Google Professional-Cloud-Network-Engineer - Google Cloud Certified - Professional Cloud Network Engineer
Total 233 questions
You just finished your company’s migration to Google Cloud and configured an architecture with 3 Virtual Private Cloud (VPC) networks: one for Sales, one for Finance, and one for Engineering. Every VPC contains over 100 Compute Engine instances, and now developers using instances in the Sales VPC and the Finance VPC require private connectivity between each other. You need to allow communication between Sales and Finance without compromising performance or security. What should you do?
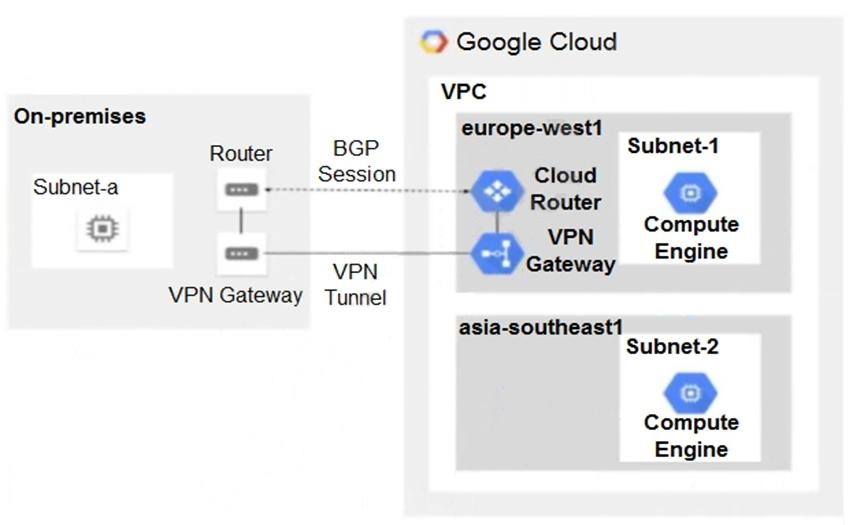
You have the following routing design. You discover that Compute Engine instances in Subnet-2 in the asia-southeast1 region cannot communicate with compute resources on-premises. What should you do?
You need to create a GKE cluster in an existing VPC that is accessible from on-premises. You must meet the following requirements:
IP ranges for pods and services must be as small as possible.
The nodes and the master must not be reachable from the internet.
You must be able to use kubectl commands from on-premises subnets to manage the cluster.
How should you create the GKE cluster?
You are designing a shared VPC architecture. Your network and security team has strict controls over which routes are exposed between departments. Your Production and Staging departments can communicate with each other, but only via specific networks. You want to follow Google-recommended practices.
How should you design this topology?
Your company's on-premises office is connected to Google Cloud using HA VPN. The security team will soon enable VPC Service Controls. You need to create a plan with minimal configuration adjustments, so clients at the office will still be able to privately call the Google APIs and be protected by VPC Service Controls. What should you do?
Question:
You reviewed the user behavior for your main application, which uses an external global Application Load Balancer, and found that the backend servers were overloaded due to erratic spikes in client requests. You need to limit concurrent sessions and return an HTTP 429 "Too Many Requests" response back to the client while following Google-recommended practices. What should you do?
You create multiple Compute Engine virtual machine instances to be used as TFTP servers.
Which type of load balancer should you use?



