CompTIA N10-009 - CompTIA Network+ Certification Exam
After a security incident, a technician reveals that company data was stolen. During the investigation, it is discovered that a host disguised itself as a switch. Which of the following best describes the attack that occurred?
A network administrator is troubleshooting issues with a DHCP server at a university. More students have recently arrived on campus, and the users are unable to obtain an IP address. Which of the following should the administrator do to address the issue?
Which of the following network topologies contains a direct connection between every node in the network?
Which of the following must be implemented to securely connect a company ' s headquarters with a branch location?
Which of the following network traffic type is sent to all nodes on the network?
A network administrator is developing a method of device monitoring with the following requirements:
•Allows for explicit, by user, privilege management
•Includes centralized logging of changes
•Offers widely accessible remote management
•Provides support of service accounts
Which of the following will most closely meet these requirements?
A technician is planning an equipement installation into a rack in a data center that practices hot aisle/cold aise ventilation. Which of the following directions should the equipement exhaust face when installed in the rack?
A company security policy requires all network traffic from remote employees ' corporate laptops to use the company’s VPN. Which of the following network access methods best describes this scenario?
A customer needs six usable IP addresses. Which of the following best meets this requirement?
Which of the following is the most cost-efficient way to host email services?
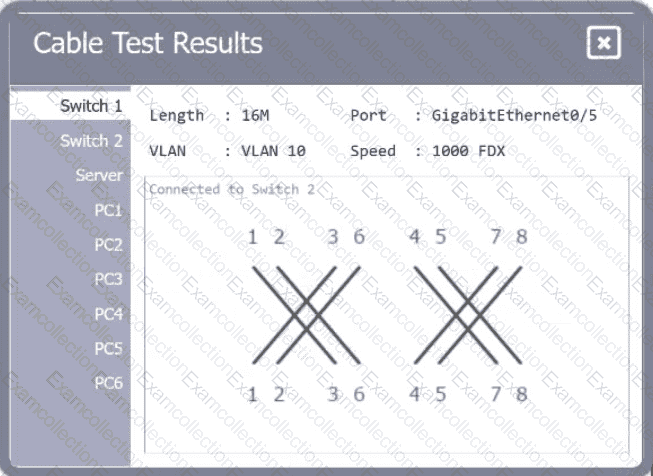
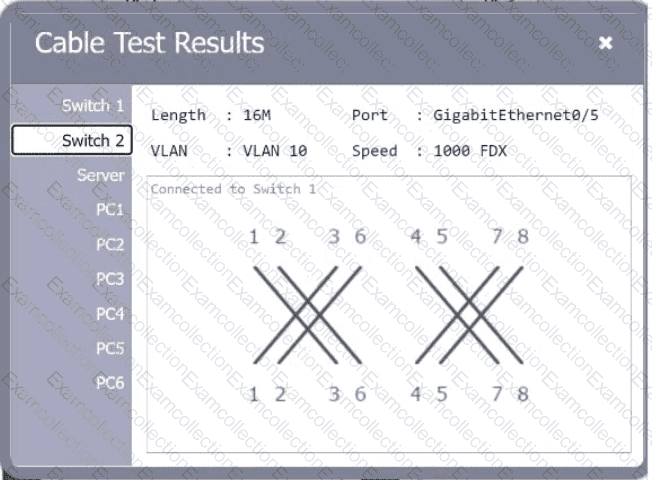
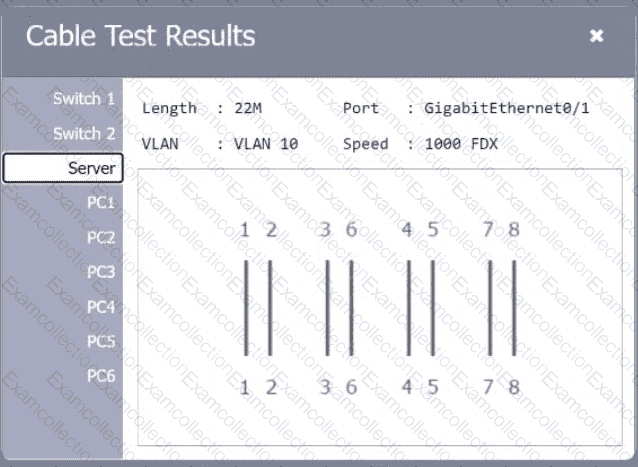
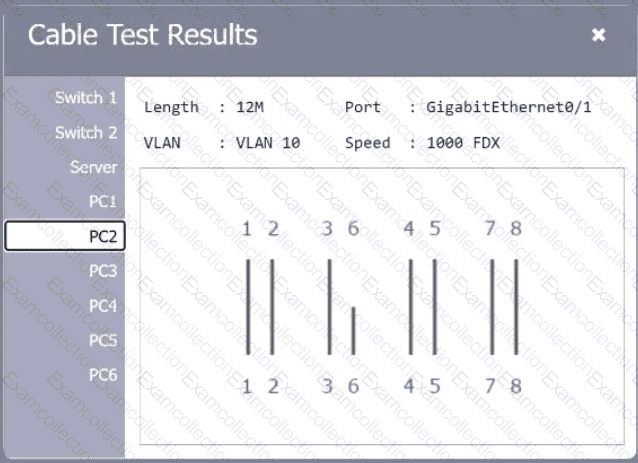
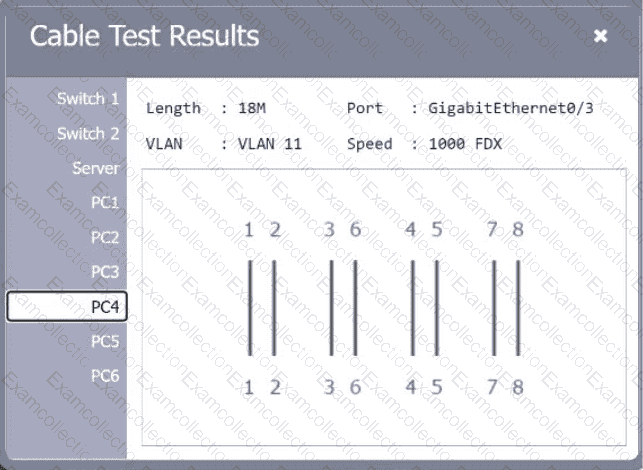
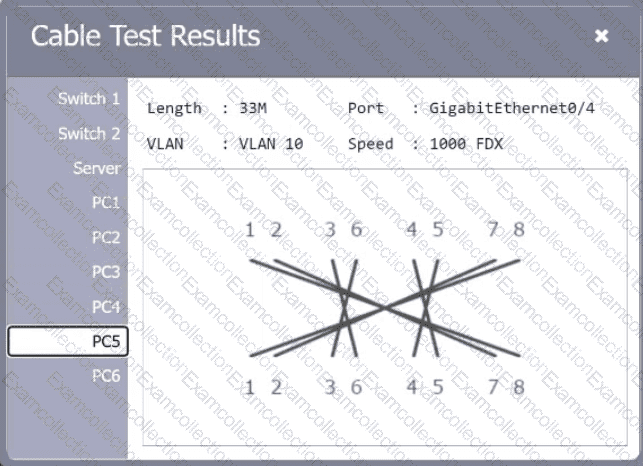
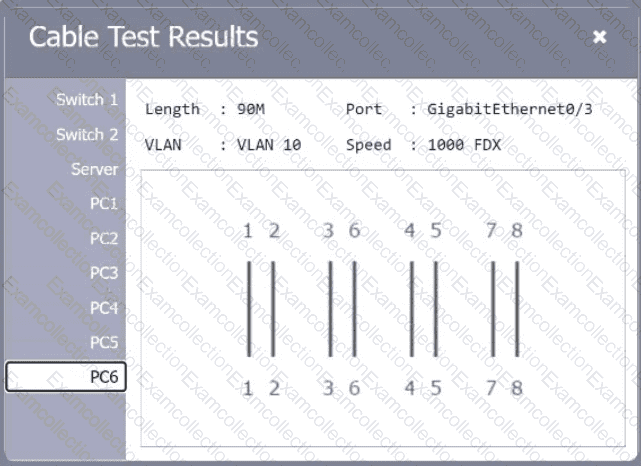
A network technician needs to resolve some issues with a customer ' s SOHO network. The
customer reports that some of the PCs are not connecting to the network, while others
appear to be working as intended.
INSTRUCTIONS
Troubleshoot all the network components.
Review the cable test results first, then diagnose by clicking on the appropriate PC,
server, and Layer 2 switch.
Identify any components with a problem and recommend a solution to correct each
problem.
If at any time you would like to bring back
the initial state of the simulation, please
click the Reset All button.
A network administrator is configuring a network for a new site that will have 150 users. Within the next year, the site is expected to grow by ten users. Each user will have two IP addresses, one for a computer and one for a phone connected to the network. Which of the following classful IPv4 address ranges will be best-suited for the network?
Which of the following standards enables the use of an enterprise authentication for network access control?
Which of the following best describes a characteristic of a DNS poisoning attack?
Which of the following is the step that a troubleshooter should take immediately after implementing a solution?



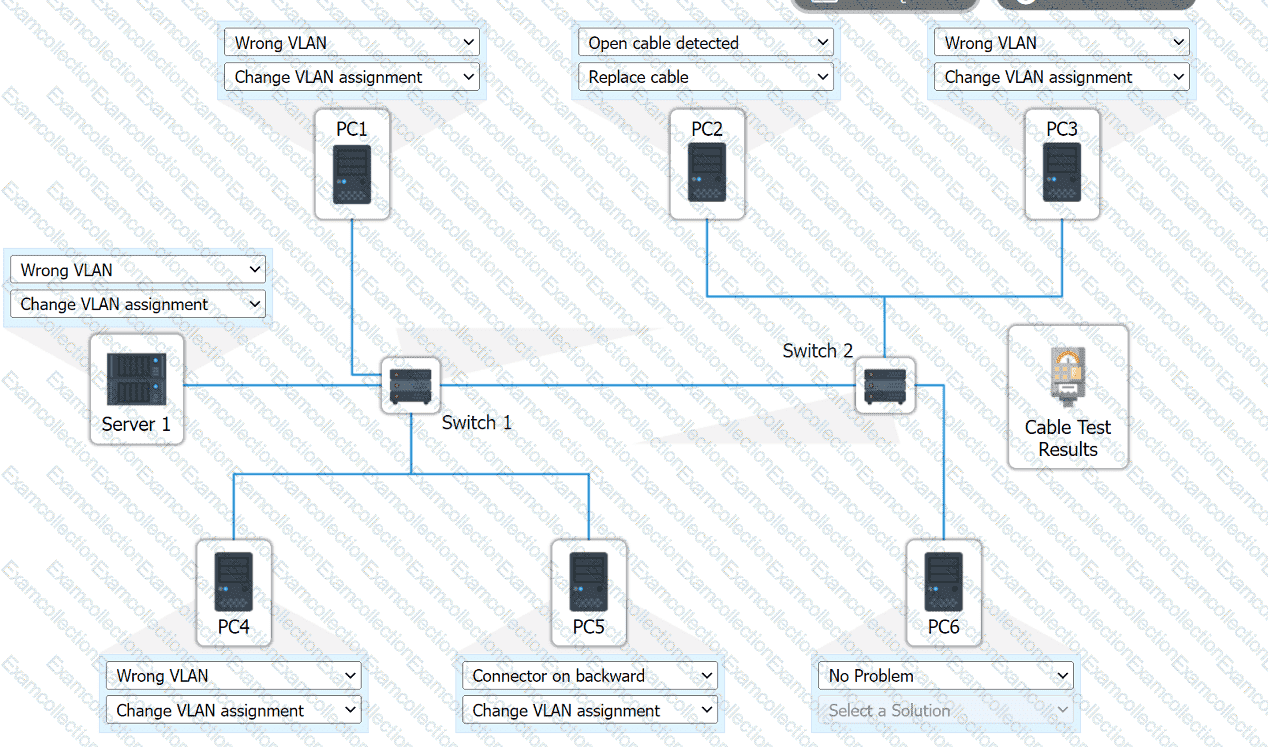 A computer network diagram with many boxes and text AI-generated content may be incorrect.
A computer network diagram with many boxes and text AI-generated content may be incorrect.