Microsoft SC-401 - Administering Information Security in Microsoft 365
Note: This question is part of a series of questions that present the same scenario. Each question in the series contains a unique solution that might meet the stated goals. Some question sets might have more than one correct solution, while others might not have a correct solution.
After you answer a question in this section, you will NOT be able to return to it. As a result, these questions will not appear in the review screen.
You have a Microsoft 365 tenant and 500 computers that run Windows 11. The computers are onboarded to Microsoft Purview.
You discover that a third-party application named Tailspin_scanner.exe accessed protected sensitive information on multiple computers. Tailspin_scanner.exe is installed locally on the computers.
You need to block Tailspin_scanner.exe from accessing sensitive documents without preventing the application from accessing other documents.
Solution: From Microsoft Defender for Cloud Apps, you create an app discovery policy.
Does this meet the goal?
You need to provide a user with the ability to view data loss prevention (DIP) alerts in the Microsoft Purview portal. The solution must use the principle of least privilege.
Which role should you assign to the user?
You have a Microsoft 365 E5 subscription.
You plan to deploy Microsoft Purview Data Security Posture Management for Al (DSPM for Al) to protect company data that contains Personally Identifiable Information (Pll) from being shared with third-party generative Al tools.
You need to complete the prerequisites for the planned deployment.
Which two Microsoft Purview solutions should you use? Each correct answer presents part of the solution.
NOTE: Each correct selection is worth one point.
You need to test Microsoft Purview Advanced Message Encryption capabilities for your company. The test must verify the following information:
• The acquired default template names
• The encryption and decryption verification status
Which PowerShell cmdlet should you run?
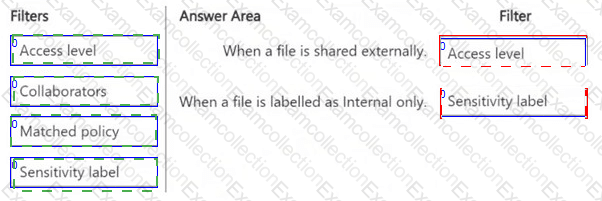
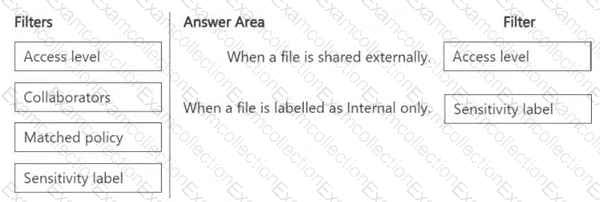
You have a Microsoft 365 E5 subscription that uses Microsoft Defender for Cloud Apps.
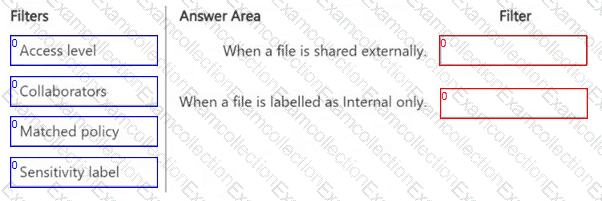
You plan to deploy a Defender for Cloud Apps file policy that will be triggered when the following conditions are met:
â— A file is shared externally.
â— A file is labeled as internal only.
Which filter should you use for each condition? To answer, drag the appropriate filters to the correct conditions. Each filter may be used once, more than once, or not at all. You may need to drag the split bar between panes or scroll to view content.
NOTE : Each correct selection is worth one point.
You have a Microsoft 365 subscription.
You need to customize encrypted email for the subscription. The solution must meet the following requirements.
â— Ensure that when an encrypted email is sent, the email includes the company logo.
â— Minimize administrative effort.
Which PowerShell cmdlet should you run?
You have a Microsoft 365 subscription.
You need to ensure that users can apply retention labels to individual documents in their Microsoft SharePoint libraries.
Which two actions should you perform? Each correct answer presents part of the solution.
NOTE: Each correct selection is worth one point.
Nate: This question is part of a series of questions that present the same scenario. Each question in the series contains a unique
solution that might meet the stated goals. Some question sets might have more than one correct solution, while others might
not have a correct solution.
After you answer a question in this section, you will NOT be able to return to it. As a result, these questions will not appear in the
review screen.
You implement Microsoft 365 Endpoint data loss prevention (Endpoint DLP).
You have computers that run Windows 11 and have Microsoft 365 Apps installed. The computers are joined to a Microsoft Entra tenant.
You need to ensure that Endpoint DLP policies can protect content on the computers.
Solution: You onboard the computers to Microsoft Defender for Endpoint.
Does this meet the goal?
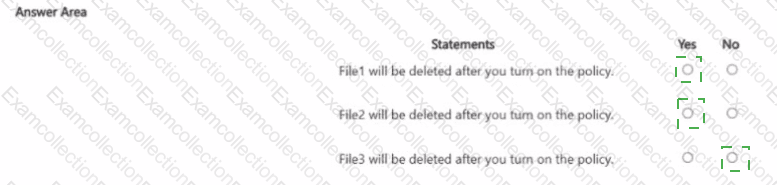
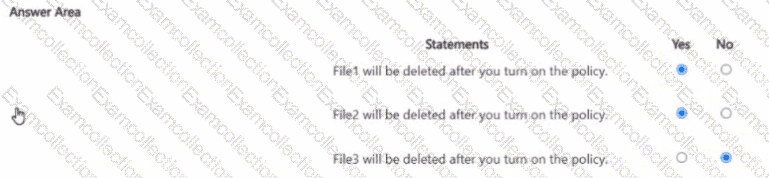
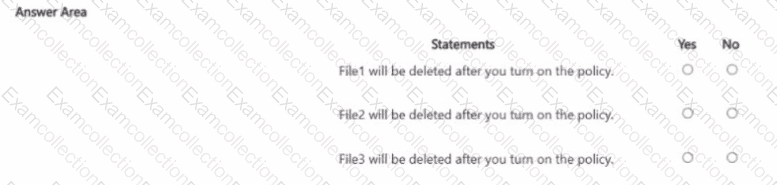
You have the files shown in the following table.
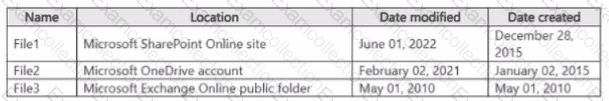
You configure a retention policy as shown > n the exhibit. (Click the Exhibit lab.)
The start of the retention period is based on when items are created. The current date is January 01. 207S.
For each of the following statements, select Yes if the statement is true. Otherwise, select No.
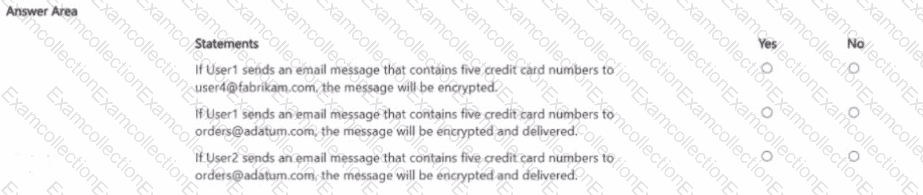
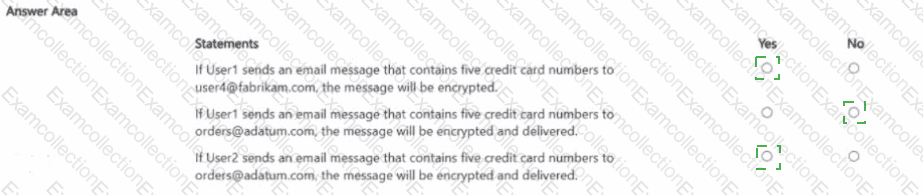
You have a Microsoft 36S subscription that contains the users shown in the following table.
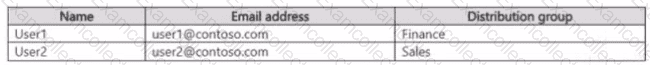
You create the data loss prevention (DLP) policies shown in the following table.
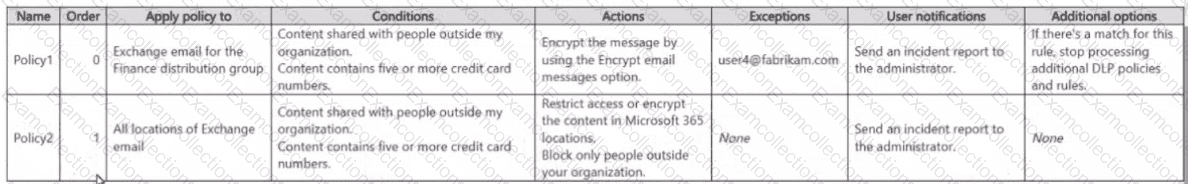
For each of the following statements, select Yes if the statement is true. Otherwise, select No.
NOTE: Each correct selection is worth one point.