Juniper JN0-351 - Enterprise Routing and Switching Specialist (JNCIS-ENT)
You enable persistent MAC learning on your Juniper switch
In this scenario, which statement is correct?
Two routers share the same highest priority and start time.
You are concerned about spoofed MAC addresses on your LAN.
Which two Layer 2 security features should you enable to minimize this concern? (Choose two.)
You implemented the MAC address limit feature with the shutdown action on all interfaces on your switch.
In this scenario, which statement is correct when a violation occurs?
Exhibit.
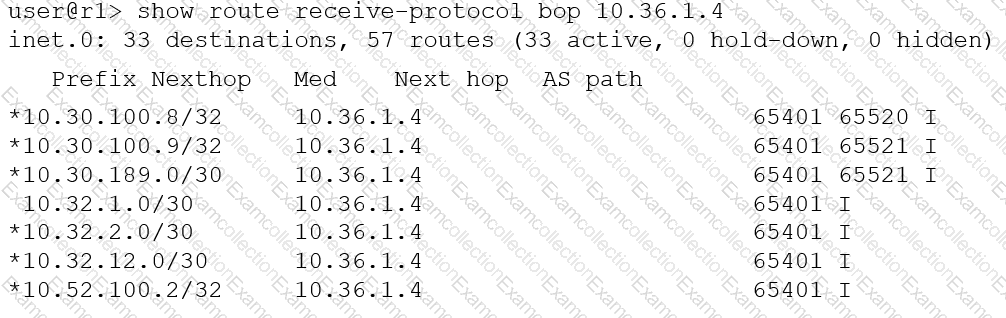
You want to verify prefix information being sent from 10.36.1.4.
Which two statements are correct about the output shown in the exhibit? (Choose two.)
Exhibit
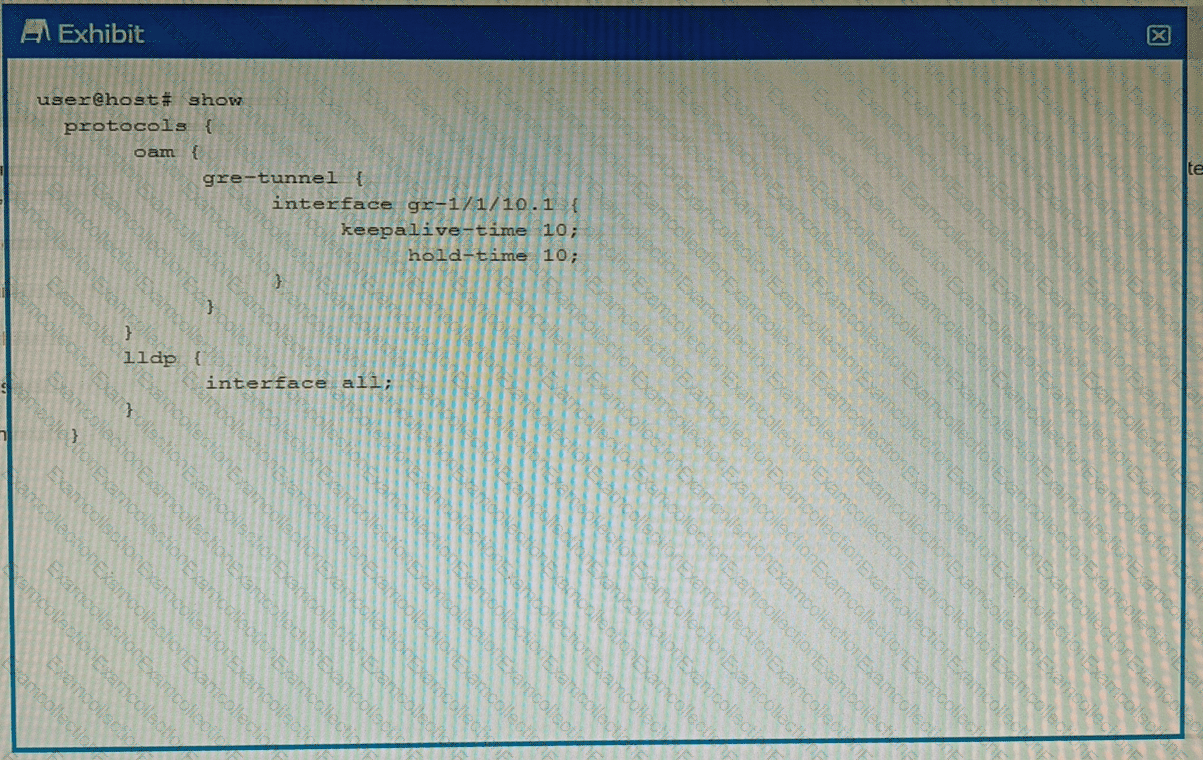
You have configured a GRE tunnel. To reduce the risk of dropping traffic, you have configured a keepalive OAM probe to monitor the state of the tunnel; however, traffic drops are still occurring.
Referring to the exhibit, what is the problem?
In a LAN segment, which tie-breaker would spanning tree consider if equal-cost paths exist between two or more switches to the root bridge?
Which two statements are true about the default VLAN on Juniper switches? (Choose two.)
You are asked to create a default route that will be advertised to your internal OSPF neighbors. You have three upstream connections to the Internet and you must ensure that when available, all traffic uses ISP1 as your primary connection and only uses ISP2 and ISP3 when ISP1 is not available.
Which solution should you implement in this scenario?
After receiving a BGP route, which two conditions are verified by the receiving router to ensure that the received route is valid? (Choose two)



