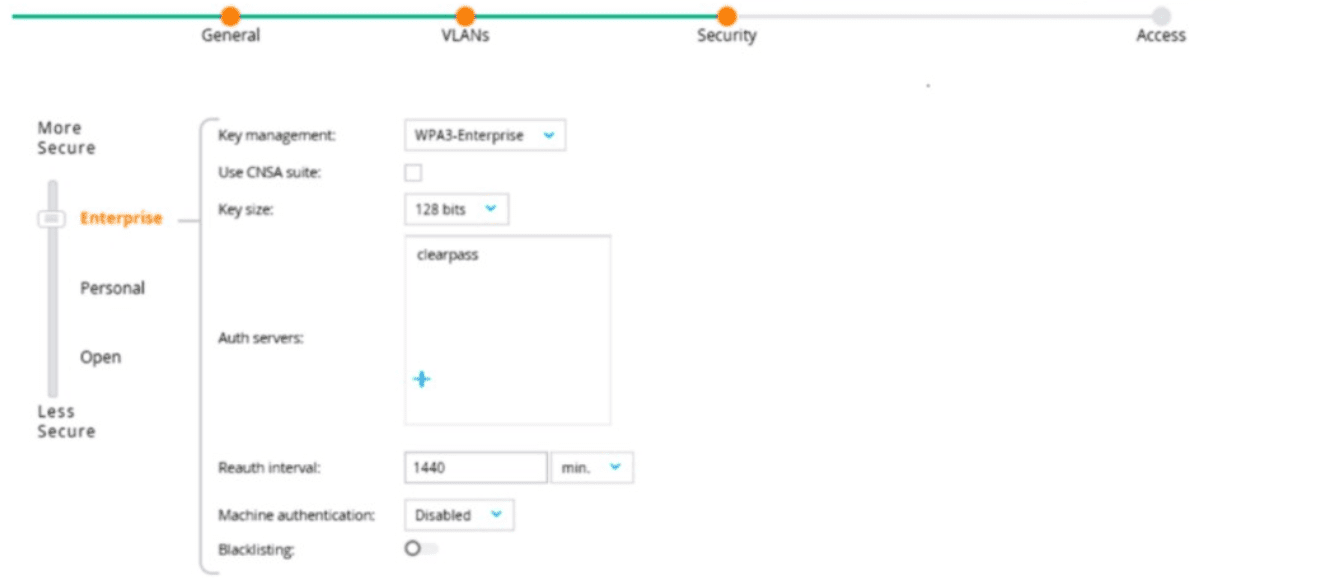
The exhibit shows the configuration of a WLAN on an AOS-8 Mobility Controller (MC) with the following settings:
Key management: WPA3-Enterprise (indicating 802.1X authentication).
Use CNSA suite: Unchecked (using standard encryption, not the Commercial National Security Algorithm suite).
Key size: 128 bits (standard for AES-GCMP in WPA3).
Reauth interval: 1440 minutes (24 hours, the interval for re-authentication).
Machine authentication: Disabled (only user authentication is required).
Blacklisting: Disabled (clients are not blacklisted after failed attempts).
The question states that the AAA profile settings have not been adjusted, meaning the default roles (e.g., initial role, logon role, 802.1X default role) are not specified in the exhibit and are assumed to be the system defaults (e.g., "logon" for the initial and logon roles, and a default role like "guest" for the 802.1X default role). The question asks under which circumstances a client will receive the "default role assignment," which refers to the 802.1X default role configured in the AAA profile for the WLAN.
802.1X Authentication Process in AOS-8:
When a client connects to a WPA3-Enterprise WLAN, it starts in the initial role (typically "logon") to allow basic connectivity (e.g., DHCP, DNS).
During 802.1X authentication, the client is placed in the logon role to allow communication with the authentication server (e.g., ClearPass Policy Manager, CPPM).
If authentication succeeds, the client is assigned a role:
If the authentication server (e.g., CPPM) sends an Aruba-User-Role VSA with a role that exists on the MC, the client is assigned that role.
If no Aruba-User-Role VSA is sent, the client is assigned the 802.1X default role configured in the AAA profile for the WLAN.
If authentication fails or the server is unreachable, the client may be assigned a different role (e.g., a critical role, if configured) or denied access.
Option A, "The client has attempted 802.1X authentication, but the MC could not contact the authentication server," is incorrect. If the MC cannot contact the authentication server (e.g., due to a timeout), the client does not receive the 802.1X default role. Instead, the MC may apply a critical role (if configured) or deny access, depending on the configuration. The 802.1X default role is applied only after successful authentication.
Option B, "The client has passed 802.1X authentication, and the authentication server did not send an Aruba-User-Role VSA," is correct. If the client successfully authenticates via 802.1X and the authentication server (e.g., CPPM) does not send an Aruba-User-Role VSA, the MC assigns the client the 802.1X default role configured in the AAA profile for the WLAN. This is the "default role assignment" referred to in the question.
Option C, "The client has attempted 802.1X authentication, but failed to maintain a reliable connection, leading to a timeout error," is incorrect. A timeout error during authentication (e.g., the client fails to respond to EAP messages) typically results in an authentication failure, not a successful authentication. The client would not receive the 802.1X default role; it might be denied access or placed in a different role (e.g., a pre-authentication role).
Option D, "The client has passed 802.1X authentication, and the value in the Aruba-User-Role VSA matches a role on the MC," is incorrect. If the authentication server sends an Aruba-User-Role VSA with a role that exists on the MC, the client is assigned that specific role, not the 802.1X default role.
The HPE Aruba Networking AOS-8 8.11 User Guide states:
"After a client successfully authenticates via 802.1X, the Mobility Controller assigns a role to the client. If the authentication server (e.g., a RADIUS server) sends an Aruba-User-Role VSA with a role that exists on the controller, the client is assigned that role. If no Aruba-User-Role VSA is sent in the Access-Accept message, the client is assigned the 802.1X default role configured in the AAA profile for the WLAN. For example, if the AAA profile specifies ‘guest’ as the 802.1X default role, the client will be assigned the ‘guest’ role." (Page 305, Role Assignment Section)
Additionally, the HPE Aruba Networking Wireless Security Guide notes:
"In WPA3-Enterprise with 802.1X authentication, the default role assignment occurs when a client successfully authenticates but the authentication server does not specify a role via the Aruba-User-Role VSA. In this case, the client receives the 802.1X default role defined in the AAA profile, such as ‘guest’ or another role configured by the administrator." (Page 42, 802.1X Role Assignment Section)
[References:, HPE Aruba Networking AOS-8 8.11 User Guide, Role Assignment Section, Page 305., HPE Aruba Networking Wireless Security Guide, 802.1X Role Assignment Section, Page 42.===========]