Microsoft SC-900 - Microsoft Security Compliance and Identity Fundamentals
Select the answer that correctly completes the sentence.
Which Microsoft Purview data classification type supports the use of regular expressions?
Which Microsoft 365 feature can you use to restrict users from sending email messages that contain lists of customers and their associated credit card numbers?
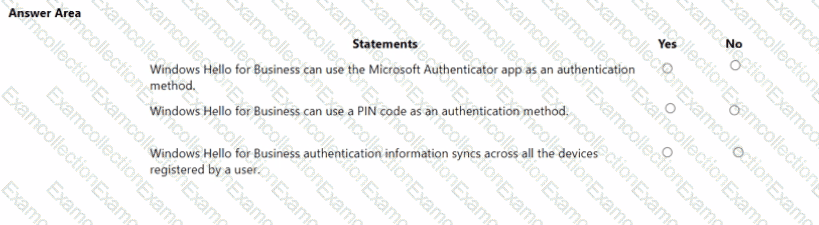
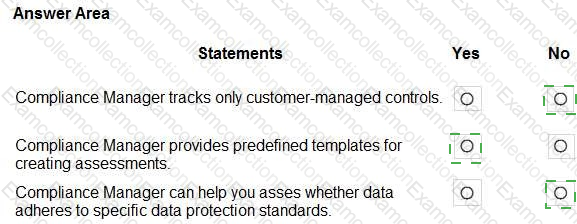
For each of the following statements, select Yes if the statement is true. Otherwise, select No. NOTE: Each correct selection is worth one point.
You company is evaluating various security products, including a security information and event management (SIEM) solution. You need to provide information about the functionality of SIEM solutions. What is a function of a SIEM solution?
Which Microsoft portal provides information about how Microsoft manages privacy, compliance, and security?
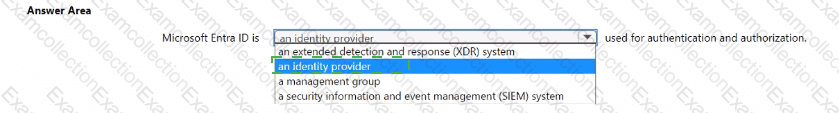
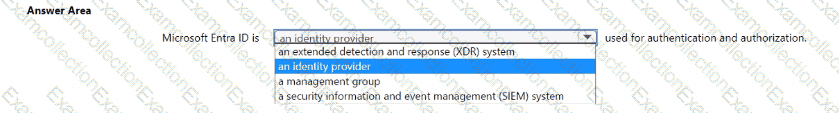
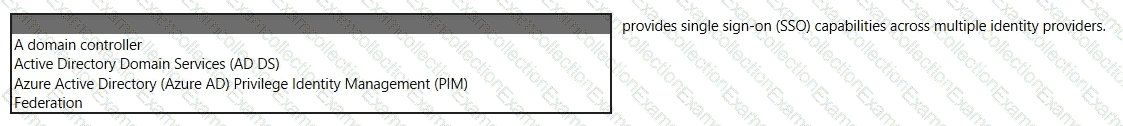
Select the answer that correctly completes the sentence.
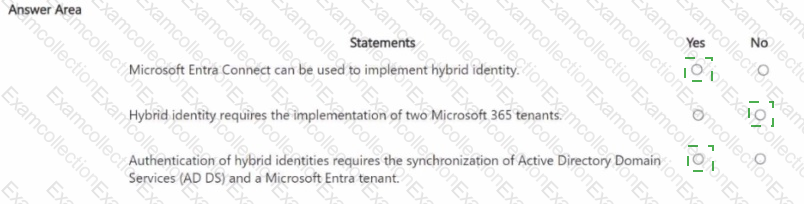
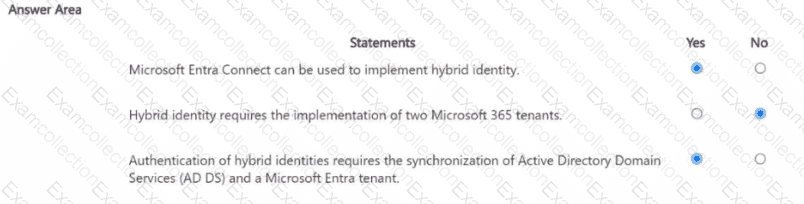
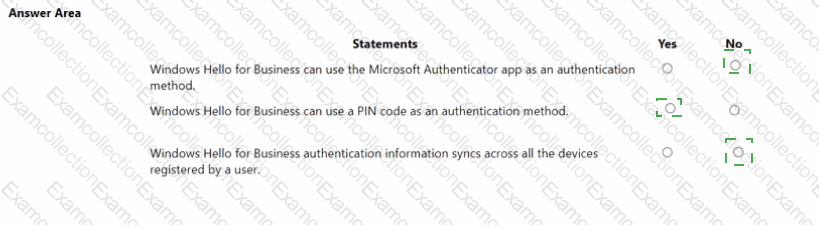
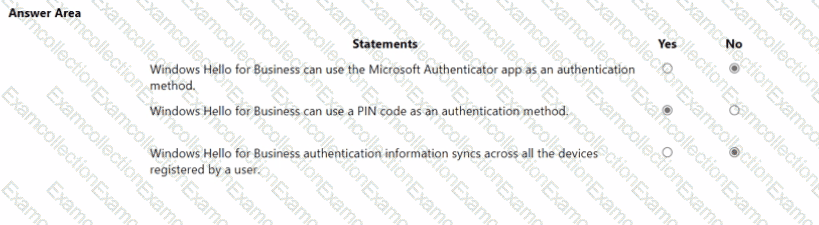
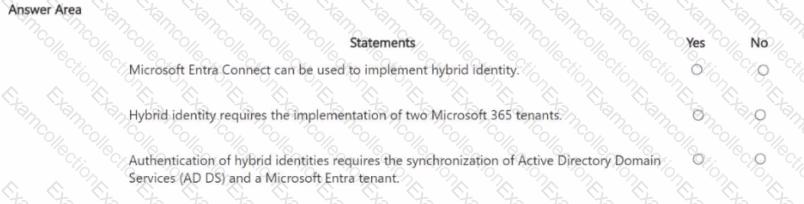
For each of the following statements, select Yes if the statement is true. Otherwise, select No.
NOTE: Each correct selection is worth one point.
You have an Azure subscription that contains multiple resources.
You need to assess compliance and enforce standards for the existing resources.
What should you use?
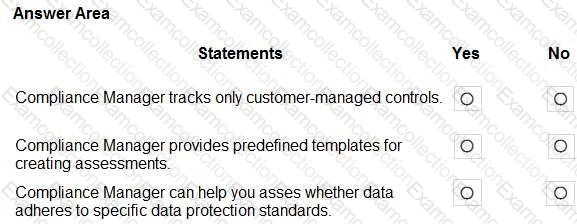
For each of the following statements, select Yes if the statement is true. Otherwise, select No.
NOTE: Each correct selection is worth one point.