Proofpoint TPAD01 - Threat Protection Administrator Exam
You are tasked with configuring outbound mail for an organization where an external domain has multiple MX records. Only one specific host is accepting mail. What is the best way to specify this specific hostname for outbound mail?
You are reviewing the MTA logs for a message that has been deferred. Which Delivery Status Notification (DSN) code indicates that the receiving server was temporarily unable to process the message?
Review the filter log exhibit.
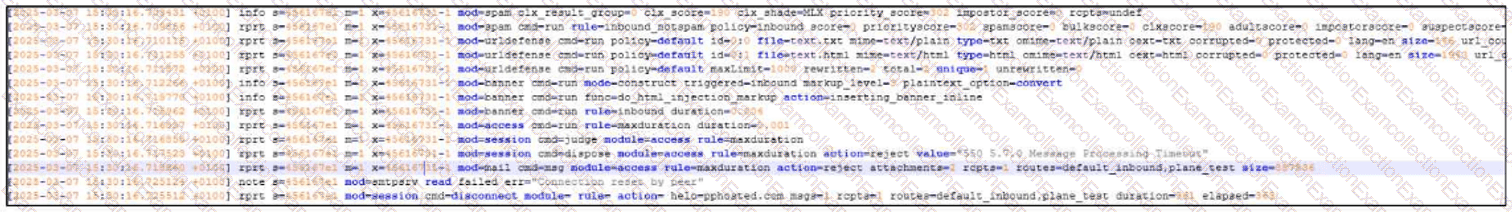
What two actions have taken place in the filter logs for this message?
What the exhibit shows clearly:
- URL Defense processing is present in the log
- A spam-related action/flag is present
Which of the following are true regarding Spam Detection?
Pick the 3 correct responses below.
During the configuration of an alert profile, which option is specifically required to ensure alerts are delivered to the appropriate individuals?
What are the three default methods available in Recipient Verification to verify that a recipient mailbox exists?
Pick the 3 correct responses below.
A SAML authentication profile is configured on the Proofpoint Protection Server console. Which portals can be accessed using this configuration?
What is the primary function of Cloud Threat Response (CTR)?
What is the primary purpose of the End User Web Interface in Proofpoint?
What is the main function of Threat Response Auto-Pull (TRAP)?



