Proofpoint PPAN01 - Certified Threat Protection Analyst Exam
Exhibit:

Which column indicates the number of users targeted by a malicious campaign or threat?
Evidence of an attack is no longer present due to a scheduled data purge. What would be the appropriate recommendation?
Which of the following is an item that should be included in an incident report as part of the post-incident debrief?
You would like to view the total number of uncleared threats or false positives that have been interacted with by users over the past 2 weeks. How can this be accomplished on the TAP Dashboard?
What is the primary function of the People Page in the Threat Protection Workbench and TAP Dashboard?
A college student receives the email shown in the exhibit.
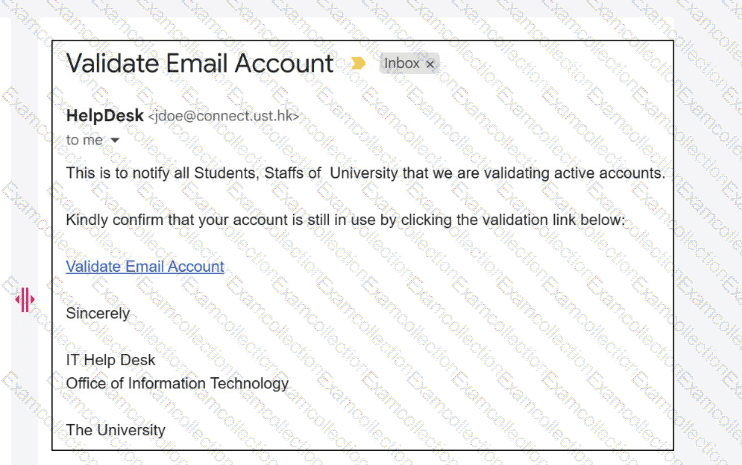
What type of attack is being performed?
In which part of the SMTP conversation can threat actors spoof information to make the message look safe to the recipient?
Based on the exhibit,
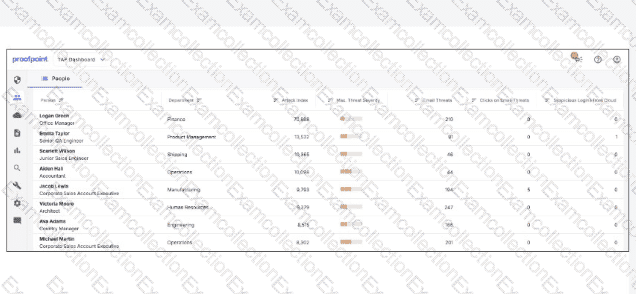
which user would most benefit from attending security awareness training based on their behavior?
The Attack Index is a calculation of the overall threat burden for a particular user. Which listed factor contributes to this calculation?
Which two items should be included in an incident report to be discussed during a post-incident debrief? (Select two.)



