HP HPE6-A78 - Aruba Certified Network Security Associate Exam
An ArubaOS-CX switch enforces 802.1X on a port. No fan-through options or port-access roles are configured on the port The 802 1X supplicant on a connected client has not yet completed authentication
Which type of traffic does the authenticator accept from the client?
What is one benefit of enabling Enhanced Secure mode on an ArubaOS-Switch?
A company has an ArubaOS solution. The company wants to prevent users assigned to the "user_group1" role from using gaming and peer-to-peer applications.
What is the recommended approach for these requirements?
What is one way a honeypot can be used to launch a man-in-the-middle (MITM) attack to wireless clients?
You are deploying a new wireless solution with an Aruba Mobility Master (MM). Aruba Mobility Controllers (MCs), and campus APs (CAPs). The solution will include a WLAN that uses Tunnel for the forwarding mode and WPA3-Enterprise for the security option.
You have decided to assign the WLAN to VLAN 301, a new VLAN. A pair of core routing switches will act as the default router for wireless user traffic.
Which links need to carry VLAN 301?
What distinguishes a Distributed Denial of Service (DDoS) attack from a traditional Denial of Service (DoS) attack?
What is a reason to set up a packet capture on an Aruba Mobility Controller (MC)?
Refer to the exhibit.
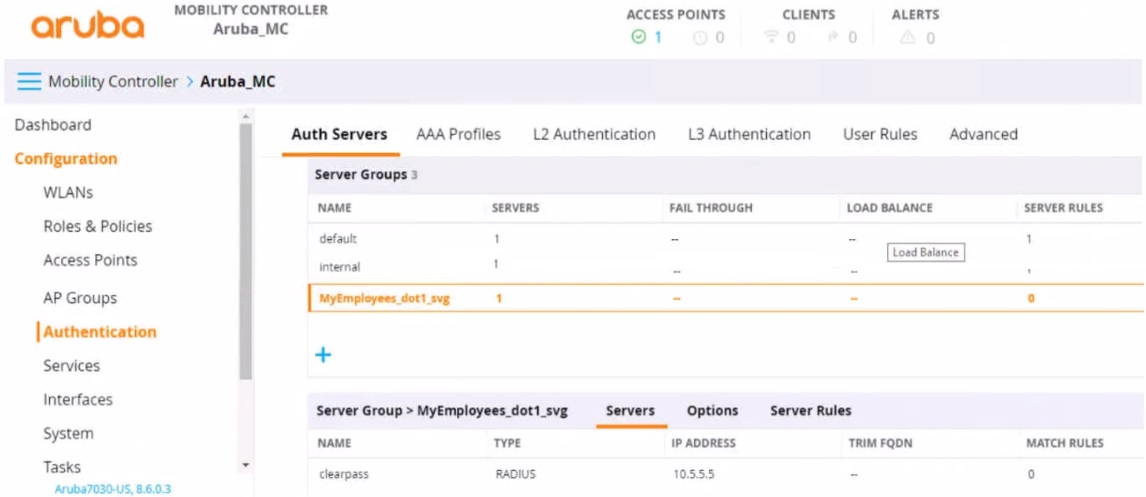
You have set up a RADIUS server on an ArubaOS Mobility Controller (MC) when you created a WLAN named "MyEmployees .You now want to enable the MC to accept change of authorization (CoA) messages from this server for wireless sessions on this WLAN.
What Is a part of the setup on the MC?
A customer has an AOS-10 network infrastructure. The customer is looking for a solution that can classify many different types of devices, including IoT devices. Which solution should you explain can provide these capabilities?
An MC has a WLAN that enforces WPA3-Enterprise with authentication to HPE Aruba Networking ClearPass Policy Manager (CPPM). The WLAN's default role is set to guest. A Mobility Controller (MC) has these roles configured on it:
authenticated
denyall
guest
general-access
guest-logon
logon
stateful-dot1x
switch-logon
voiceA client authenticates. CPPM returns an Access-Accept with an Aruba-User-Role VSA set to general_access. What role does the client receive?



