Cisco 300-215 - Conducting Forensic Analysis and Incident Response Using Cisco CyberOps Technologies (CBRFIR)
Refer to the exhibit.
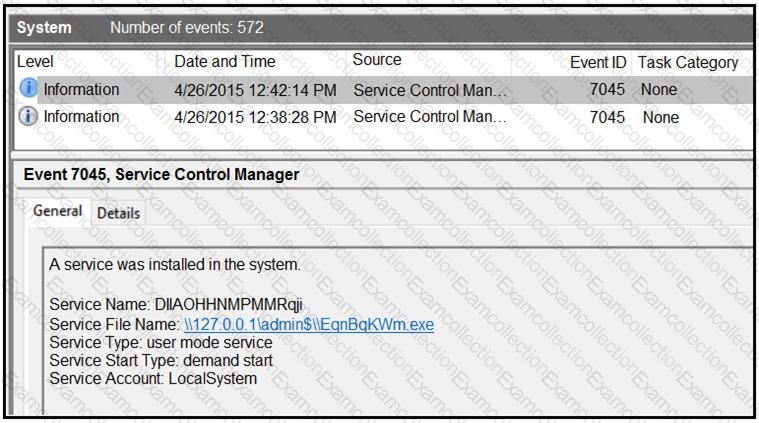
An HR department submitted a ticket to the IT helpdesk indicating slow performance on an internal share server. The helpdesk engineer checked the server with a real-time monitoring tool and did not notice anything suspicious. After checking the event logs, the engineer noticed an event that occurred 48 hours prior. Which two indicators of compromise should be determined from this information? (Choose two.)
Which two tools conduct network traffic analysis in the absence of a graphical user interface? (Choose two.)
Refer to the exhibit.
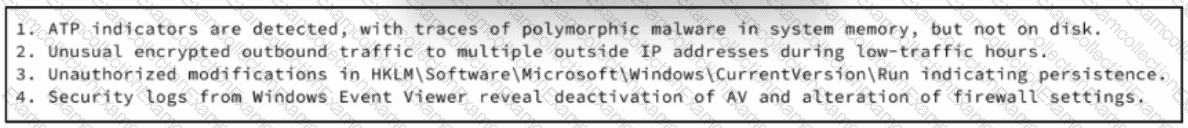
An experienced cybersecurity analyst is investigating a sophisticated suspected breach on a Windows server within an enterprise network and compiled the evidence gathered so far Which action should the analyst prioritize to understand the scope and impact of the breach?
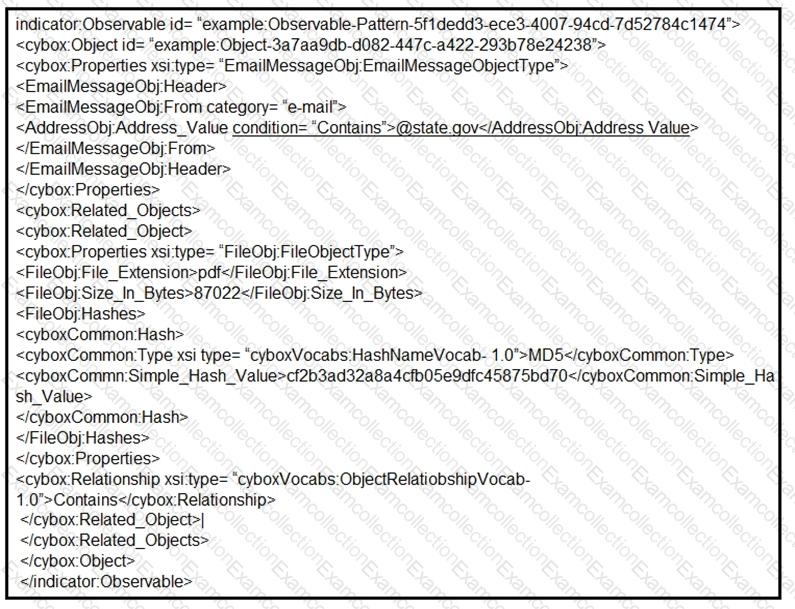
Refer to the exhibit.
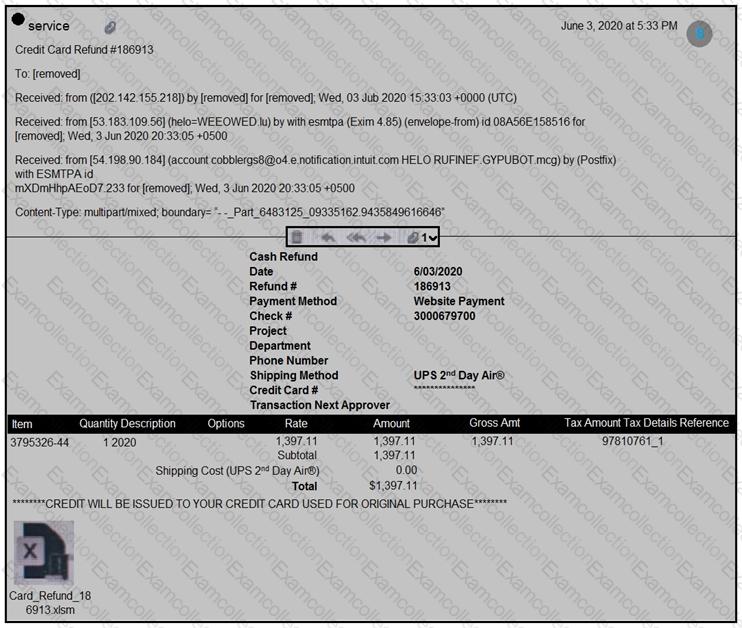
Which element in this email is an indicator of attack?
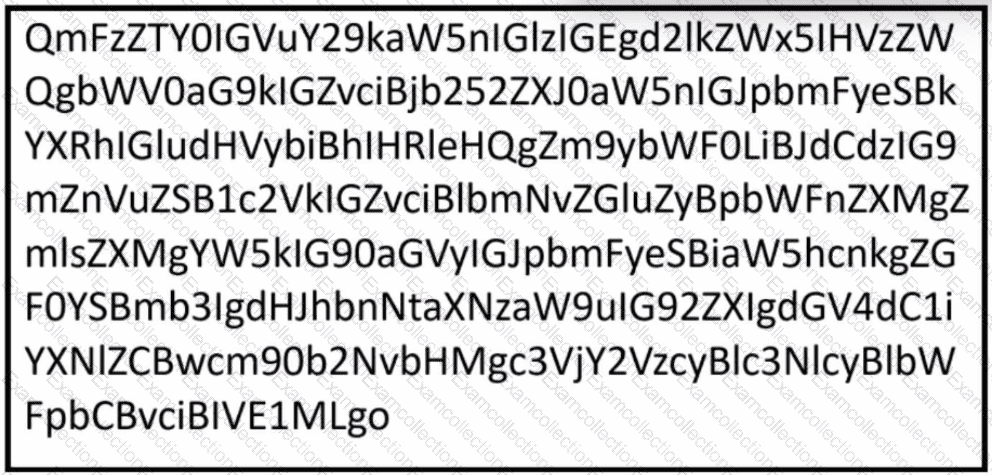
Refer to the exhibit.
Which encoding method is used to obfuscate the script?
Refer to the exhibit.
Which two actions should be taken as a result of this information? (Choose two.)
Over the last year, an organization’s HR department has accessed data from its legal department on the last day of each month to create a monthly activity report. An engineer is analyzing suspicious activity alerted by a threat intelligence platform that an authorized user in the HR department has accessed legal data daily for the last week. The engineer pulled the network data from the legal department’s shared folders and discovered above average-size data dumps. Which threat actor is implied from these artifacts?
Refer to the exhibit.
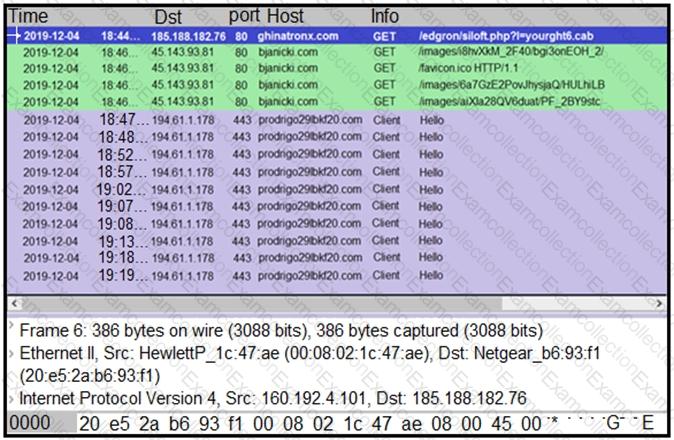
A network engineer is analyzing a Wireshark file to determine the HTTP request that caused the initial Ursnif banking Trojan binary to download. Which filter did the engineer apply to sort the Wireshark traffic logs?
An organization experienced a ransomware attack that resulted in the successful infection of their workstations within their network. As part of the incident response process, the organization's cybersecurity team must prepare a comprehensive root cause analysis report. This report aims to identify the primary factor or factors responsible for the successful ransomware attack and to formulate effective strategies to prevent similar incidents in the future. In this context, what should the cybersecurity engineer emphasize in the root cause analysis report to demonstrate the underlying cause of the incident?