Cisco 200-201 - Understanding Cisco Cybersecurity Operations Fundamentals (CBROPS)
What is the impact of encryption?
Which type of attack uses a botnet to reflect requests off of an NTP server to overwhelm a target?
An analyst must choose one source of information for further troubleshooting. A key requirement is to use low storage space over the next 12 months while being able to quickly determine the source and scope of an attack to effectively mitigate it. Which source of information should the analyst choose?
The security team has detected an ongoing spam campaign targeting the organization. The team's approach is to push back the cyber kill chain and mitigate ongoing incidents. At which phase of the cyber kill chain should the security team mitigate this type of attack?
Which attack method is being used when an attacker tries to compromise a network with an authentication system that uses only 4-digit numeric passwords and no username?
What is the difference between deep packet inspection and stateful inspection?
What is a description of a social engineering attack?
Refer to the exhibit.
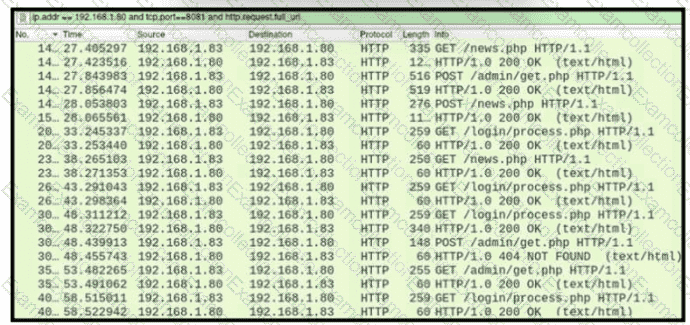
A network administrator is investigating suspicious network activity by analyzing captured traffic. An engineer notices abnormal behavior and discovers that the default user agent is present in the headers of requests and data being transmitted What is occurring?
What are two categories of DDoS attacks? (Choose two.)
Refer to the exhibit.
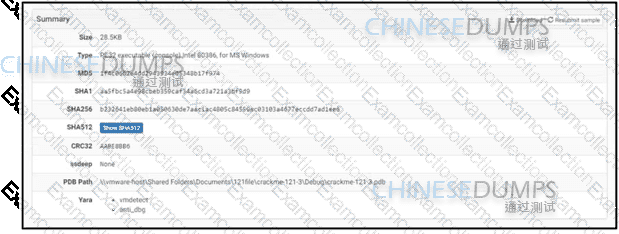
An engineer is reviewing a Cuckoo report of a file. What must the engineer interpret from the report?



