Huawei H12-711_V4.0 - HCIA-Security V4.0 Exam
_____ Authentication is to configure user information (including local user's user name, password and various attributes) on the network access server. The advantage is that it is fast.[fill in the blank]*
Which of the following statements are correct about IKE-based SA establishment in IPsec?
Which of the following authentication modes are supported by AAA?
Which of the following are the default zones of Huawei firewalls?
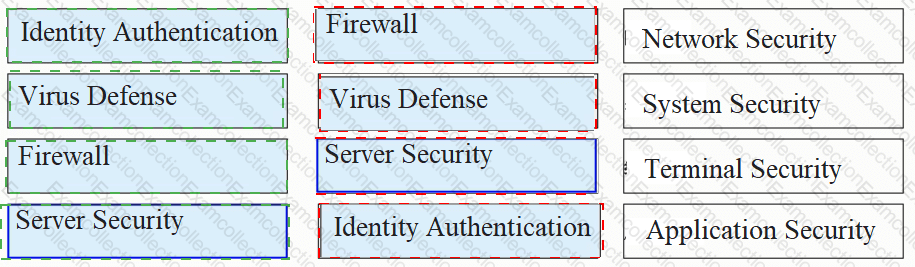
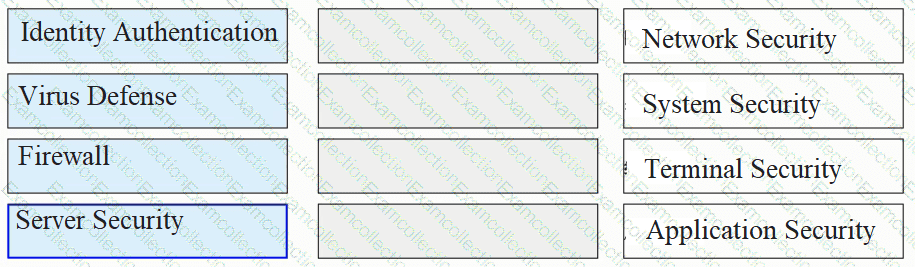
Please classify the following security defenses into the correct classification.
Which of the following are antivirus response actions of the firewall?
Which of the following descriptions of server authentication is correct?
Which of the following are application-layer protocols?
Which of the following is not the default security zone of the firewall
3-tuple NAT allows external devices to proactively access internal PCs through translated addresses and ports. Even if no security policy is configured on the firewall, the firewall allows such access packets to pass through.