CompTIA PT0-003 - CompTIA PenTest+ Exam
A penetration tester identifies the URL for an internal administration application while following DevOps team members on their commutes. Which of the following attacks did the penetration tester most likely use?
During an assessment, a penetration tester runs the following command:
dnscmd.exe /config /serverlevelplugindll C:\users\necad-TA\Documents\adduser.dll
Which of the following is the penetration tester trying to achieve?
A penetration tester wants to automatically enumerate all ciphers permitted on TLS/SSL configurations across a client’s internet-facing and internal web servers. Which of the following tools or frameworks best supports this objective?
During a security assessment, a penetration tester needs to exploit a vulnerability in a wireless network ' s authentication mechanism to gain unauthorized access to the network. Which of the following attacks would the tester most likely perform to gain access?
As part of an engagement, a penetration tester wants to maintain access to a compromised system after rebooting. Which of the following techniques would be best for the tester to use?
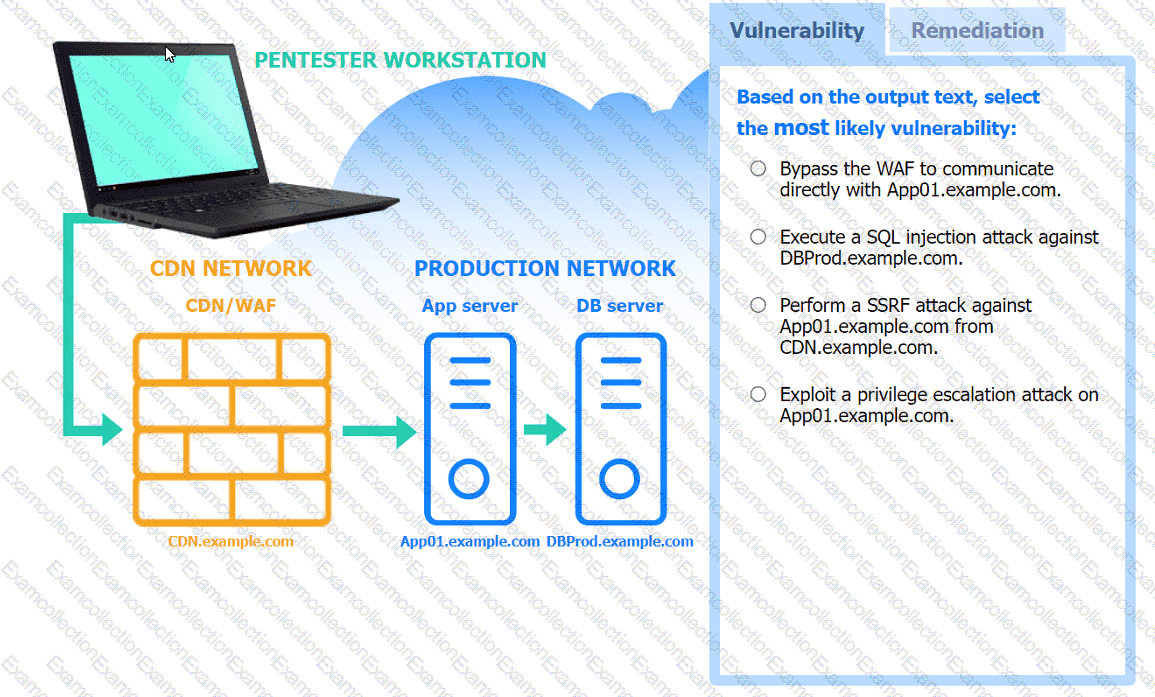
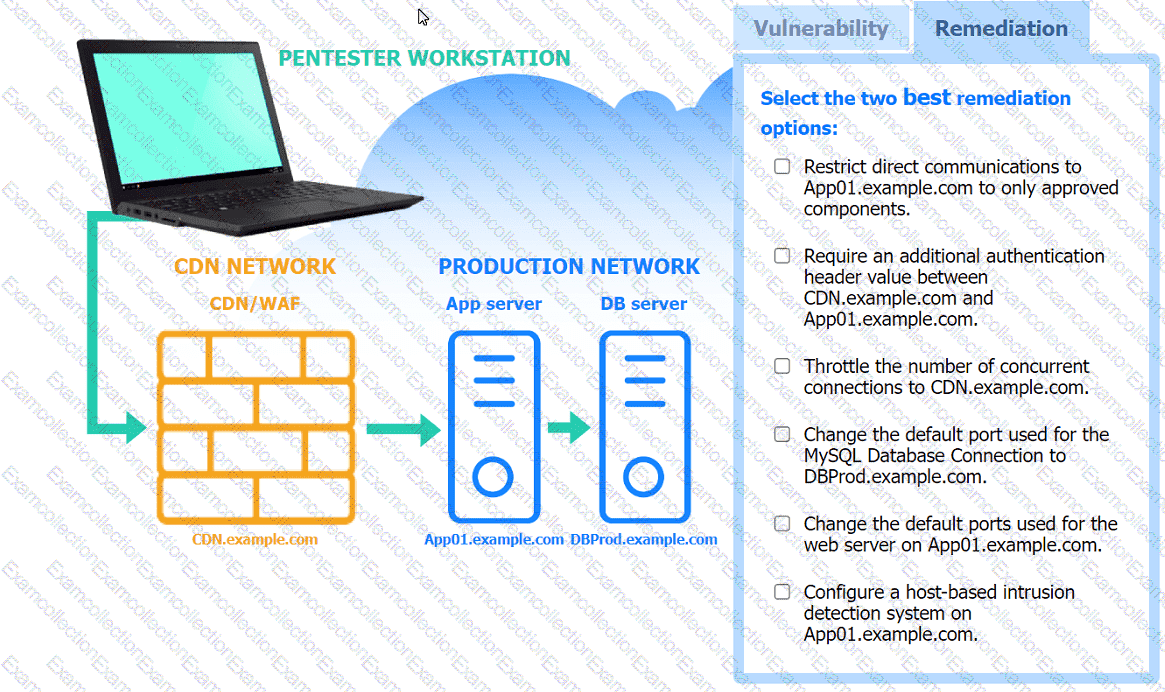
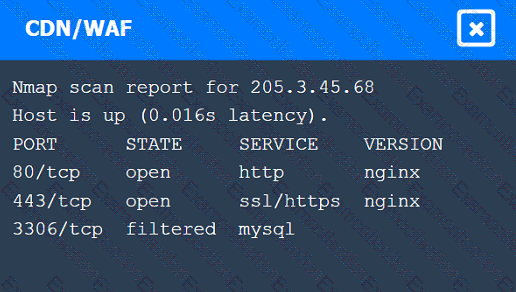
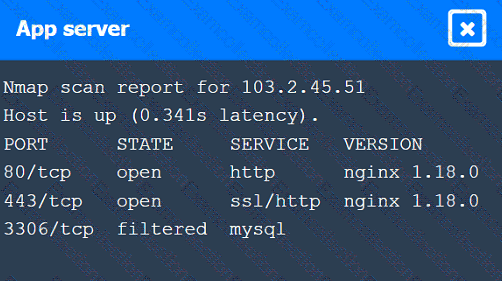
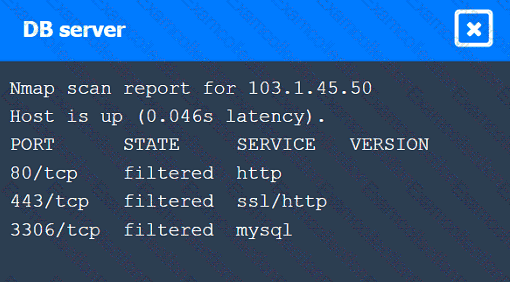
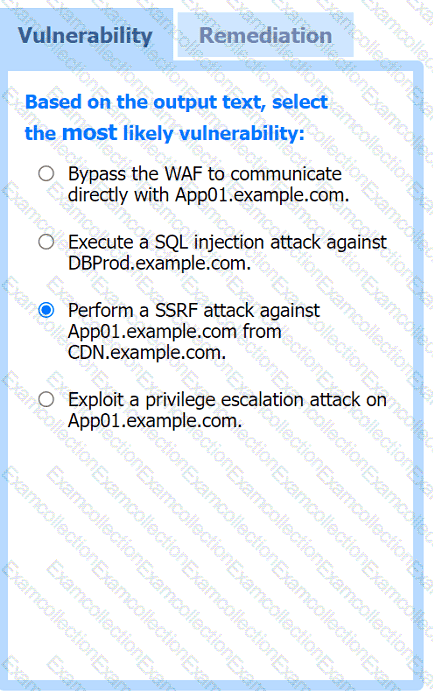
A penetration tester performs several Nmap scans against the web application for a client.
INSTRUCTIONS
Click on the WAF and servers to review the results of the Nmap scans. Then click on
each tab to select the appropriate vulnerability and remediation options.
If at any time you would like to bring back the initial state of the simulation, please
click the Reset All button.
A penetration tester downloads a JAR file that is used in an organization ' s production environment. The tester evaluates the contents of the JAR file to identify potentially vulnerable components that can be targeted for exploit. Which of the following describes the tester ' s activities?
A penetration tester gains access to a Windows machine and wants to further enumerate users with native operating system credentials. Which of the following should the tester use?
Which of the following activities should be performed to prevent uploaded web shells from being exploited by others?
An internal penetration tester is on site assessing network access for company-owned mobile devices. Which of the following would be the best tool to identify the available networks?



 A screenshot of a computer Description automatically generated
A screenshot of a computer Description automatically generated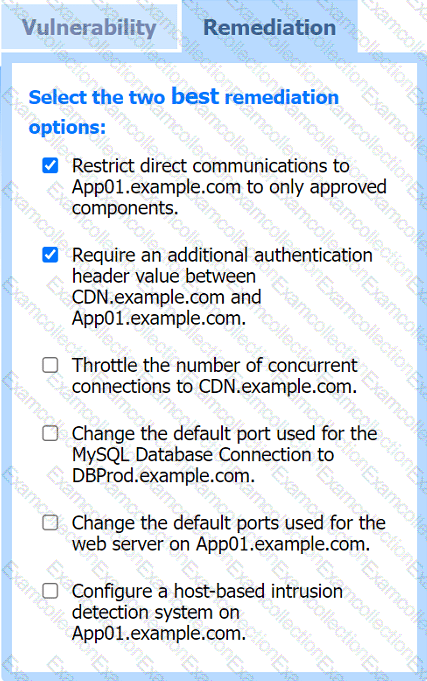 A screenshot of a computer screen Description automatically generated
A screenshot of a computer screen Description automatically generated