Cisco 300-215 - Conducting Forensic Analysis and Incident Response Using Cisco CyberOps Technologies (CBRFIR)
Rotor to the exhibit.
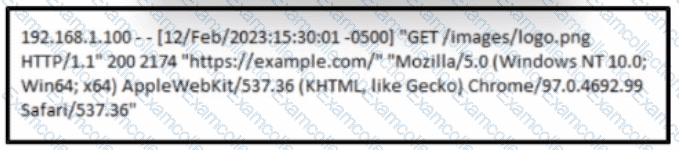
A cybersecurity analyst must analyst the logs from an Apache server for the client. The concern is that an offboarded employee home IP address was potentially used to access the company web server via a still active VPN connection Based on this log entry, what should an analyst conclude?
Refer to the exhibit.
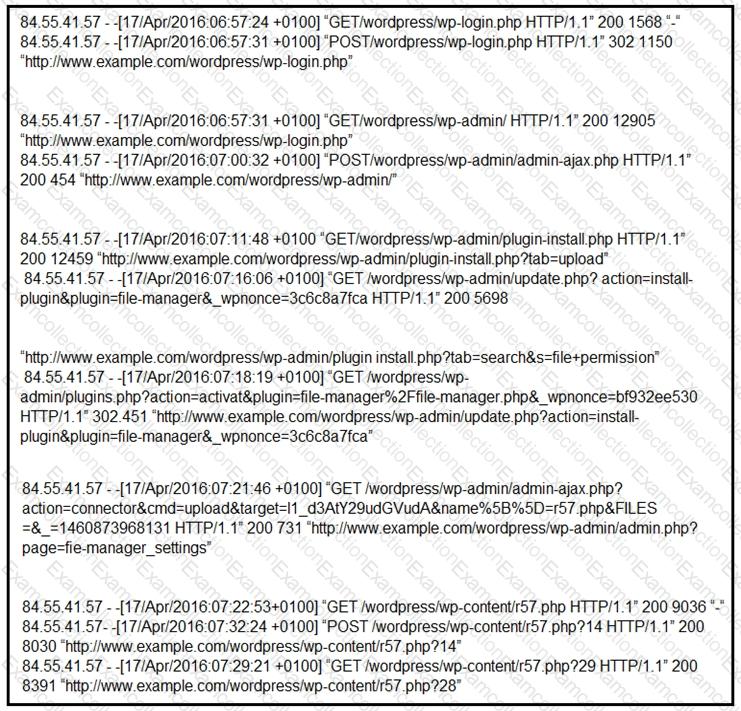
Which two determinations should be made about the attack from the Apache access logs? (Choose two.)
An attacker modifies a malicious file named TOPSECRET0523619132 by changing its file extension from a .png to a doc in an attempt to evade detection. Which technique is being used to disguise the file?
Refer to the exhibit.
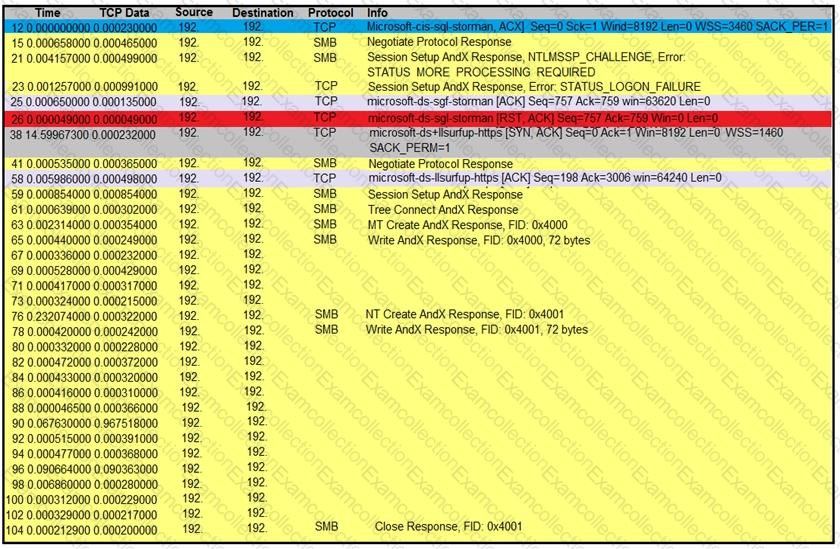
An engineer is analyzing a TCP stream in Wireshark after a suspicious email with a URL. What should be determined about the SMB traffic from this stream?
A cybersecurity analyst detects fileless malware activity on secure endpoints. What should be done next?
The Linux system administrator of a company suspects that physical unauthorized access was granted to a local Linux terminal. The administrator wants to examine the suspected machine for potential unauthorized use and to get information about even/ account in this terminal including when the password last changed The administrator logs in as a root user Which file should be examined to get the information?
During a routine inspection of system logs, a security analyst notices an entry where Microsoft Word initiated a PowerShell command with encoded arguments. Given that the user's role does not involve scripting or advanced document processing, which action should the analyst take to analyze this output for potential indicators of compromise?
A network host is infected with malware by an attacker who uses the host to make calls for files and shuttle traffic to bots. This attack went undetected and resulted in a significant loss. The organization wants to ensure this does not happen in the future and needs a security solution that will generate alerts when command and control communication from an infected device is detected. Which network security solution should be recommended?
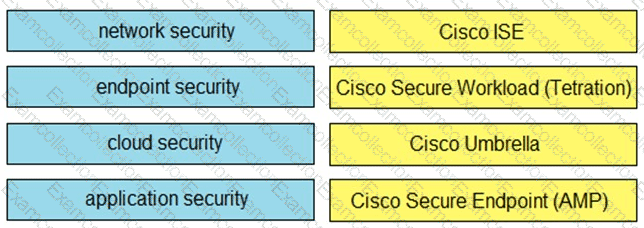
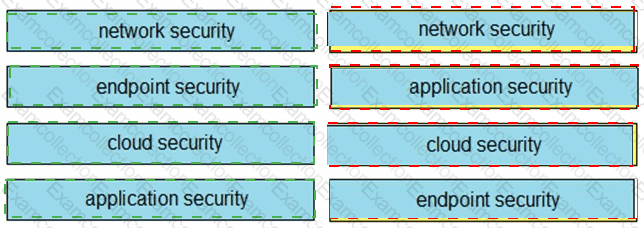
Drag and drop the capabilities on the left onto the Cisco security solutions on the right.