CompTIA PT0-003 - CompTIA PenTest+ Exam
A penetration tester conducts OSINT for a client and discovers the robots.txt file explicitly blocks a major search engine. Which of the following would most likely help the penetration tester achieve the objective?
A penetration tester is working on an engagement in which a main objective is to collect confidential information that could be used to exfiltrate data and perform a ransomware attack. During the engagement, the tester is able to obtain an internal foothold on the target network. Which of the following is the next task the tester should complete to accomplish the objective?
A penetration tester is conducting an assessment of offline systems that control a power plant. The tester is looking for vulnerabilities observable in the network stack. The rules of engagement state that the tester cannot interact with production systems. Which of the following tools or techniques should the tester use for the assessment?
During a discussion of a penetration test final report, the consultant shows the following payload used to attack a system:
html
Copy code
7/ < sCRitP > aLeRt( ' pwned ' ) < /ScriPt >
Based on the code, which of the following options represents the attack executed by the tester and the associated countermeasure?
A company hires a penetration tester to test the security implementation of its wireless networks. The main goal for this assessment is to intercept and get access to sensitive data from the company ' s employees. Which of the following tools should the security professional use to best accomplish this task?
A penetration tester needs to identify all vulnerable input fields on a customer website. Which of the following tools would be best suited to complete this request?
Which of the following OT protocols sends information in cleartext?
Which of the following would most likely reduce the possibility of a client rejecting the final deliverable for a penetration test?
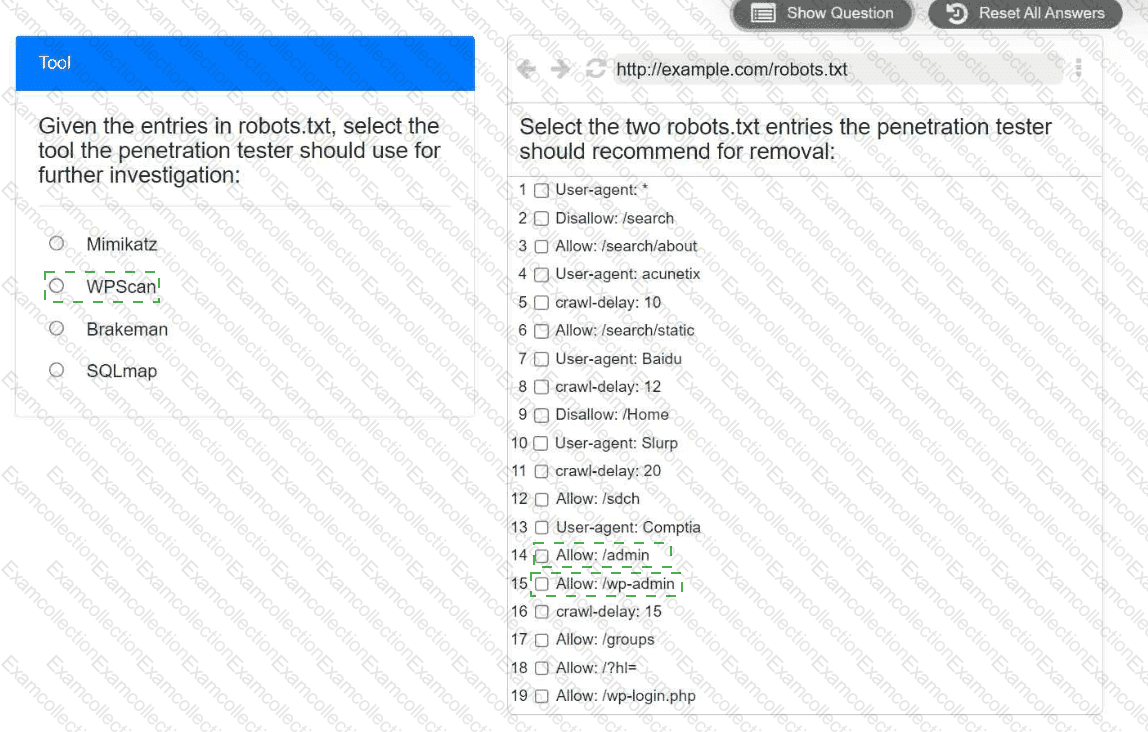
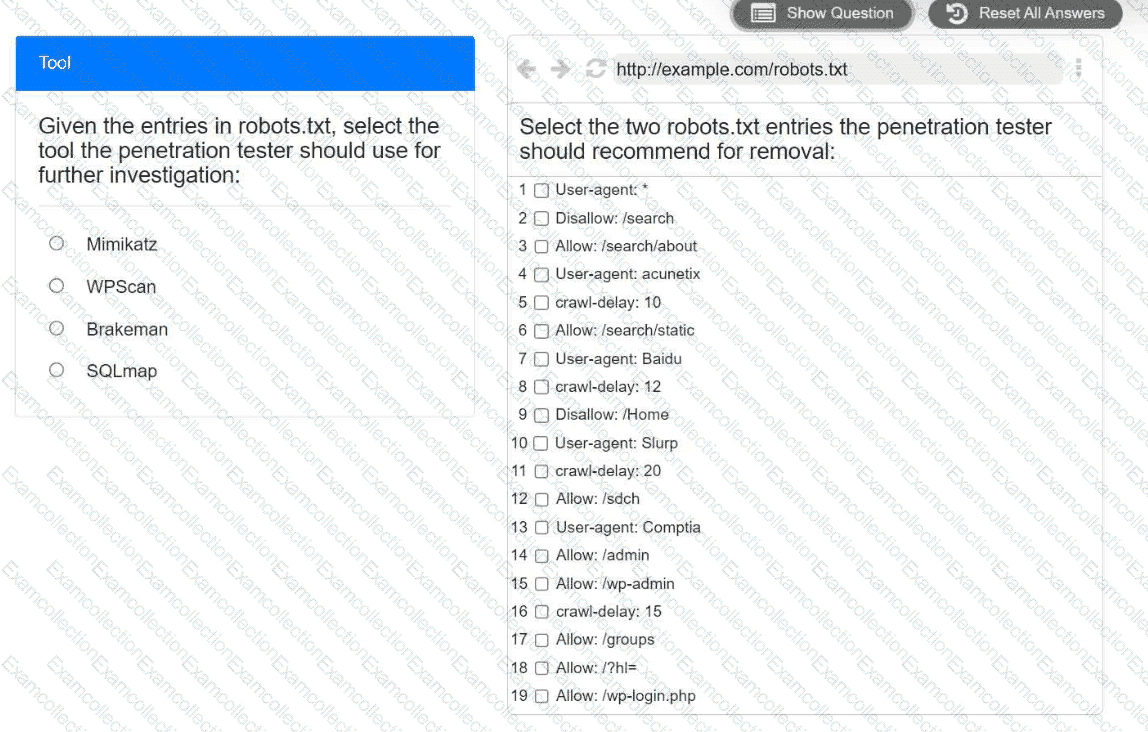
A penetration tester is performing reconnaissance for a web application assessment. Upon investigation, the tester reviews the robots.txt file for items of interest.
INSTRUCTIONS
Select the tool the penetration tester should use for further investigation.
Select the two entries in the robots.txt file that the penetration tester should recommend for removal.
Which of the following explains the reason a tester would opt to use DREAD over PTES during the planning phase of a penetration test?