Proofpoint TPAD01 - Threat Protection Administrator Exam
Which URLs are valid entries for the configuration shown in the screenshot?
How does TAP’s Message Defense feature work for unknown attachments?
What is the purpose of roles when assigning administrative access to Proofpoint Protection Server?
Pick the 2 correct responses below.
What is the difference between the Discard and Reject dispositions?
When reviewing the Audit Logs in the context of cluster monitoring, what type of information is primarily available?
You are using Smart Search within the PPS Admin UI to investigate the final disposition of a message. Smart Search shows the message is Quarantined/Discard to adqueue. How do you trace the message?
You log into the Protection Server and a rule you created yesterday is no longer enabled. Where can you find out what happened to the rule you created?
Refer to the exhibit below to see the interface used in this scenario.
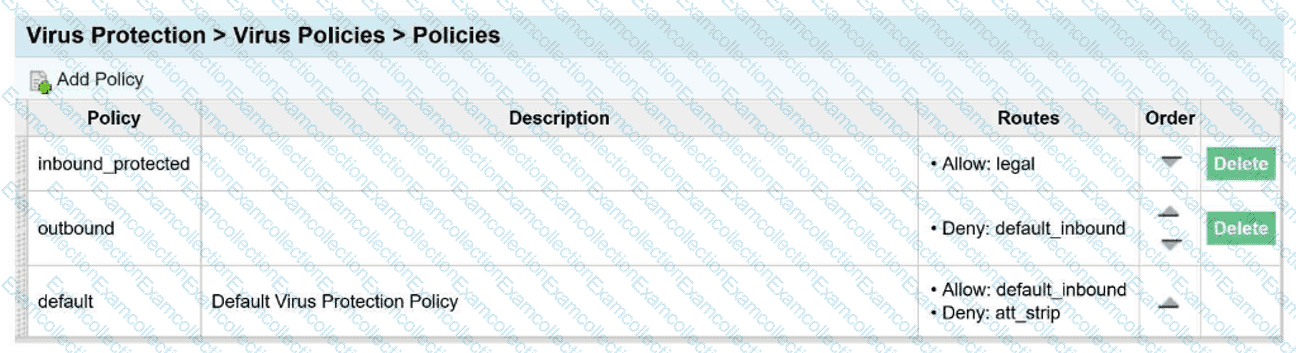
An email arrives inbound to the protection server, it is going to a single recipient and belongs
to the legal and default_inbound policy routes.
Which of the following is true regarding the virus policies?
You need to generate a report from the Cloud Admin Interface. What file formats are available to export?
When setting up an Import/Authentication Profile in PPS, which of the following is a required piece of information to connect to an LDAP server?



