Huawei H12-711_V4.0 - HCIA-Security V4.0 Exam
Which of the following is not the matching mode of the firewall security protection whitelist rules?
Which of the following problems cannot be solved using PKI?
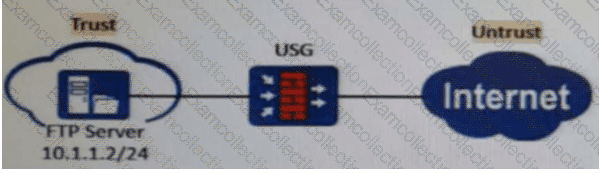
As shown in the figure, nat server global202.106.1.1 inside10.10.1.1 is configured on the firewall. Which of the following is the correct configuration for interzone rules?
IPSec VPN uses an asymmetric algorithm to calculate the ___ key to encrypt data packets.[fill in the blank]
Which of the following types of malicious code on your computer includes?
Please order the following steps in the PKI life cycle correctly, 1. Issued, 2. storage, 3. Update, 4. verify[fill in the blank]*
In asymmetric encryption algorithms, only public keys can be used to encrypt data, and private keys are used to decrypt data. This process is irreversible.
In the Linux system, which of the following is the command to query the P address information?
Which of the following statements is incorrect about information transmission through the heartbeat link between two firewalls that work in hot standby mode?
Certificates saved in DER format may or may not contain a private key.



