HP HPE6-A78 - Aruba Certified Network Security Associate Exam
What is an Authorized client, as defined by AOS Wireless Intrusion Prevention System (WIP)?
Your company policies require you to encrypt logs between network infrastructure devices and Syslog servers. What should you do to meet these requirements on an ArubaOS-CX switch?
What is symmetric encryption?
You have configured a WLAN to use Enterprise security with the WPA3 version.
How does the WLAN handle encryption?
You are deploying a new wireless solution with an HPE Aruba Networking Mobility Master (MM), Mobility Controllers (MCs), and campus APs (CAPs). The solution will include a WLAN that uses Tunnel for the forwarding mode and WPA3-Enterprise for the security option.
You have decided to assign the WLAN to VLAN 301, a new VLAN. A pair of core routing switches will act as the default router for wireless user traffic.
Which links need to carry VLAN 301?
Your HPE Aruba Networking Mobility Master-based solution has detected a rogue AP. Among other information, the AOS Detected Radios page lists this information for the AP:
SSID = PublicWiFi
BSSID = a8:bd:27:12:34:56
Match method = Plus one
Match method = Eth-Wired-Mac-Table
The security team asks you to explain why this AP is classified as a rogue. What should you explain?
Refer to the exhibit.
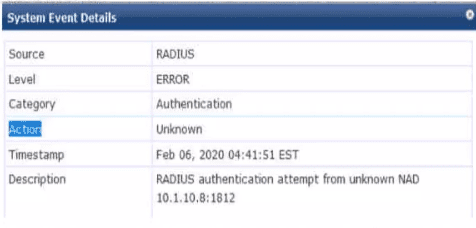
You are deploying a new ArubaOS Mobility Controller (MC), which is enforcing authentication to Aruba ClearPass Policy Manager (CPPM). The authentication is not working correctly, and you find the error shown In the exhibit in the CPPM Event Viewer.
What should you check?
What purpose does an initialization vector (IV) serve for encryption?
You have an Aruba Mobility Controller (MC). for which you are already using Aruba ClearPass Policy Manager (CPPM) to authenticate access to the Web Ul with usernames and passwords You now want to enable managers to use certificates to log in to the Web Ul CPPM will continue to act as the external server to check the names in managers' certificates and tell the MC the managers' correct rote
in addition to enabling certificate authentication. what is a step that you should complete on the MC?
You are troubleshooting an authentication issue for HPE Aruba Networking switches that enforce 802.1X to a cluster of HPE Aruba Networking ClearPass Policy Manager (CPPMs). You know that CPPM is receiving and processing the authentication requests because the Aruba switches are showing Access-Rejects in their statistics. However, you cannot find the record for the Access-Rejects in CPPM Access Tracker.
What is something you can do to look for the records?



