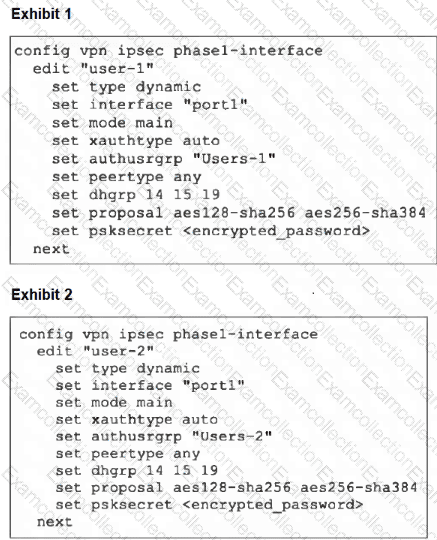
An administrator has configured two VPNs for two different user groups. Users who are in the Users-2 group are not able to connect to the VPN. After running a diagnostics command, the administrator discovers that FortiGate is not matching the user-2 VPN for members of the Users-2 group.
Which two changes must the administrator make to fix the issue? (Choose two.)
Which two statements about Security Fabric communications are true? (Choose two.)
When FortiGate enters conserve mode because of memory pressure, which action can FortiGate perform to preserve memory?
Refer to the exhibit.
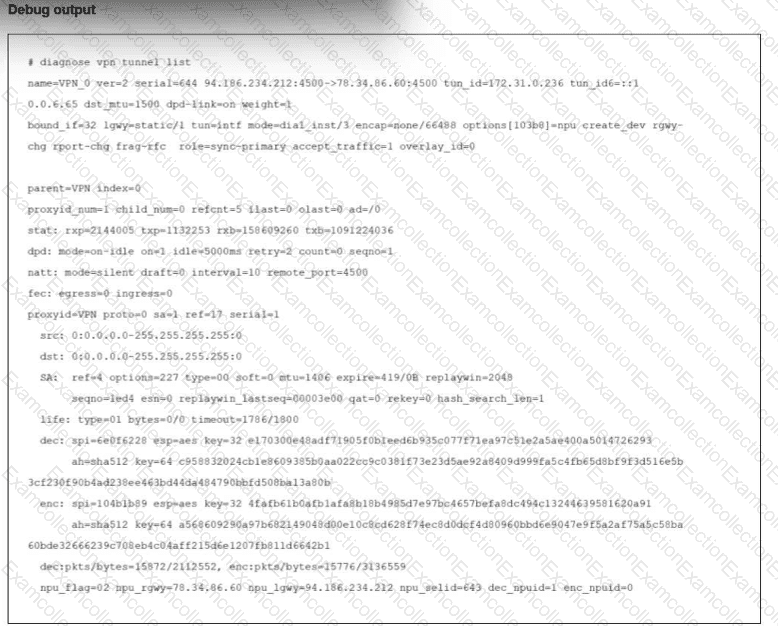
The output of the command diagnose vpn tunnel list is shown.
Reviewing the debug command, what is the current status of the traffic flowing through the tunnel?
Which three common FortiGate-to-collector-agent connectivity issues can you identify using the FSSO real-time debug? (Choose three.)
Which two protocol states indicate that traffic is bidirectional? (Choose two.)



